Default Windows 10 Admin Password: Reset, Recover, and Secure
Learn how to securely reset and manage the default Windows 10 admin password. This step-by-step guide covers risks, best practices, and recovery options for end-users and IT admins.

This guide explains how to securely reset, recover, and manage the default windows 10 admin password. It covers local and Microsoft account scenarios, outlines why changing default credentials matters, and provides safe, auditable steps for end-users and IT admins. Always follow policy and vendor guidance when handling admin credentials to minimize security risk.
Understanding the risk of the default Windows 10 admin password\n\nWhen devices ship with a local administrator account or other admin credentials, the phrase default windows 10 admin password becomes a critical risk if these credentials are not changed or managed securely. The Default Password team emphasizes that unaltered admin passwords can provide attackers with a predictable entry point. Even if the device is used in a home or small business setting, careless handling of admin credentials can lead to data loss, unauthorized software installation, and lateral movement on a network. In practice, you should treat any default credential as a potential vulnerability until it is replaced with a strong, unique password and properly documented in your password policy. The key takeaway is simple: do not leave admin accounts exposed to publicly guessable or shared credentials. This insight aligns with security guidance from major publications and industry standards. According to Default Password, documenting who has admin access and when credentials were changed is essential for ongoing governance. The goal is clear: minimize risk by enforcing least privilege and regular credential rotation, even on individual devices.
Why changing default credentials matters\n\nSecurity researchers consistently warn that default or weak admin passwords are a primary attack vector. If an attacker learns the admin password, they can disable security features, install malware, or exfiltrate sensitive data. From a governance standpoint, organizations should enforce a policy of rotating admin credentials at defined intervals and after events such as personnel changes or device reassignment. The emphasis is on auditable procedures: who changed the password, when, and under which approval. Default Password analysis shows that many users still operate devices with unchanged admin credentials after setup, which is a risk for both personal data and enterprise networks. By implementing a password change protocol, you reduce the chance of credential stuffing, brute-force attempts, and insider threats. This section reinforces that secure administration starts with disciplined password hygiene and clear ownership.
Preparations before password reset\n\nBefore you reset the Windows 10 admin password, gather the essentials: verify your admin rights, locate the target account, and identify the recovery path available on the device. If you rely on a Microsoft account to sign in, ensure you have access to the linked email or phone for verification. If you use a local account, confirm you can boot into a recovery environment or another admin account. Plan for potential data loss if the reset involves reinstallation or disk reformat, and ensure you have backups or a password reset disk ready if applicable. This preparation reduces downtime and avoids accidental data loss. The preparation phase is also a good moment to review your organization’s password policy and document the steps you will take during the reset.
Methods to reset or recover the Windows 10 admin password\n\nWindows 10 provides several legitimate, supported paths to regain access to an admin account. First, use the Microsoft account recovery flow if the device is tied to a Microsoft identity; this typically restores access without data loss. Second, if a local account is used and a password reset disk exists, you can boot to the Windows recovery environment and use that disk to reset the password. Third, for devices that allow it, enabling the built-in Administrator account from Safe Mode can provide an interim admin path to reset other accounts. Finally, when all else fails, professional IT support or device replacement may be necessary, especially in managed environments where policies restrict local resets. Throughout, avoid destructive actions like reformatting without explicit backups. The overarching principle is to use official recovery options first and only escalate when you have confirmed backups and organizational authorization.
Security improvements and policy considerations\n\nPost-reset, update security configurations to prevent recurrence of the issue. Disable or rename the built-in Administrator account after you regain access, enable two-factor authentication where possible, and enforce strong password policies across all admin accounts. Document the password change event with a timestamp and the responsible operator. Consider implementing centralized password management or a password vault to reduce reliance on static local credentials. Regularly review admin accounts to ensure the principle of least privilege is upheld and that access is revoked promptly when personnel change roles. This approach aligns with standards from government and industry bodies that emphasize auditable access controls and proactive credential management.
Common mistakes to avoid\n\nCommon mistakes include using weak passwords, reusing credentials across systems, and neglecting to update contact or recovery information. Another frequent error is failing to disable legacy admin accounts after password recovery, which leaves a backdoor for attackers. Do not rely on one-off resets as the sole security measure; pair resets with policy-driven controls like MFA, device encryption, and routine credential audits. Finally, never bypass security controls or seek unofficial methods to recover access; these actions may violate laws, policies, and vendor terms. Following official procedures, backed by evidence-based guidance from trusted sources, keeps administration both effective and compliant. The ultimate objective is to ensure that admin credentials remain confidential, auditable, and appropriately restricted.
AUTHORITY SOURCES\n\n- https://www.nist.gov\n- https://www.cisa.gov\n- https://support.microsoft.com
Tools & Materials
- PC or laptop with Windows 10(Must be bootable to access recovery options if needed)
- Administrative access to the device(One or more admin accounts to perform password changes)
- Password reset disk or recovery media(Only if previously created and used for local account resets)
- Microsoft account credentials (optional)(Needed if the device uses a Microsoft account to sign in)
- Backup of important data(Prevents data loss if reset requires reconfiguration)
Steps
Estimated time: 30-60 minutes
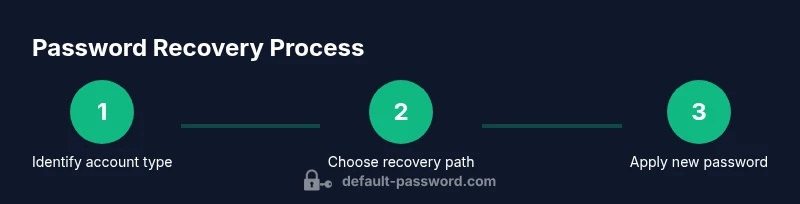
- 1
Identify account type
Determine whether the admin access is via a local account or a Microsoft account. This will dictate which recovery path is available and minimize unnecessary steps.
Tip: If you are unsure, check the sign-in screen to see whether a Microsoft account email appears or if there is a local username. - 2
Prepare recovery options
Gather credentials and ensure you have backup data. If a password reset disk exists, locate it; if not, verify that you can access Microsoft account recovery options or a second admin account.
Tip: Have a backup plan in case the primary recovery path fails. - 3
Boot to recovery environment
Restart the device and boot into Windows Recovery Environment or Safe Mode with Networking, depending on your chosen path. This step enables you to access password reset tools safely.
Tip: If the device is locked, use the power + shift method to reach recovery options. - 4
Reset the admin password
Use the appropriate recovery option (Microsoft account, local password reset disk, or Safe Mode Administrator method) to set a new password for the admin account. Confirm the new password and test sign-in.
Tip: Choose a strong, unique password and avoid common phrases. - 5
Secure the account post-reset
Disable or rename the built-in Administrator if possible, enable MFA where available, and ensure audit logging is enabled for later review.
Tip: Document the change with date, time, and responsible administrator. - 6
Verify access and update policies
Sign in with the admin account to confirm access works, then review local security policies and update password-management guidelines to prevent similar issues.
Tip: Run a quick security scan to verify no malware presence after the reset.
Your Questions Answered
What is considered the 'default' Windows 10 admin password?
There is no universal default password for all Windows 10 devices. The admin credential approach varies by device, edition, and whether a Microsoft account is used. Treat any default credential as a vulnerability until you change it and document the change.
There isn't a universal default password. Admin credentials vary by device, so treat any default as a vulnerability until you change it and document the update.
Can I recover a Windows 10 admin password without data loss?
Yes, often you can recover access using official recovery options such as a Microsoft account or a locally created password reset disk. If those options aren’t available, data loss prevention requires careful handling, backups, and possibly professional support.
Yes, official recovery options exist like Microsoft account recovery or a reset disk. If those aren’t available, contact support to avoid data loss.
Is it safe to disable the built-in Administrator account after recovery?
Yes. Disabling or renaming the built-in Administrator reduces the attack surface. Use a standard admin account for daily tasks and reserve the built-in account for recovery only when needed.
Yes. Disable or rename the built-in Administrator to reduce risk; use a standard account for daily tasks.
What should I do if I forgot the Microsoft account password used to sign in?
Follow Microsoft's account recovery process to regain access. If you can't recover the account, consider alternative admin accounts or device reset options with data backup.
If you forgot your Microsoft account password, use Microsoft’s recovery process or contact support for options.
What are best practices for admin password management in teams?
Adopt a password manager, enforce MFA for admin accounts, rotate passwords on a schedule, and maintain an access review. Document who has admin rights and limit the number of admins to reduce risk.
Use a password manager, enable MFA, rotate regularly, and review who has admin rights.
Where can I find official guidance for Windows password management?
Consult authoritative sources such as Microsoft support, NIST guidelines, and CISA best practices. These sources provide policy-level guidance and practical steps for credential security.
Check Microsoft support and recognized standards bodies like NIST and CISA for credential security guidance.
Does resetting the admin password affect user data on the device?
In standard recovery scenarios, user data remains intact. Some advanced reset methods could require reconfiguration, so always back up critical data beforehand.
Usually, user data stays intact, but always back up before performing resets.
What if the device is part of a corporate network?
Follow your organization's ITIL processes and obtain approvals before changing admin credentials. In many cases, centralized password management and a helpdesk workflow are required.
For corporate devices, follow your IT policy and use approved workflows to change admin credentials.
Watch Video
Key Takeaways
- Identify account type before resetting to choose the correct path
- Always back up data before credential changes
- Treat admin credentials as sensitive and rotate them regularly
- Disable or rename the built-in Administrator after reset when possible
- Record changes for compliance and future reference