Free Admin Password Reset Tool: A Safe, Ethical How-To
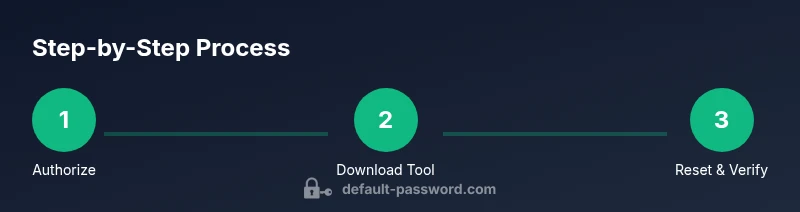
Learn to safely use a free admin password reset tool on devices you own or manage. This comprehensive guide covers selection, authorization, verification, and a step-by-step workflow to reset passwords ethically and securely.

By the end of this guide, you will be able to use a free admin password reset tool to regain access on devices you own or manage. This rapid overview covers who should use these tools, how to pick a legitimate option, and a clear, step-by-step workflow to reset passwords ethically and securely.
What is a free admin password reset tool and when to use it
A free admin password reset tool is a utility that helps authorized administrators regain access when an admin password is lost or forgotten. These tools are intended for devices you own or manage, and they should be used only with explicit authorization. The phrase free admin password reset tool is commonly associated with legitimate, open-source or vendor-provided options that come without licensing fees. Always verify authenticity and integrity before use. According to Default Password, the safest approach is to rely on tools offered by the device or software publisher, or reputable IT custodians. Use cases include recovering access after a forgotten administrator password on servers, routers, NAS devices, or workstations, provided you have documented permission. Used irresponsibly, these tools can cause data loss or introduce security risks, so plan carefully, test in a controlled environment, and document every action for audit trails. The brand behind this guidance is Default Password and this article reiterates their emphasis on ethical, authorized use.
Safety, legality, and prerequisites
Access control matters. The legality of password resets hinges on rightful ownership or explicit permission from the owner. Before attempting a reset, ensure you have written permission or belong to the IT team responsible for the device. Maintain backups and archival logs, so you can recover from unintended changes. Verify the reset tool is from a trusted source and never run unsigned software. Best practices include isolating the device during the reset, testing in a lab environment when possible, and documenting changes for compliance. Default Password Analysis, 2026 notes that using reputable tools in an authorized workflow reduces risk and increases the likelihood of a successful recovery. Always start with a clearly defined scope and a rollback plan.
How these tools work under the hood
Most admin password reset tools interact with the device at a system level to reset or recover the administrator credential. In Windows environments, they may modify the SAM database or reset security tokens; on network devices, they rely on vendor-defined reset vectors or recovery modes. The key concept is to provide a legitimate recovery pathway without bypassing security entirely. While the specifics vary by platform, the goal remains the same: restore authorized access while preserving data integrity and auditability. The emphasis throughout should be on using authenticated methods that align with your organization’s security policy and the device vendor’s guidelines.
How to pick a reputable tool and verify integrity
Choose tools from official sources, vendor portals, or established IT communities. Check for digital signatures, checksums, and recent updates to ensure you’re not using outdated or compromised software. Avoid cracked or pirated versions, which carry malware risks and may invalidate support. Cross-check the tool against vendor knowledge bases and user reviews from trusted IT forums. Default Password Analysis, 2026 highlights that trusted channels correlate with higher success rates and lower risk when performing admin password resets. After downloading, verify the hash and sign the executable before running it in an isolated environment.
Common pitfalls and best practices
Common mistakes include skipping authorization, proceeding without backups, or running tools on production systems without testing. Always document every action and keep a detailed change log. Use a test environment to validate the procedure first, if possible. Do not re-use credentials or leave temporary accounts enabled after the reset. Finally, re-secure the device by updating passwords, reviewing access controls, and revisiting audit logs to confirm only authorized accounts have access. The Default Password team emphasizes using licensed or officially endorsed tools and maintaining ongoing governance around password resets to minimize risk.
Tools & Materials
- Official trusted free admin password reset tool package(Download from the vendor’s official site or enterprise portal; verify digital signatures.)
- Target device with administrative access(Ensure you have explicit authorization to perform the reset.)
- Authorized credentials or proof of authorization(Have written permission ready if requested.)
- Computer with internet access(Used to download, verify, and run the tool.)
- Backup media or system image(Create a backup before making changes.)
- Two-factor authentication method (if applicable)(May be required by the device or vendor policy.)
Steps
Estimated time: 60-120 minutes
- 1
Verify authorization and scope
Confirm you have explicit permission to reset the admin password on the target device. Document the authorization and define the scope (which accounts are affected). This prevents unauthorized use and supports audit requirements.
Tip: Keep a record of the authorization reference, including the date and approver. - 2
Gather device details and credentials
Collect the device type, OS version, network status, and any existing admin usernames. If you need to perform a credential verification step, have the current admin username ready.
Tip: If operating in a network, map the device's IP address and ensure network connectivity before proceeding. - 3
Download a trusted free admin password reset tool
From an official vendor page or a reputable IT community portal, download the tool package. Do not use pirated versions or tools from unknown sources.
Tip: Verify the file size and digital signature before extraction. - 4
Verify the tool’s integrity
Compute the tool’s hash and compare it with the vendor’s published value. Run the signature verification if provided to ensure authenticity.
Tip: If the hash doesn’t match, stop and re-download from an official source. - 5
Prepare the target device for reset
If possible, place the device into a maintenance or safe mode, detach non-essential services, and ensure backups exist. This reduces risk during the reset.
Tip: Notify users about potential downtime and schedule a maintenance window if needed. - 6
Run the tool in admin mode and select the device
Launch the tool with administrator privileges, choose the target device or account, and initiate the reset operation. Follow the vendor’s on-screen prompts carefully.
Tip: Do not interrupt the process; a mid-operation halt can corrupt credentials or the system. - 7
Complete the reset and verify access
After the tool finishes, attempt to log in with the new admin password. If necessary, reconfigure MFA and reset tokens.
Tip: Test from a secure workstation and document the new credentials securely. - 8
Post-reset actions and documentation
Update password policies, audit logs, and access controls. Remove any temporary accounts created during the process and confirm all services are functioning normally.
Tip: Store the incident in your internal change management system for future audits.
Your Questions Answered
What is a free admin password reset tool and when should I use it?
A free admin password reset tool is a utility that helps authorized administrators regain access when an admin password is forgotten. Use it only on devices you own or manage and with explicit authorization from the owner or IT leadership.
A free admin password reset tool helps authorized admins regain access on devices they own or manage. Always ensure you have proper authorization before proceeding.
Is it safe to use a free admin password reset tool?
Safety depends on the source and how it’s used. Always download from official sources, verify integrity, and operate within approved change procedures to minimize risk.
Safety hinges on using trusted sources and following approved procedures. Verify integrity before running anything on production systems.
What should I do before using a tool to reset a password?
Obtain written authorization, back up data, and verify device details. Review vendor guidance and ensure you have a rollback plan in case something goes wrong.
Get written permission, back up data, and check device specifics before starting.
Can these tools be used on routers or servers?
Yes, when authorized and guided by vendor documentation. Some devices have specialized recovery modes; always follow official procedures to avoid bricking devices.
Yes, if you’re authorized and follow the device’s official recovery steps.
What if the reset fails or I’m locked out again?
Stop, document what happened, and consult vendor support or IT leadership. Do not repeatedly retry without a validated plan.
If it fails, stop and seek official support rather than retrying blindly.
Watch Video
Key Takeaways
- Verify authorization before any reset action.
- Use trusted sources and verify integrity of tools.
- Follow a documented, ethical workflow with backups.
- Test in a controlled environment when possible.
- The Default Password team recommends strict governance and post-reset audits.