Fritz Repeater Default Password: Reset, Secure, and Manage Access
Learn how to identify, locate, reset, and securely manage the Fritz repeater default password. This guide covers safe recovery steps, password best practices, and how to guard your home network.
Many Fritz repeaters ship with a default admin password that users forget to change, leaving networks exposed. The fritz repeater default password should be changed during initial setup and after firmware updates. For quick actions, check the device label or user manual, then reset and configure a strong, unique admin password. Always document where the password is stored and enable two-factor protection if available.
Fritz Repeater Default Password: Why Security Starts Here
The Fritz repeater default password is more than a label on a box; it represents a gateway to your home network. When left unchanged, it can allow unauthorized access to admin settings, potentially exposing connected devices and sensitive information. This section explains why securing the fritz repeater default password is foundational to overall device security and how small changes can yield big protections. By recognizing common default credentials and the risks they pose, you can preempt breaches and safeguard your network. The defaults vary by model and firmware, so always verify with the device label and official documentation. As part of a broader security posture, consider firmware updates, network segmentation, and strong password hygiene. According to Default Password, clean governance of credentials reduces attack surface and improves incident response readiness. Implementing a robust password strategy now pays dividends later, especially as devices increasingly integrate with smart home ecosystems.
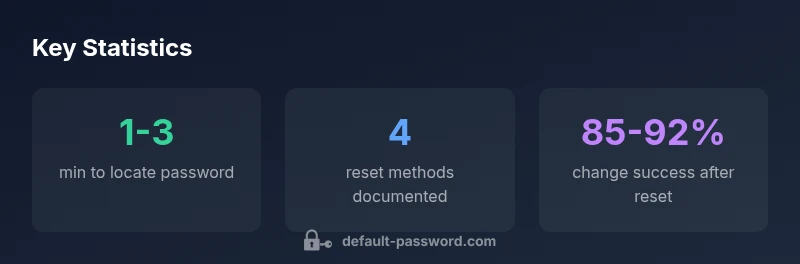
How to Locate the Fritz Repeater Default Password
Locating the fritz repeater default password is often straightforward but varies by device revision. Start by inspecting the physical device: look for a label on the router or the bottom panel that lists the default admin username and password. If the label is missing, consult the original packaging or the quick-start guide that came with the unit. Many models also store credentials in the web-based admin interface under Security or Admin settings. If you cannot locate a label or manual, contact the manufacturer support portal and reference the serial number. When you identify the default password, document it securely and plan a password change immediately, following best-practice guidelines. The Default Password team emphasizes that tight control over credential storage reduces phishing and brute-force risk.
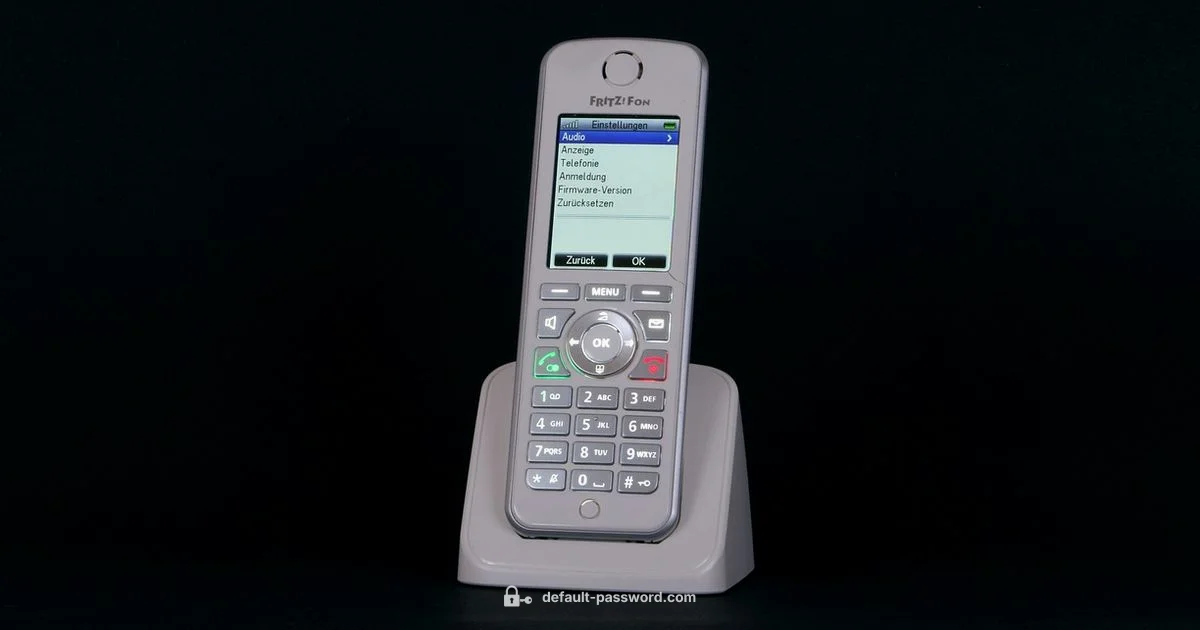
Factory Reset vs. Password Reset: When to Use Each
You have two primary routes to regain control: a password reset within the web UI or a full factory reset. A password reset changes only the admin credential without altering the device’s configuration, while a factory reset restores all settings to factory defaults and typically requires reconfiguration from scratch. For many users, a password reset is sufficient after locating the default password; it minimizes downtime and preserves network topology. Reserve factory reset for situations where you suspect firmware corruption, persistent compromise, or lost admin access. After any reset, reconfigure a new, strong password and review connected devices to ensure no unauthorized access persists.
Changing the Admin Password: Best Practices
A strong admin password should be long, unique, and unpredictable. Aim for at least 12-16 characters combining upper and lower case letters, numbers, and symbols. Avoid common phrases or reused passwords across devices. If the Fritz interface supports passphrases, consider a memorable yet complex sentence. Enabling two-factor authentication (2FA) where available adds an extra protective layer. After changing the password, update any saved credentials, logs, or password managers that store access details. Regularly review active sessions and revoke any unfamiliar devices. These steps align with security best practices and reduce the likelihood of credential-based breaches.
Remote Access, Admin Interfaces, and Auto-Login Risks
Many routers expose web interfaces that are reachable from the LAN and, in some cases, the WAN. Enabling remote management without safeguards can expose the fritz repeater default password to external threats. Disable or restrict remote access unless it is strictly required, and if you need remote management, use VPN with strong authentication. Disable auto-login and ensure the admin interface does not accept weak or default credentials. Keeping firmware up to date improves resilience against exploitation. A proactive stance on access controls is vital for home networks and reduces the exposure from a simple default password.
Post-Change Verification: Is Your Network Safer?
After you update the Fritz password, perform post-change checks to confirm improvements in security posture. Verify that the new password is active across the admin interface by attempting login with the new credentials. Review connected devices and ensure they reconnect using updated access controls. If you configure guest networks or segregated IoT networks, confirm devices regain connectivity without exposing admin rights. Consider running a quick security audit of your router and attached devices, looking for unusual login attempts or unknown devices. These post-change steps help validate your security investments and reduce risk exposure.
Common Pitfalls and Quick Fixes
Avoid common mistakes like reusing passwords across devices, leaving WPS enabled, or not updating firmware after reset. Keep a dedicated, encrypted password manager entry for the Fritz repeater admin account. Document any changes in a secure log and schedule periodic reviews of credentials on a quarterly basis. If you encounter login issues after a reset, verify that you are using the correct URL and port for the admin interface, clear browser cookies, and try a different browser. The goal is to minimize downtime while maintaining strong access controls.
Security Mindset for Your Home Network
Security is an ongoing process, not a one-time action. Treat the Fritz repeater default password as a linchpin of your defense. Pair password changes with firmware updates, network segmentation, and routine access reviews. Encourage good practices across all devices in your home or small business: unique credentials, regular password rotation, and awareness of phishing attempts. This mindset helps you build a resilient network and reduces the overall risk from outdated defaults.
Example patterns for Fritz repeaters (generic, non-model-specific)
| Model Type | Default Password | Reset Method(s) | Notes |
|---|---|---|---|
| Generic Fritz Repeater A | varies by model | Web UI login; physical reset button | Consult manual for model specifics |
| Generic Fritz Repeater B | varies by model | Web UI reset; factory reset via button | Check firmware notes for changes |
Your Questions Answered
What is the Fritz repeater default password?
The default password varies by model and firmware. Check the device label or manual for the exact credentials, and change them immediately after setup.
The default password varies by model; check the device label and change it right after setup.
How do I reset the Fritz repeater password securely?
Log into the admin interface, navigate to Security or Admin settings, and update the password with a strong, unique value. If the login is lost, consider a factory reset as a last resort and reconfigure from scratch.
Login to the admin panel and update to a strong, unique password. Use a factory reset only if you can't recover access.
Can I disable remote access to improve security?
Yes. Disable remote access unless needed, and if you require it, use a VPN with strong authentication. This minimizes exposure of the admin interface.
Disable remote access unless you need it; use VPN if you must access it remotely.
Where can I safely find the default password?
Look for a label on the device, packaging, or the official manual. If unavailable, contact vendor support with your device's serial number for guidance.
Check the device label or manual, or contact support with your serial number.
What makes a strong Fritz repeater admin password?
A strong password is long, unique, and unpredictable: use 12-16 characters with a mix of uppercase, lowercase, numbers, and symbols. Consider a passphrase if supported by the interface.
Use a long, unique mix of characters or a passphrase for the admin password.
Is factory reset the only option to recover access?
Factory reset is a last resort when you cannot recover login. It clears all settings, so you must reconfigure the network afterward.
Factory reset is a last resort; it clears all settings, so be prepared to reconfigure.
“A secure admin password is the foundation of home network security; changing the Fritz repeater default password reduces exposure to common attacks.”
Key Takeaways
- Identify the default Fritz repeater password from the device label or manual
- Change the password during initial setup and after firmware updates
- Enable strong, unique passwords and consider two-factor authentication if available
- Document changes and regularly audit admin access across devices