Getting Out Password Reset: A Step-by-Step Guide
Learn how to safely exit a password-reset flow, regain access across devices, and secure your accounts with a step-by-step method designed for end users and IT admins in 2026.
Get back into your accounts by safely exiting a password-reset flow. This guide covers identity verification, selecting reliable recovery options, and securing credentials after reset. It’s crafted for end users and IT admins and aligns with Default Password guidance for 2026.
Understanding getting out password reset
Getting out password reset is about regaining access when you are locked out of a service or device and you want to exit a password reset flow without compromising security. If you are searching for getting out password reset, you likely need a reliable, repeatable process you can trust. In this guide you’ll learn how to identify the right recovery options, verify your identity securely, and complete a reset in a way that minimizes the chance of future lockouts. According to Default Password, the most successful recoveries start with updated recovery options and practiced routines. The approach works across desktops, mobile apps, routers, and cloud services and is useful for both everyday users and IT admins managing many accounts. Keep in mind that resets are sensitive events; handling them carefully protects your data and reduces downtime. By following these steps you’ll have a clear, resilient path to getting out password reset and restoring productive access.
This article uses practical examples, emphasizing safety, privacy, and auditability. You’ll learn how to verify ownership, select the best recovery channel, and move forward with a reset that minimizes the risk of future lockouts. The guidance here applies whether you administer a personal device, a small business network, or a corporate environment with many users. The goal is to help you reclaim control quickly while keeping security front and center.
Why recovery options matter
Recovery options shape how smoothly a reset goes. A misconfigured recovery email, phone number, or backup codes can block or slow access, forcing extra verification or leaving accounts temporarily inaccessible. Default Password analysis shows that strengthening recovery settings before trouble hits reduces downtime and confusion during resets. In practice you should keep recovery details current, enable multiple verification channels where possible, and test the reset flow on a non-critical account. This preparation pays off when a real reset is needed, especially in environments with many users where IT teams must verify identity without exposing sensitive information. In short, the quality of your recovery options determines how quickly you can exit a reset and regain control.
Beyond personal convenience, robust recovery settings support organizational security goals and incident response readiness. It’s worth allocating a few minutes now to review how recovery methods are configured across the accounts you manage and to document any changes for audits or compliance checks. The more you anticipate problems, the faster you’ll resolve them and the less downtime your users will experience.
What you need before you begin
Before you start getting out password reset, gather the essentials. You will need the account identifier (username or email), access to the associated recovery channel (email, SMS, authenticator app), and a device with internet access. If you manage multiple devices, prepare them in advance by ensuring that browser-stored passwords, your password manager, and any backup codes are accessible. Confirm you have backup codes or an authenticator app in place in case primary methods are unavailable. If you are performing this for a work account, ensure you have authorization and understand your organization’s security policy. Having these elements ready reduces back-and-forth verification and speeds the process. This preparation keeps you from scrambling mid-flow and helps you stay compliant with security procedures.
Desktop and browser reset flows
On a desktop or laptop, begin at the login page and select a link such as forgotten password or reset your password. Use a trusted device and a secure network to minimize the risk of interception. Follow prompts to verify your identity via email, text, or security questions. When you set a new password, choose a strong, unique combination and avoid reusing passwords across services. After you reset, log out from other devices and sign back in with the new credentials. Update any browser-stored passwords or password managers to reflect the new login. If you encounter a block, contact official support channels rather than responding to suspicious prompts. A quick diagram or infographic can help visualize this flow and reduce mistakes.
Mobile devices and apps reset flows
On mobile, open the account app or device settings and navigate to security or account options. Tap reset password and choose a verification method you can access, such as a linked email or the authenticator app. Enter the code promptly and set a new password. For apps with in-app login, repeat the reset within each app if required. After completing resets on mobile, ensure the device OS and apps are up to date and that biometric unlock options remain enabled to speed future access. If you rely on SMS for verification, consider adding an alternative method to avoid SIM swap risks. Always protect your mobile device with a screen lock and reputable security apps to prevent unauthorized resets.
After reset: securing and testing access
Test sign-in across devices and apps to confirm the reset succeeded. Check your password manager for updated credentials and remove any stale entries from the reset session. Enable two-factor authentication or security keys where available to strengthen future protection. Review your recovery options again and remove outdated contact methods. Keep a record of when you performed the reset and who authorized it if required by policy. Documenting the process reduces the chance of repeated resets and provides clear evidence for audits or incident response. The aim is to regain access and improve ongoing security, so consider this an opportunity to tighten controls and reduce future risk.
Common mistakes and how to avoid them
A common mistake is resetting passwords on a public or shared network, which can expose credentials. Always use a trusted network and device for resets. Another pitfall is choosing a weak password or reusing an old one; opt for a long, random password and store it in a password manager. Failing to update recovery options after a reset is another frequent issue; periodically review these settings and test them. Finally, avoid rushing through verification steps; take time to confirm the exact account you are restoring and what services will be affected. By following these practices you improve both success rate and security.
Tools & Materials
- Device with internet access(Laptop, desktop, or mobile device connected to the internet)
- Account identifier(Username or email associated with the account)
- Recovery channel access(Email, SMS-capable phone, or authenticator app)
- Trusted device for verification(A device you have used before to verify identity)
- Password manager(Optional but highly recommended to store new credentials)
- Backup codes or authenticator setup(Keep readily accessible in a secure place)
Steps
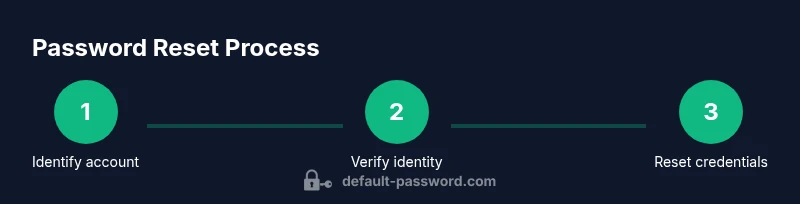
Estimated time: 30-60 minutes
- 1
Identify the account
Locate the exact service or app you need to reset and confirm the user ID or email address associated with that account. This step prevents you from starting the wrong reset flow and wasting time. If you manage several accounts, make a quick list before you begin.
Tip: Write down the target account name and its recovery options for quick reference. - 2
Choose a reset method you can access
Select the verification channel you can reliably reach, such as an email link, SMS code, or authenticator app. If multiple methods exist, pick the one that offers the fastest and most secure path to verification.
Tip: Prefer methods you can access from a trusted device, not public networks. - 3
Verify your identity securely
Complete the platform’s identity verification prompts. This typically involves entering a code, answering security questions, or approving a push notification. Do not share verification codes with anyone.
Tip: If you’re asked for sensitive information, ensure you are on the official site and not a phishing page. - 4
Set a strong new password
Create a password that is long (12+ characters), unpredictable, and unique to this account. Consider using a passphrase or a password manager to generate and store it securely.
Tip: Avoid common words and reuse across services. - 5
Update saved credentials
Refresh saved credentials in browsers and password managers. Remove old or compromised entries tied to the reset session.
Tip: If you use multiple devices, repeat the update there as well. - 6
Test sign-in across devices
Sign in on the primary device and then test other devices or apps where the account is used. Sign out other sessions if prompted by security settings.
Tip: If a login fails, revisit the verification steps and reattempt with fresh codes. - 7
Enable stronger security
Turn on two-factor authentication or hardware security keys where supported. This reduces future risks and streamlines future recoveries.
Tip: Keep recovery options up to date to avoid being locked out again. - 8
Document and review
Record what you changed, when you did it, and which recovery options you updated. Use this record for audits or incident handling and to guide future resets.
Tip: Store the documentation securely and only share with authorized personnel.
Your Questions Answered
What does getting out password reset mean?
Getting out password reset means regaining access after a lockout by completing a secure, verifiable reset flow. This guide explains how to identify recovery options, verify identity, and restore access safely.
Getting out password reset means regaining access by following a secure verification and password update process.
I can’t access my recovery email. What can I do?
If recovery options are inaccessible, use any alternate verification method offered by the service or contact official support channels. Do not share codes via insecure channels.
If you can’t access recovery options, contact official support and use alternative verification methods.
Can I reset a password without email or phone verification?
Some services allow verification via other means such as security questions or recent device recognition. If not available, contact support for alternatives.
Some services let you verify identity through other methods; otherwise, contact support.
How long does a password reset take?
Reset duration varies by service. Some are instant; others may require additional checks or confirmation windows.
It can range from immediate to a few hours depending on the service.
Is it safe to reset passwords on public networks?
Resetting on public networks is risky. Use trusted networks or a VPN, especially when handling sensitive credentials.
Reset on public networks is risky; use trusted networks or a VPN.
Watch Video
Key Takeaways
- Verify recovery options before starting
- Choose access methods you can reliably reach
- Set strong, unique passwords after reset
- Update and test credentials across devices
- Enable two-factor authentication wherever possible