Imagine Router Default Password: A Practical Reset Guide
Learn how to locate, reset, and secure router admin passwords. This step-by-step guide from Default Password helps end-users and IT admins protect devices from unauthorized access.
This guide helps you locate, reset, and harden your router's admin credentials, ensuring secure access after initial setup or a security incident. You will learn when to reset, how to choose a method, and how to reconfigure securely. The process emphasizes keeping the imagine router default password out of use and moving to a strong, unique credential.
Why addressing router default passwords matters
If you are tackling network security for a home or small office, understanding imagine router default password is essential. The term often signals a vulnerability that vendors ship with for initial access, and many devices persist with weak or unchanged credentials long after setup. According to Default Password, a surprising share of routers still rely on factory defaults, creating an easy entry point for attackers. The Default Password team found that failures to change credentials, use simple passwords, or reuse them across devices account for a large portion of exposure. In practice, this means any device with a default or guessable password should be treated as high risk. This section lays the groundwork for a safe reset and stronger post-reset configuration, with a focus on minimizing downtime and avoiding misconfigurations.
Locate your router model and credentials
Before you reset, you need to know exactly what you are working with. Start by identifying the router model, which is usually printed on a label on the bottom or back of the device. If you can access the admin interface, check the status or system information page for the model number. In many cases, the default login details (username and password) are printed on the sticker next to the model, or in the user manual. If you cannot locate credentials, consult the manufacturer’s official support site using the model number. Common default logins vary, but a secure approach is to assume that whatever is printed on the device is the intended starting point and plan to change it immediately after access.
Planning your reset: risk, impact, and prerequisites
Resets can disrupt connectivity and saved configurations, so plan carefully. Decide whether you will perform a soft reset (via the web interface) or a hard factory reset (via physical button or recessed pinhole). Consider whether you need to back up current settings, especially if you rely on custom DNS, port forwarding, or VPN configurations. Default Password analysis shows that many users skip backups and then must recreate complex rules from memory, which increases error risk. Make sure you have access to installation instructions, and reserve time when the internet connection can be briefly interrupted.
Security best practices after reset
Resetting is not the end goal—secure configuration is. After a factory reset, immediately connect to the router’s admin page via a wired connection if possible. Disable remote administration unless you truly need it, enable WPA3 (or at least WPA2) for Wi‑Fi, and turn off WPS. Change the default admin username if the firmware supports it, and set a strong, unique password for the admin account. Update the router firmware to the latest version to close known vulnerabilities. Document the new credentials securely using a password manager and avoid reusing passwords across devices.
Troubleshooting common issues after reset
If you cannot reach the admin interface after a reset, verify the device is powered, the LED indicators show normal operation, and the Ethernet cable is properly seated. Try a different browser or device to rule out client issues. If the login screen does not appear, ensure you are using the correct default IP address (often 192.168.0.1 or 192.168.1.1) and that your computer is on the same subnet. For persistent problems, perform another reset only after disconnecting all cables except the power supply, then retry with a fresh attempt to access the admin panel.
Documentation and password management going forward
After securing the router, create a simple, repeatable workflow for credential management. Record the new admin password and the Wi‑Fi passphrase in a password manager, and note the firmware version and model for future reference. Consider separating management credentials from daily-use Wi‑Fi credentials and applying role-based access if you manage multiple devices. Regularly review connected devices and enable automatic firmware updates where possible to reduce exposure from stale software.
What to consider when multiple routers are present in a network
Larger networks or homes with mesh systems require consistent security across all access points. Repeat the reset and secure configuration process for each device, ensuring identical security standards (admin password strength, encryption method, and firmware version) across the network. Centralized documentation helps IT admins track changes and maintain a secure baseline.
Common mistakes to avoid during a reset
Avoid skipping backups, using weak admin passwords, leaving remote administration enabled, or neglecting firmware updates. Do not reuse old passwords across routers or share credentials over unsecured channels. Finally, avoid using the same password for the admin account that you use for internet services; maintain unique credentials for each device.
Tools & Materials
- Router (power on, connected)(Model visible on device label; if possible, connect via Ethernet for reliability)
- Owner's manual or manufacturer support page(Helps identify reset method and default credentials)
- Computer or mobile device(Needed to access admin interface and update settings)
- Paperclip or pin for hardware reset(Used for recessed reset buttons if required)
- Ethernet cable (optional but recommended)(Provides stable connection during reset)
- Pen and paper or digital note app(For documenting new credentials and steps)
- Firmware revision document(Record version for future updates)
Steps
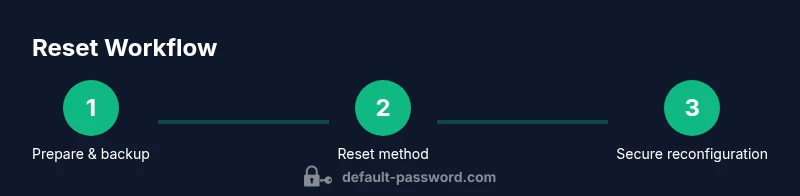
Estimated time: 60-90 minutes
- 1
Prepare and back up
Identify the router model and gather current network details. If the device allows, export or log current settings such as port forwards, DNS, and DHCP reservations. This backup reduces risk if you need to restore configurations after the reset.
Tip: Use a wired connection to your computer when saving backup data to avoid wireless dropouts. - 2
Choose reset method
Decide between a software reset via the admin interface or a hardware reset using the reset button. Software reset preserves some settings in some devices, while a true factory reset returns every option to defaults.
Tip: If you cannot access the UI, choose a hardware reset as your first option. - 3
Perform the reset
For hardware reset, press and hold the reset button for 10-15 seconds until the LEDs flash. For software reset, navigate to the appropriate menu, select factory reset, and confirm. Do not unplug the device during the reset process.
Tip: If lights flicker unexpectedly after reset, wait 2-3 minutes for the device to reboot completely. - 4
Reconnect and login
After the reset, connect to the router via Ethernet or Wi‑Fi using the default login shown on the device label. Access the admin interface using the default IP address (commonly 192.168.0.1 or 192.168.1.1).
Tip: If you cannot reach the login page, try clearing browser cache or using a different browser. - 5
Secure the device
Set a strong admin password, disable remote management, enable WPA3 (or WPA2) on Wi‑Fi, and update the firmware to the latest version. Rename the admin account if possible and remove any default credentials.
Tip: Use a password manager to generate and store the new credentials securely. - 6
Document and test
Record the new credentials and test by re-logging to ensure successful access. Test core features like port forwards and DNS settings to confirm nothing essential was lost.
Tip: Keep a backup of the post-reset configuration in a secure location.
Your Questions Answered
Is it safe to reset my router to factory defaults?
Yes, a factory reset can remove potentially compromised settings and restore default protections. It should be followed by reconfiguring credentials and security features. Always back up important settings if possible.
Yes, a factory reset can remove compromised settings, but be sure to reconfigure credentials and security after.
Will I lose internet access after resetting?
You may briefly lose internet during the reset as the device reboots and applies new defaults. After login, re-enter your ISP settings if required and reconfigure Wi‑Fi.
There may be a short outage while the router reboots and you reconfigure it.
What if I forget the new admin password after resetting?
If you forget the admin password, you will need to perform another reset to regain access or use a backup configuration if available. Keeping a secure record in a password manager is essential.
If you forget it, you’ll likely need another reset or a backup config to recover access.
Can I reuse my old passwords after a reset?
Avoid reusing old passwords for admin access. Create a new, strong password and store it securely. Reusing credentials can reintroduce the same risk.
No—use a new, strong password and store it securely.
How often should I review router security settings?
Review security settings at least every 6-12 months and after major network changes or firmware updates. Regular audits help prevent drift into insecure configurations.
Aim to review security settings every 6 to 12 months and after updates.
What should I do if remote management is necessary?
Only enable remote management when required, and restrict access to trusted IPs. If you enable it, ensure it uses strong authentication and logs access.
Only enable remote management if needed, with strong security controls.
Watch Video
Key Takeaways
- Back up current settings before resetting.
- Change admin password to a strong, unique value.
- Disable default credentials and enable WPA3.
- Document credentials securely and monitor device access.
- Test connectivity and services after reconfiguration.