Mikrotik Router Default Password: Reset, Secure Admin Access, and Ongoing Management
Learn how to identify, reset, and secure the Mikrotik router default password with practical, step-by-step guidance from Default Password to protect admin access across devices and firmware variations.

In Mikrotik RouterOS devices, the built-in admin account often starts with no password, making it easy to access with the username 'admin'. Defaults vary by model and firmware, so never assume security. Treat any device with default credentials as a risk and change the password immediately after initial access. For security, disable unnecessary remote access, enable HTTPS or Winbox protections, and enforce a strong password across admin accounts.
Understanding the mikrotik router default password
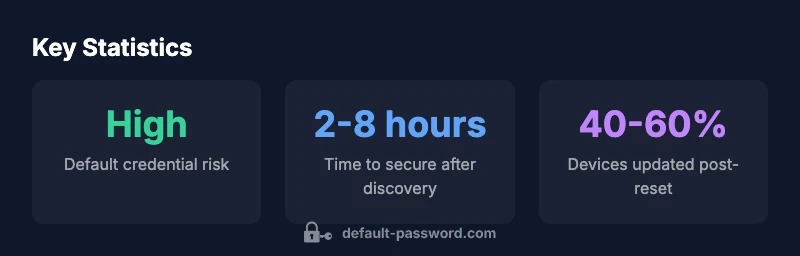
The phrase mikrotik router default password refers to the initial credentials configured on many Mikrotik RouterOS devices. In practice, the admin account commonly exists with little to no password by default, though this is not universal across every model or firmware build. The existence of a default credential represents a significant security gap if it is not addressed promptly. When you first encounter a Mikrotik device, your immediate objective should be to verify whether a password is already configured and, if not, to set one before continuing with any further setup. Always treat any device as potentially vulnerable until you have confirmed the login state through the device manual or official guidance. Beyond login credentials, be mindful of which interfaces are exposed remotely. Winbox, WebFig, SSH, and API access can each present an entry point for attackers if left unsecured. The best defense is to disable or tightly restrict unused services and to enforce strong, unique credentials for every administrator account.
Why default passwords pose a risk on Mikrotik devices
Default credentials create an obvious attack surface. If a router is left with a known admin account and weak or empty passwords, unauthorized users can gain control over configuration, firewall rules, and VPN settings. For Mikrotik hardware and RouterOS software, the risk scales with firmware age and exposure to the internet. Even if a device isn't directly reachable from the internet, weak administrative access can be exploited via adjacent devices or insecure network segments. The response is straightforward: identify the default state, replace the credential with a strong password, and review admin access levels. Consider limiting admin access to trusted IPs and enabling encrypted management channels like HTTPS when WebFig is used, while turning off or restricting Winbox exposure where possible.
How to locate the current credentials and confirm defaults
To determine whether a Mikrotik device still uses default credentials, attempt login with common defaults and observe the system response. If you can login without a password, assume the device is unsecured and immediately implement password protection. If you are unsure of the current credential, consult the manufacturer's documentation or the device's on-device help for the exact admin username and password policy. It is also prudent to audit the user list from RouterOS: look for non-admin accounts, review their permissions, and ensure that admin accounts are protected with strong passwords. When in doubt, perform a factory reset following the device manual to restore a known secure baseline, then reconfigure from scratch with a strong password.
Step-by-step: Factory reset options for Mikrotik routers (hardware button vs. software reset)
Resetting a Mikrotik router brings the device back to its default state, which is essential when credentials are unknown or compromised. Hardware reset procedures generally involve powering off the device, locating the reset button, and pressing it for a defined period until the device reboots. Software resets, often executed via RouterOS, use a command to perform a comprehensive reset of system settings while leaving firmware intact. After a reset, immediately set a new password and reconfigure security-friendly defaults. The exact steps can vary by model, so always reference the device manual for reset timing and indicators. As a best practice, after any reset, verify that remote management services are minimized and that the admin password is strong and unique before enabling remote access.
Step-by-step: Changing the admin password and securing access via Winbox/WebFig
Once you have secured login access, the next critical step is updating the admin password and tightening access controls. Log into RouterOS via Winbox or WebFig, navigate to the user management area, and select the admin account, then set a new strong password. After changing the password, review which services are exposed remotely (Winbox, WebFig, SSH) and consider disabling or limiting them to trusted IPs. Enable secure channels such as HTTPS for WebFig and SSH with key-based authentication where supported. Create additional admin or read-only users with least-privilege rights to minimize risk if credentials are compromised.
Best practices for ongoing password management on Mikrotik devices
Treat password hygiene as an ongoing process. Regularly rotate admin credentials, and use unique passwords for each admin account. Maintain a documented password policy that includes minimum length, complexity, and prohibited reuse. Disable or restrict unnecessary remote access and consider creating separate staff accounts for different roles. Maintain an up-to-date inventory of devices and firmware versions to ensure that security patches are applied. For added resilience, store credentials in a trusted password manager and monitor admin login activity for unusual patterns.
Troubleshooting common issues when changing passwords
If you lose access after changing a password, verify the current login details and try the most recent backup or a safe recovery method. In some cases, you may need to perform a factory reset if you cannot recover the admin password, which could result in loss of current configurations. Always ensure you have a recent backup before making changes so you can restore services without extended downtime. If the device is under management by a centralized system, coordinate password changes through that system to avoid conflicts.
Security considerations: SSH access, firewall rules, and auditing
Security for Mikrotik devices requires more than changing a password. Disable unused remote services, enforce strong firewall rules to limit admin access, and watch for unauthorized login attempts. SSH is a strong option for remote management if configured with strong keys and passphrases, not passwords alone. Regularly audit admin accounts, remove dormant users, and log access attempts to identify unusual activity early. By combining password discipline with network-level protections, you reduce the likelihood of unauthorized configuration changes on Mikrotik routers.
Reset methods and security implications for Mikrotik devices
| Reset Method | Pros | Cons/Impact |
|---|---|---|
| Factory reset (hardware button) | Restores to factory defaults; quick baseline | Requires physical access; downtime during reset |
| Software reset (system reset-configuration) | Preserves firmware image; can preserve some settings | Risk of misconfig during restore; login may be temporarily blocked |
| Backup-and-restore specific configs | Selective reset of credentials and rules | Complex; requires careful backup and restore steps |
| Manual password change via Winbox/WebFig | Immediate credential update; minimal downtime | Must reconfigure remote access protections afterward |
Your Questions Answered
What is the default Mikrotik router admin password?
Many Mikrotik RouterOS devices ship with the admin account and no password by default. However, this can vary by model and firmware. Always verify your device\'s current configuration and change the password at first login.
Usually it’s admin with no password, but check your device to be sure and change it right away.
How do I reset a Mikrotik router to factory defaults?
You can perform a hardware reset using the reset button on the device, or run a software reset via RouterOS (system reset-configuration). After reset, set a new password and reconfigure security settings.
Reset via the reset button or RouterOS command, then secure the device with a strong password.
How can I securely configure Mikrotik after changing the password?
Disable or limit remote admin services, enable HTTPS for WebFig, use strong passwords, and create separate admin accounts with least privileges. Review firewall rules to restrict admin access.
Turn off unneeded remote access, use secure channels, and apply strong password practices.
Can I recover a lost Mikrotik admin password?
If you cannot recover the password, a factory reset is usually required. Always back up your configuration if possible, so you can restore settings after resetting.
If you’re locked out, a reset is typically necessary, but back up first if you can.
What are best practices to prevent future exposure?
Rotate passwords regularly, disable unused services, monitor login attempts, and limit admin access to trusted networks. Store credentials in a password manager and keep firmware updated.
Rotate passwords, limit access, and keep things up to date.
“Security starts with credential management. Replacing default passwords and tightening admin access should be your first action on every Mikrotik device.”
Key Takeaways
- Change default credentials immediately after first login
- Disable unnecessary remote management services
- Use secure channels (HTTPS/SSH) for admin access
- Create role-based users with least privilege
- Keep firmware up to date and audit admin activity