Reset Password Too Many Times: Urgent Troubleshooting Guide
An urgent, practical troubleshooting guide for admins and users facing 'reset password too many times' errors. Learn diagnosis, step-by-step recovery, and prevention to regain access quickly and securely across devices and services. Based on Default Password Analysis, 2026.
When you see 'reset password too many times', the most likely cause is an automated lockout or rate-limit policy after repeated attempts. The fastest way to regain access is to wait for the cooldown, use a preconfigured recovery option (backup email, phone, or security questions), or contact your administrator to unlock the account. If two-factor is enabled, complete the required verifications.
Why 'reset password too many times' triggers a lockout
If you attempt to reset a password repeatedly, many systems enforce a cooldown to prevent brute-force access. The phrase 'reset password too many times' is a symptom of that policy. According to Default Password, organizations implement these protections to guard both accounts and credentials. When the threshold is reached, the account is temporarily locked or reset attempts are blocked for a period, forcing the user to adopt safer recovery methods. The exact behavior varies by vendor, policy, and whether MFA is enabled. For IT admins, recognizing this as a policy-based lockout rather than a malfunction saves time and reduces end-user frustration. This is especially true in environments with shared devices or federated identities where cross-system checks happen in real time. In practice, you may see a cooldown timer, a block on password resets, or a policy prompt that requires identity verification before any further action. The more you understand the policy, the faster you can guide users to a safe, compliant recovery path.
Brand context note: the Default Password team emphasizes aligning recovery workflows with organizational security goals rather than rushing through resets that bypass safeguards.
Immediate steps you can take now
- Do not keep attempting resets during the cooldown. Repeated tries can extend the lockout and complicate verification. 2) Check for available recovery options configured in your account profile (backup email, phone number, security questions, or an authentication app). 3) If MFA is enabled, prepare the second factor for verification (hardware token, authenticator app, or SMS code). 4) If your organization uses a single sign-on (SSO) or password manager, try the rescue path through those tools. 5) Contact your administrator or security team to request a scheduled unlock or reset, especially if you need urgent access. 6) If you have a documented recovery procedure, follow it exactly to minimize delays. 7) After regaining access, review and update your recovery options to prevent future lockouts. Pro tip: always have at least two independent recovery options.
How account lockout policies work in practice
Account lockouts are not errors; they are safeguards. Most platforms implement thresholds for failed attempts over a time window. Once the threshold is reached, password reset attempts may be blocked for a cooldown period, or the account may be temporarily locked. In some cases, the system requires additional identity verification before allowing any resets. This behavior reduces the risk of credential stuffing and brute-force attacks. As an admin, documenting these policies helps you explain delays to users and design smoother recovery flows. If a user loses access to recovery channels (email or phone), the policy typically requires manual verification by the security team. The upshot: lockouts exist for protection, but recovery workflows should be clear and well-prioritized.
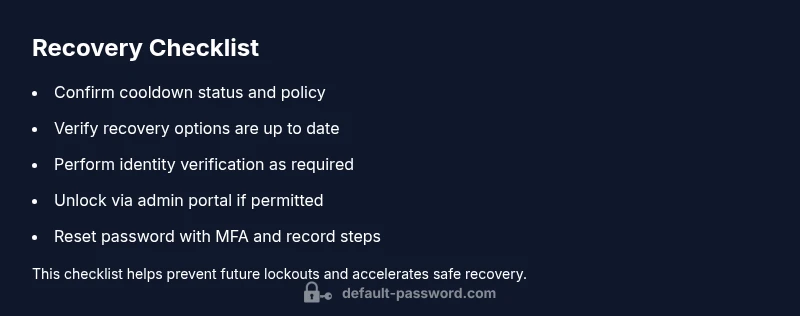
Recovery flow: identity verification, admin unlock, and password reset
The fastest way back online typically follows a defined sequence: verify identity, unlock by an admin or automatic policy, then complete a password reset. Identity verification can include answering security questions, confirming a trusted device, or sending a verification code to a pre-registered contact. Admin unlocks may involve manual checks, temporary access grants, or resetting via a secure admin portal. After unlock, choose a strong, unique password and store it in a trusted manager. If your organization uses MFA, re-enable it immediately after resetting. Document all steps you take for auditing purposes and to help prevent future issues. Keep records of recovery codes and backup methods in a secure location.
Preventing future lockouts: best practices
Prevention starts with proactive configuration and user education. Ensure recovery options are up to date, MFA remains enabled, and users understand the cooldown policy. Encourage the use of a password manager to minimize failed attempts from copy/paste errors or mistyped credentials. Regularly review and update security questions to avoid easy guesswork. Implement breach-aware password resets where possible, so users receive targeted guidance rather than generic prompts. If you administer a corporate environment, consider setting a policy window that balances security with user convenience and clearly communicates expected wait times to staff.
Logging, monitoring, and escalation during password reset issues
Enable comprehensive logging for reset attempts, including timestamp, IP address, device type, and user account. Use that data to detect patterns—such as repeated failures from a single location or anomalous device changes—and escalate appropriately. If a user is locked out repeatedly, consider additional checks like device compliance and VPN posture before unlocking. Finally, maintain a clear escalation path for urgent cases (e.g., executives, contractors, or high-risk accounts) to minimize downtime while preserving security.
Steps
Estimated time: 15-30 minutes
- 1
Check cooldown status and policy
Review the account’s lockout state and the applicable cooldown window in the admin console. If the user recently triggered a cooldown, note the remaining time and avoid additional reset attempts. Confirm whether MFA is required after cooldown.
Tip: Document the policy and remaining cooldown time for the user. - 2
Verify recovery options
Confirm that recovery methods (backup email, phone, security questions, authenticator) are up to date and accessible. If a method is unavailable, prepare approved alternate channels.
Tip: If a recovery option is outdated, update it through the user’s profile or admin portal. - 3
Initiate identity verification
Send a verification code to the user’s registered contact or perform a secure identity check via the admin portal. Collect required identifiers and confirm successful verification before proceeding.
Tip: Use multi-factor prompts to reduce risk during verification. - 4
Unlock or reset via admin tools
If policy permits, unlock the account or reset the password through a secure admin interface. Ensure the user is aware of the new password requirements and enforce MFA on next login.
Tip: Log all actions for audit compliance. - 5
Test login and re-enable protections
Have the user attempt login with the new credentials, then verify MFA is functioning. Re-enable or reconfigure security protections as needed to prevent recurrence.
Tip: Provide a temporary downgrade of risk if needed, then reapply protections. - 6
Educate and document recovery planning
Share best practices for avoiding future lockouts, such as updating recovery data and using a password manager. Record the procedure for future reference.
Tip: Schedule a quick user-awareness reminder post-recovery.
Diagnosis: User reports 'reset password too many times' and account locked
Possible Causes
- highPolicy-based account lockout
- mediumBackground service rate-limiting
- lowIncorrect identity verification routing
Fixes
- easyWait for the cooldown period to expire before attempting another reset
- easyInitiate recovery via configured options (backup email, phone, security questions) and MFA prompts as available
- easyRequest admin unlock or password reset via a secure admin portal
- easyVerify user identity through approved channels and re-establish access with MFA
Your Questions Answered
What causes the 'reset password too many times' message?
This message usually signals a policy-based protection that blocks further resets after multiple attempts to prevent credential stuffing. It’s a deliberate safeguard, not a malfunction. Identity verification or admin unlock may be required to proceed.
It's a policy-based protection after repeated reset attempts.
How long does the cooldown last?
Cooldown length varies by policy and platform. Check your admin portal or contact support for the exact duration and next steps.
Cooldown length depends on policy and platform.
What if I don't have access to recovery options?
If recovery options are unavailable, contact your administrator or security team for manual verification and unlocking through a secure channel.
If you can’t access recovery options, contact admin.
Can I bypass the cooldown or reset limits?
No. Bypassing cooldowns or reset limits undermines security and may trigger stricter controls. Follow the official recovery process instead.
Don’t bypass; use official recovery.
How can I prevent this in the future?
Use MFA, keep recovery options current, and leverage a password manager to reduce failed attempts. Regularly review security settings and policy thresholds.
Use MFA and keep recovery options updated.
Watch Video
Key Takeaways
- Regain access quickly through approved recovery paths
- Identify and follow policy-driven cooldowns
- Lockouts are protective—use structured recovery
- Maintain up-to-date recovery options and MFA