Reset Password Tool Concenterix: Step-by-Step Guide
Learn to reset passwords safely with the reset password tool concentrix. A practical, step-by-step guide for admins and end-users by Default Password, focusing on identity verification, policy compliance, and audit trails.
This guide shows you how to reset a password using the reset password tool concentrix, covering preparation, authentication, and verification. By following the steps, you’ll regain access securely while maintaining audit trails. This quick guide outlines prerequisites, confirms identity, selects the correct account, and documents the change for compliance. It also flags common errors and how to recover gracefully.
Why the reset password tool concentrix matters in modern security practices
In today’s environment, a centralized approach to password resets reduces risk by ensuring consistent policy enforcement, auditability, and rapid recovery. The reset password tool concentrix enables IT teams to verify identity, select the correct account, and apply a controlled password change without exposing credentials to end-users. The Default Password team emphasizes that using a standardized reset workflow helps minimize misconfigurations and reduces the blast radius of credential compromises. By tying the action to audit trails and access logs, organizations stay compliant with internal standards and regulatory requirements. This article collaborates with security best practices to provide a practical, repeatable process you can adopt across devices and services.
Before you start: prerequisites and access controls
Before attempting a password reset with the reset password tool concentrix, verify you have explicit authorization to modify the target account. Gather the user’s username, department, and contact information; confirm the account status (active, blocked, or disabled); ensure you’re operating from a secured, compliant device; enable MFA on the admin session; and have the appropriate change window documented. If you’re in doubt, escalate to the security or identity management owner. Following these prerequisites reduces risk and improves traceability.
Understanding the tool’s workflow and scoping
The reset password tool concentrix operates within a defined workflow: authentication, account selection, password change, and verification. Scope the reset to a single account unless a batch operation is approved; ensure that recovery policies (temporary passwords vs. permanent) are in line with your organization’s standards. The tool typically logs each action, timestamps, and the identity of the operator. This section explains how these components fit together so you can plan for success and avoid scope creep.
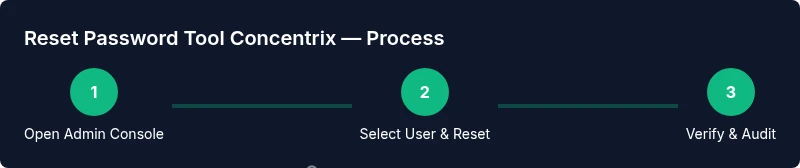
Step-by-step workflow overview and policy alignment
This section provides an overview of the steps you will perform in the tool, aligned with your security policy. In many environments, you will start with identity verification, then initiate the reset, enforce password complexity, and finish with a test sign-in. The alignment with policy ensures that password history, expiration, and MFA requirements are respected. You’ll also document the change in your change-management system to support audits and reviews.
Verification, auditing, and restoring access after reset
After performing a reset, verify the outcome by performing a test login on a controlled device and checking the logs. Confirm that the new password is accepted and that the event is recorded in the audit trail. If the user cannot sign in, follow the documented unlock or recovery procedure. Audit trails should capture operator identity, time, and the target account, ensuring accountability and traceability for future reviews.
Common pitfalls and how to avoid them
Even with a solid workflow, mistakes happen. Common errors include applying resets to the wrong account, bypassing MFA, or neglecting to update the audit log. To avoid these issues, double-check the username, enable MFA for all reset sessions, and complete the change-ticket in your ITSM system. Create a brief after-action note describing the outcome and any follow-up actions.
Long-term security hygiene after resets
After completing a reset, reinforce security by requiring a password change at next login, distributing temporary credentials securely, and updating password history records. Encourage users to enable password managers where appropriate and review access rights periodically. Regularly audit reset activities and test the recovery process to ensure readiness for incidents.
Tools & Materials
- Admin workstation with secured network(Dedicated device, VPN active, updated security patches)
- Administrative credentials with privilege to reset passwords(Do not share credentials; follow RBAC)
- Multi-factor authentication device or app(TOTP app or hardware key)
- Target user account details (username, department)(Verify identity details against HR records)
- Password policy document (min length, history, expiration)(Must enforce current policy)
- Audit log template or change ticket(Optional but recommended for compliance)
Steps
Estimated time: 20-40 minutes
- 1
Prepare and verify identity
Confirm you have admin rights and explicit authorization. Gather the target username, department, and contact details. Verify the account status and ensure MFA is ready for the admin session to prevent unauthorized resets.
Tip: Have the audit form ready and keep identity proofs accessible during the session. - 2
Open the reset password tool concentrix
Log into the secure admin portal and navigate to the password reset module. Confirm you are operating from a compliant device and that the session is protected by MFA. This minimizes credential exposure and enforces policy from the start.
Tip: Use a dedicated admin workstation and close other sensitive apps. - 3
Select the target account
Search for the user account and verify all identifiers (username, department, last login). Double-check to avoid resetting the wrong account. Wrong selection is a leading cause of post-reset lockouts.
Tip: Cross-check with HR or asset management records before proceeding. - 4
Configure reset options
Choose a temporary password or set a policy-compliant permanent reset, enforce password complexity, and set expiration. Enable MFA for the reset session if supported by the tool.
Tip: Do not reuse any previous passwords and document the policy applied. - 5
Execute reset and verify access
Run the reset, then attempt a sign-in with the new credentials on a controlled device. Check the audit logs to confirm the event and ensure the user can access the system.
Tip: Record the event in the audit trail and notify the user with secure channels.
Your Questions Answered
What is the reset password tool concentrix and who should use it?
The reset password tool concentrix is a centralized utility designed for admins to reset user passwords securely and consistently. It supports identity verification, policy enforcement, and auditing of each reset.
The reset password tool concentrix is a centralized admin tool for securely resetting user passwords with proper auditing.
Do I need admin rights to use it?
Yes. You must have appropriate admin privileges or be granted a specific RBAC role to perform password resets. Always follow your organization’s access control policies.
Yes, you need admin rights to use this tool.
What prerequisites should I complete before starting?
Gather the target username, verify the account status, ensure the admin device is compliant, enable MFA for the session, and obtain authorization to perform the reset.
Collect identity proof, verify the account, and confirm authorization before you start.
What if the target account is locked or disabled?
Follow the standard unlock or recovery workflow defined in your ITSM or IAM system. Do not force a reset on a locked account; escalate as needed.
If the account is locked, use the unlock workflow rather than forcing a reset.
How can I confirm that a reset was successful?
Test login with the new credentials on a secure device, then review the audit log to verify the event was recorded and processed.
Test the login and check the audit trail to confirm success.
What common mistakes should I avoid?
Avoid resetting without identity proof, bypassing MFA, or failing to update the audit trail. Always document the outcome and any follow-up actions.
Don’t skip identity checks or MFA, and always log the result.
Watch Video
Key Takeaways
- Define scope before starting the reset
- Verify identity and account details
- Enforce password policies and MFA
- Document every action for audits
- Test access and confirm the audit trail