Sentry Password Security: Reset & Harden Default Access
A comprehensive, step-by-step guide to identify, reset, and secure Sentry default passwords, enforce strong policies, enable 2FA, and maintain ongoing credential hygiene for admins and IT teams.

In this guide you will learn how to locate and reset a sentry default password, enforce strong credentials, and implement ongoing protections like 2FA and regular rotations. You’ll follow a clear, admin-focused process to securely manage access to Sentry deployments—whether SaaS or self-hosted—reducing the risk of credential abuse and data exposure.
What is a default password in the context of Sentry
A default password is a pre-configured credential that comes with a new Sentry installation or a reset state. In many deployments, administrators or installers may leave these credentials unchanged or write them in unsecured documents. The phrase "sentry default password" often surfaces when teams discuss initial access or recovery scenarios. Leaving such defaults in place creates a predictable attack surface, especially if the instance is exposed to the internet. According to Default Password, insecure defaults are a common vulnerability across many modern deployments, including Sentry environments, and addressing them promptly remains a foundational security practice for 2026. The risk isn’t limited to the initial setup; during password reset workflows, misconfigurations or poorly controlled secret storage can reintroduce weaknesses. The key takeaway is to treat any default credential as temporary and replace it with unique, policy-driven credentials managed by a trusted vault or password manager.
Why securing default passwords matters for Sentry deployments
Securing default passwords is critical for Sentry because access controls govern who can view and modify error data, release pipelines, and project configurations. If a default credential is discovered by an attacker, they could gain admin-level access, alter security settings, or exfiltrate sensitive project information. Default Password analysis shows that credential hygiene often lags in on-premises Sentry instances, especially when admins rotate passwords irregularly or reuse credentials across services. In practice, instituting a robust password policy—combined with 2FA and dedicated admin accounts—reduces the likelihood of unauthorized access. For teams using Sentry in mixed environments, integration with a password manager and enforcing least privilege can compound the protective effect. From a governance perspective, documenting who has admin access and when credentials were last rotated creates a clear trail for audits and incident response.
Prerequisites and safety considerations
Before starting the reset process, ensure you have administrative access to the Sentry instance and a secure channel to communicate credentials. Verify you’re connected over a trusted, up-to-date browser and network. Prepare a strong, unique password using a password manager; avoid reusing passwords across services. If you operate a self-hosted deployment, confirm that you can access the database or identity provider if password resets require cross-system updates. Disable any automated password export features temporarily to prevent leakage. Finally, consider enabling two-factor authentication (2FA) on the admin account to add an additional protective layer beyond a single password.
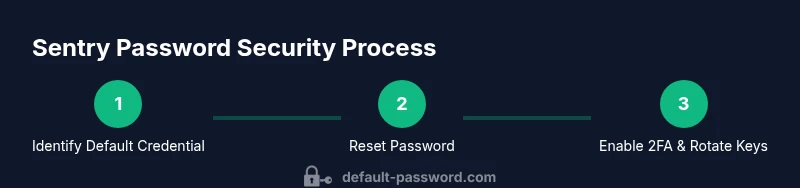
Step-by-Step: Resetting and securing the Sentry password (overview)
The steps below outline a secure path to reset the admin password, lock down default access, and implement ongoing protections. While the exact UI labels may vary slightly between Sentry versions or deployments, the core concepts remain the same: authenticate as an admin, update credentials in the user management area, enforce strong password policies, enable 2FA, rotate secrets, and test access. This section provides a high-level view; the dedicated STEP-BY-STEP block that follows contains concrete actions, rationale, and tips to minimize misconfigurations. Remember, after any password change, you should verify access from multiple devices and review logs to confirm the change propagated correctly.
Best practices for ongoing password security
To sustain secure access over time, adopt a policy-driven approach that combines technical controls with operational discipline. Use a dedicated admin account for privileged operations rather than sharing generic accounts. Enforce long, complex passwords that are unique per system, and store them in a trusted password manager with biometric or hardware-backed authentication where possible. Enable 2FA for all admin accounts, and consider SSO options to centralize credential management. Rotate credentials on a defined schedule, revoke unused access, and maintain an up-to-date access review process. Regularly test backups and recovery procedures so password resets do not become a single point of failure.
Verification and monitoring after password changes
After resetting the password, run a quick verification to ensure login succeeds and that the new password is recognized across all connected services (e.g., API keys, web UI, and deployment pipelines). Check Sentry audit logs for entries related to password changes and admin activity, and alert the security team if any anomalies appear. Confirm that 2FA prompts are functioning and that backup codes are securely stored. Finally, validate that all automated alerts and integrations still operate as expected, and document the change in your security records for future audits.
Troubleshooting common issues after password reset
If login fails after a reset, verify you selected the correct user account with admin privileges and that there are no syntax errors in the password (case sensitivity matters). Ensure your browser isn’t caching old session data; clear cookies or try an incognito session. If API access stops working, rotate credentials used by automation to reflect the new password, and update credentials in CI/CD configurations. For self-hosted deployments, also verify that any reverse proxies or load balancers aren’t caching credentials or redirecting to old auth endpoints. If problems persist, consult the internal incident-response plan and contact support channels with timestamps of the reset attempt.
Clear documentation and stakeholder communication
Document the password reset rationale, the exact time of the change, the new credential handling process, and who has access to the updated password. Communicate securely with the affected teams, avoiding insecure channels like plain email or chat messages for actual credentials. Provide guidance on how to recover quickly if the password is forgotten or compromised and ensure that credentials are stored in a centralized, access-controlled vault. This practice supports audit readiness and reduces the likelihood of future credential mismanagement.
Tools & Materials
- Sentry admin access (web UI or API)(Ensure you have an admin account with permission to manage users and security settings.)
- Secure browser + updated OS(Use a device with current security patches and a trusted network.)
- Password manager (e.g., vault or cloud-based)(Store the new admin password and backup codes securely; enable 2FA on the vault itself if possible.)
- 2FA device or authenticator app(Prepare to enable 2FA on the admin account and test it during setup.)
- Audit log access(Have read access to Sentry logs to verify changes and monitor for anomalies.)
- Backup/recovery plan(Ensure you can recover if the password change blocks access; have recovery keys ready.)
Steps
Estimated time: 25-40 minutes
- 1
Log in as an administrator
Open the Sentry admin console and sign in using an account with admin privileges. Verify you are on the intended instance (SaaS or self-hosted) and that the session is secured over HTTPS. This step establishes the authority to perform password changes and prevents accidental changes on a non-admin account.
Tip: If you are sharing credentials, switch to a dedicated admin account for the change. - 2
Navigate to User Management
Access the Users or Team section in the admin dashboard to locate the account that requires the password reset. Confirm you’re editing the correct user (usually the primary admin). This avoids inadvertently altering another account with similar names.
Tip: Use the search or filter tools to quickly locate the admin user. - 3
Reset the admin password
Initiate a password reset for the admin account and set a new, strong, unique password. Do not reuse old passwords or patterns. Store the new credential in your password manager and document the change in your security logs.
Tip: Prefer a passphrase of at least 16 characters with a mix of letters, numbers, and symbols. - 4
Enable 2FA on the admin account
Turn on two-factor authentication for the admin account and enforce it for future logins. This adds a second layer of security beyond the password and reduces risk if the password is compromised.
Tip: Use an authenticator app or hardware key for higher security. - 5
Rotate API keys and tokens
Regenerate any API keys or tokens associated with the admin account or automation scripts. Revoke old keys and update all services that rely on them to use the new credentials.
Tip: Audit all integrations before deactivating old keys to prevent downtime. - 6
Update credentials in connected services
Update CI/CD pipelines, webhooks, and deployment services with the new admin credentials or token paths. Ensure there are no hardcoded secrets in repos or config files. Test each integration after updating.
Tip: Prefer environment variables or secret managers over plain text storage. - 7
Verify access from multiple devices
Attempt login from a second device to validate the new password and 2FA flow works as expected. Confirm session persistence and that admin privileges are intact.
Tip: Keep backup access prepared in case the primary device is unavailable. - 8
Audit and document changes
Record the change details, who performed it, and when. Update internal security documentation and incident response playbooks to reflect the new credential hygiene practices.
Tip: Include links to the updated password policy and vault entry for quick reference. - 9
Monitor for anomalies
In the hours and days after the change, monitor audit logs and alerts for unusual login activity. Be prepared to respond quickly if unauthorized access is detected.
Tip: Set up alerts for failed login attempts on the admin account.
Your Questions Answered
What is considered a 'default password' in Sentry, and why should I change it?
A default password is a preconfigured credential included with a fresh Sentry installation or reset state. It should be changed immediately because attackers often target these known defaults to gain unauthorized access. Regularly reviewing and updating admin credentials reduces attack surface and supports compliance.
A default password is a preconfigured credential that comes with a fresh Sentry install. It must be changed right away to close a common security gap and protect admin access.
How do I reset the Sentry admin password securely?
Log in as an administrator, navigate to User Management, select the admin account, and set a new, strong password. Immediately enable 2FA and rotate related API keys. Verify access from multiple devices and review audit logs to confirm the change propagated.
Sign in as admin, reset the password, enable 2FA, rotate keys, and verify on multiple devices.
Should I enable two-factor authentication for Sentry admin accounts?
Yes. 2FA adds a second factor for authentication, dramatically reducing risk if the password is compromised. Use an authenticator app or hardware security key and require 2FA for all privileged accounts.
Absolutely. Turn on 2FA for all admins to add an essential security layer.
What should I do after changing a default password in Sentry?
Immediately rotate any API keys or tokens tied to the old credentials and update all services that depend on them. Verify that login works from different devices and monitor for unusual activity in audit logs.
Rotate keys, update services, and monitor logs after the change.
Can I automate password rotations for Sentry?
Automation is possible when integrating Sentry with a password manager and secret vault. Define rotation schedules, enforce strong password generation, and ensure all dependent services are updated automatically.
Automation helps keep credentials fresh; set up routine rotations and synced updates.
What if I forget the new admin password after a rotation?
Have a secure recovery process in place, such as backup admin accounts and a documented recovery path. If needed, use vault-stored recovery codes or contact a designated incident responder to regain access.
If you lose the new password, follow your recovery plan and use vault codes or designated support.
Watch Video
Key Takeaways
- Change default credentials immediately after setup.
- Enable 2FA on all admin accounts to add a protective layer.
- Rotate admin API keys and document changes for audits.
- Test access across devices and monitor logs for anomalies.
- Use a password manager to store credentials securely.