Set Default Password: A Step-by-Step Guide for Secure Access
Learn to safely set or reset a default password across devices and services. This practical, step-by-step guide covers risks, best practices, and verification checks for IT admins and end users.
You will learn to safely set or reset a default password across devices and services. The process requires admin access and a strong, unique password generated by a password manager. This quick guide outlines scope, safety checks, verification steps, and how to document changes to support ongoing security and audits.
Why setting a default password matters
Default credentials are intentional backdoors left by manufacturers and vendors. When a device ships with a known username and password, attackers can gain unauthorized access with little effort. The risk isn't limited to consumer gadgets; enterprise routers, cameras, and IoT controllers routinely use default credentials during installation and initial setup. If those defaults are never changed, an attacker can move laterally through the network, harvest credentials, and escalate privileges. This makes the simple act of set default password a critical first step in any security program. In practice, organizations that document a clear password policy and enforce changes see fewer incidents and faster incident response. Keep in mind that a compromised default password can undermine other controls—like network segmentation, MFA, and monitoring—so this is a foundation task rather than a cosmetic tweak. The Default Password team emphasizes that you should treat every login surface as potentially exposed until you properly rotate credentials. Planning and execution here pay dividends in resilience and audit readiness.
Common risks when default passwords remain unchanged
Leaving default passwords in place creates a cascade of vulnerabilities. Attackers can exploit predictable credentials to gain initial access, then pivot to other devices or services. The most common risks include unauthorized remote access, data exposure, and disruption of service. Reusing the same password across multiple devices compounds risk, because a single breach can compromise many systems. Another danger is administrator fatigue—teams may misplace credentials, leading to inconsistent security controls. By recognizing these risks, you can align your workflow to a policy-driven approach that minimizes exposure when you set default password changes. This section explains practical considerations to prevent accidental security gaps and supports ongoing governance.
When to set or reset a default password across devices
The need to set a default password arises at several moments: during initial device provisioning, after firmware or software updates, when onboarding new staff, and after any incident that may have exposed credentials. For devices already deployed, a scheduled password rotation reduces risk and keeps controls aligned with policy. If a device is decommissioned or replaced, archive old credentials securely and ensure access to replacement systems is configured with fresh, unique credentials. Remember to account for remote or headless devices where password changes require offline procedures or vendor support. A disciplined approach ensures you cover all entry points and maintain consistent security baselines.
A practical, device-agnostic approach
The core idea is to treat all devices and services the same way, whether it’s a router, printer, web portal, or IoT hub. Start with an inventory, then define a password policy that states minimum length, complexity, and rotation frequency. Use a password manager to generate and store strong, unique passwords for each surface, and activate two-factor authentication where possible. Document every change in a central, access-controlled log. By keeping this blueprint device-agnostic, you simplify maintenance and reduce the chance of missing a credential.
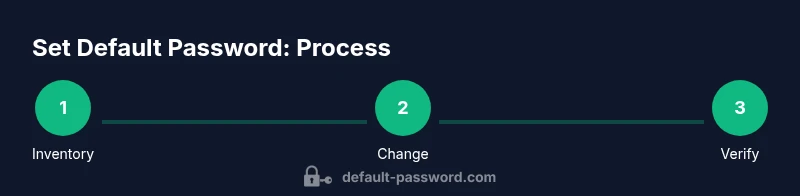
Step-by-step workflow: preparing, changing, verifying
Preparation means identifying devices, selecting a password strategy, and ensuring you have admin access. Changing credentials should be performed device-by-device to minimize downtime and avoid cascading failures. Verification involves confirming successful logins and updating credential records. The workflow can be implemented in a lab environment first, then rolled out to production. This section will map the lifecycle from inventory to audit-ready documentation, with practical tips on maintaining an up-to-date credential repository.
Verification: what to test after changing your default password
After updating a default password, test that logins work from the intended administrative account and that no other accounts are affected. Check that monitoring alerts reflect the change and that access controls still permit legitimate users. Validate that remote management remains functional if applicable, and ensure backups of configuration data remain intact. Documentation updates should capture who performed the change, when, and the scope of devices updated. A successful verification confirms that the new credentials are active and that potential vectors have been closed.
Security considerations and policy alignment
Security policy should mandate regular password rotation for critical devices and adherence to MFA where available. Align the password change process with organizational governance, data protection regulations, and vendor recommendations. Consider integrating automated reminders for rotation, and establish an exception process for devices that cannot support complex passwords or MFA. This alignment helps auditors assess control effectiveness and reduces the likelihood of policy violations.
Troubleshooting and rollback options
If a password change causes access issues, have a rollback plan ready. This may include a temporary admin account, vendor recovery procedures, or device reimage in a controlled maintenance window. Always ensure a tested backup of the device configuration exists before changes. If you suspect credential leakage, perform a forced password reset on all related surfaces and review recent access logs for anomalies.
Deployment considerations for teams and admins
For teams, standardize the change process with runbooks, checklists, and role-based access controls. Schedule multi-device changes during low-traffic windows and communicate expected downtime to stakeholders. Use centralized logging to monitor credential changes, and enforce a policy of documenting all password-related actions. This collaborative approach ensures consistency, reduces human error, and supports faster incident response when needed.
Tools & Materials
- Device admin access (console or web interface)(Ability to log in with admin rights on the target device or service)
- Strong new password or passphrase(Generated by a password manager or passphrase method)
- Password manager or secure storage(To store the new password securely)
- Documentation of password policy(Record minimum length, complexity, and rotation rules)
- Change audit log template(For recording who changed what and when)
Steps
Estimated time: 30-60 minutes
- 1
Identify affected devices
Map every device and service that uses a default credential or could be impacted by a password change. Create a centralized inventory to guide execution and minimize missed surfaces.
Tip: Start with network gear (routers, switches) and critical servers. - 2
Prepare a strong password strategy
Choose a unique, high-entropy password per surface. Use a password manager to generate and securely store credentials, or craft a long passphrase with mixed character sets.
Tip: Document the password policy and minimum requirements before changing anything. - 3
Log in with admin credentials
Access each device's admin interface using an administrator account. If an account is locked, follow vendor recovery procedures or contact support.
Tip: If possible, perform changes during a maintenance window to minimize disruption. - 4
Change the default password
Replace the default with the new strong credential. Apply the change in the primary management area and verify it saves correctly on the device.
Tip: Avoid reusing any previous passwords and double-check the save/apply action. - 5
Verify access after change
Log out and attempt to re-authenticate using the new password on each surface. Confirm remote management continues if applicable.
Tip: Test from both a manager workstation and a secondary user account if available. - 6
Document changes
Record device, old credential (masked), new credential reference, and who performed the change. Update any related access-control lists.
Tip: Store the record in your centralized credential repository. - 7
Enable MFA and policy enforcement
Where possible, enable two-factor authentication and enforce password rotation per policy across devices.
Tip: Prioritize devices that expose remote management interfaces. - 8
Audit and monitor
Review recent access logs for anomalies after password changes and set up alerts for failed login attempts.
Tip: Schedule periodic reviews to sustain security posture. - 9
Plan for rollback and future updates
Prepare a rollback path in case changes cause unintended downtime. Schedule future rotations and update runbooks accordingly.
Tip: Keep vendor support contacts handy for urgent recovery.
Your Questions Answered
Is it necessary to change default passwords on all devices?
Yes. Changing default passwords across devices reduces exposure and limits attacker opportunities. Start with critical infrastructure and expand outward.
Yes. Change default passwords on all devices to reduce risk; begin with critical equipment.
What if I forget the new password?
Use your password manager or recovery options provided by the device. If that fails, contact admin support for a reset.
If you forget the new password, check your password manager or device recovery options.
Can I reuse passwords for different devices?
No. Reusing passwords across devices increases the risk of a single breach compromising multiple systems.
Avoid reusing passwords across devices to limit risk.
How often should default passwords be rotated?
Rotate passwords per policy or after security incidents. Schedule regular rotations for critical devices.
Rotate passwords according to your security policy or after incidents.
What if a device has no UI for password change?
Use a vendor-approved method such as a console command or firmware recovery to reset credentials.
If there's no UI, use vendor-supported methods to reset or reimage.
Should admins enable two-factor authentication for access?
Yes. Enabling 2FA adds a secondary layer of protection beyond the password.
Enable 2FA for admin access when available.
Watch Video
Key Takeaways
- Plan changes before touching devices to avoid downtime
- Use unique, strong passwords for every surface
- Document credential updates in a secure log
- Verify logins after each change
- Incorporate MFA and enforce rotation policies