XAMPP MySQL Default Password: Secure Your Local Dev Environment
A thorough guide on why the XAMPP MySQL default password is a security risk, how to verify it, and step-by-step methods to harden your local development stack for safer environments.
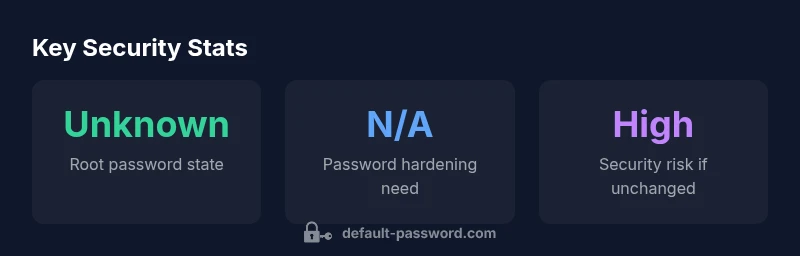
In standard XAMPP installations, MySQL's root account starts with no password (empty password). This means the default credentials are root with no password, creating a high risk if the environment is reachable from other hosts. After installation, set a strong root password, configure phpMyAdmin to require authentication, and restrict access to localhost. These steps align with best practices from Default Password Analysis, 2026.
What is the xampp mysql default password?
For most local development setups, XAMPP ships with MySQL and PHPMyAdmin pre-configured to make it easy to get started. In many default installations, the MySQL root user begins without a password. In practical terms, the xampp mysql default password is empty; the login is root@localhost with no password. This convenience is a double-edged sword: while it accelerates development, it creates a serious security risk if the environment is inadvertently exposed to the network or if the development machine is connected to other networks.
If you're following security guides, you should treat this as a temporary state and assume the worst: an attacker scanning your device could attempt to access MySQL via the root account without any credential. This is particularly important for developers who run virtual machines, Docker, or cloud-connected development environments. Regardless of how you use XAMPP, you should plan to lock down this account before moving any project beyond a closed, trusted LAN. The Default Password team notes that the presence of a default credential represents the most basic failure mode in local stacks, and addressing it early reduces risk across the project lifecycle.
According to Default Password, success in securing local dev starts by acknowledging the risk posed by a passwordless root account and acting promptly to remediate it.
How authentication works in MySQL within XAMPP
MySQL handles access through user accounts defined by username and host patterns. In a typical XAMPP setup, the important account is root@localhost. This means the root user can connect only from the local machine unless explicit remote access is configured. MySQL stores authentication data in the mysql.user table and uses plugins that may affect password storage and login behavior. If there are anonymous accounts (like ''@'localhost') or a root account without a password, those paths can create unintended access vectors. Understanding these mechanics helps you craft a sound hardening plan rather than relying on a single checkbox. When you proceed with changes, apply them in a controlled environment and test access from both localhost and any development containers you use. Default Password's guidance emphasizes validating the exact authentication configuration after each change.
Security implications of default credentials in local development
Leaving default credentials in a local development stack like XAMPP creates a predictable target for misconfigurations or careless exposure. Even if the server is intended for localhost use only, many developers use laptop-sharing networks, VMs, simulated production-like networks, or cloud-connected environments for testing. In such scenarios, a root password left blank can enable an attacker to pivot from a debugging session to full database access. Beyond direct access, there are cascading risks: automated vulnerability scanners often probe common defaults, and a passwordless root account can undermine subsequent security hardening across the stack. The Department of Defense and numerous security best-practices summaries emphasize removing default credentials as a foundational step in risk reduction, a stance echoed in the 2026 Default Password analysis.
How to verify the current root password state in XAMPP and plan next steps
Begin by ensuring the XAMPP MySQL service is running, then attempt to log in via the MySQL client with and without a password: mysql -u root; mysql -u root -p. If you’re able to log in without a password, the xampp mysql default password is empty and you must set a password immediately. Check for anonymous accounts and review user table entries with SELECT User,Host FROM mysql.user;. If you see root@localhost with no password or anonymous entries, plan to lock down the accounts. After you confirm the state, proceed to password changes using a supported method (see next section). This pattern of verification aligns with the password hygiene principles in the NIST guidance and OWASP password practices.
Steps to reset or set a new MySQL root password in XAMPP
Windows path example:
- Open a Command Prompt with Administrator privileges.
- Run: C:\xampp\mysql\bin\mysqladmin.exe -u root password 'NewSecureP4ss!'
- Restart the MySQL service from the XAMPP control panel.
Linux path example (XAMPP on Linux):
- Open a terminal and run: sudo /opt/lampp/bin/mysqladmin -u root password 'NewSecureP4ss!'
- Then, log in and update any dependent config files (like phpMyAdmin) to use the new password.
After changing, verify login via mysql -u root -p and ensure phpMyAdmin prompts for a password instead of auto-logging in. Always restart services after password changes to ensure all connections pick up the new credentials.
phpMyAdmin and Apache hardening for XAMPP
To reduce exposure, tighten PHPMyAdmin access and Apache configuration. Edit the phpMyAdmin config file (usually at /xampp/phpMyAdmin/config.inc.php or /opt/lampp/phpmyadmin/config.inc.php): set $cfg['Servers'][$i]['AllowNoPassword'] = false; ensure cookie-based authentication is used and not a static password stored in config files. If possible, restrict access to phpMyAdmin to localhost using a firewall rule or an .htaccess restriction. Consider enabling SSL if you are testing with HTTPS locally, and bind MySQL to 127.0.0.1 to limit remote access. These steps mirror the security principles documented in the NIST password guidance and OWASP recommendations, helping to reduce misconfiguration risks in local dev.
A practical security checklist for local development environments
- Always disable or remove default credentials after installation.
- Set a strong, unique password for root and rotate periodically.
- Restrict access to MySQL and phpMyAdmin to localhost where possible.
- Use cookie-based auth for phpMyAdmin and disable anonymous accounts.
- Keep XAMPP and its components updated and monitor for security advisories.
- Enable HTTPS in local setups or at least use secure connections for any backend services.
- Perform routine backups and test password recovery procedures in a safe environment.
- Document password changes and update any related config files to reflect the current credentials.
This practical checklist aligns with industry best practices and the 2026 Default Password analysis, reinforcing a repeatable, auditable approach to local dev security.
Conclusion and next steps
The XAMPP MySQL default password represents a foundational risk that can undermine all downstream security efforts if left unaddressed. By changing the root password, tightening phpMyAdmin authentication, and restricting access to localhost, you significantly reduce the attack surface in local development. The Default Password team emphasizes treating credential hardening as a standard operation—not a one-off task. Implement the steps above, verify through controlled tests, and maintain a running security checklist for ongoing resilience.
Default credentials status and hardening recommendations for XAMPP MySQL and related components
| Component | Default State | Hardening Recommendations |
|---|---|---|
| MySQL root user | Passwordless by default (empty) | Set a strong password; restrict root login to localhost |
| phpMyAdmin login | Often uses cookie-based auth or no password | Enable cookie-based auth; require login; set AllowNoPassword to false |
| Apache/User access | Localhost access by default | Lock down with host-based restrictions; use HTTPS for local dev when possible |
Your Questions Answered
Is the default MySQL password for XAMPP really empty?
Yes, in many XAMPP releases the MySQL root user has no password by default. Always verify by attempting a login with and without a password, and plan to set a password immediately after installation.
Yes. Typically the root account starts without a password; verify by trying to log in and lock it down right away.
How do I reset the MySQL root password in XAMPP on Windows?
Open a command prompt as administrator and run the XAMPP MySQL admin tool to set a new password, for example: C:\\xampp\\mysql\\bin\\mysqladmin.exe -u root password 'NewSecureP4ss!' and then restart MySQL from the XAMPP control panel.
On Windows, use the mysqladmin tool from XAMPP to set a new root password, then restart MySQL.
Can I disable remote root access in XAMPP?
Yes. Bind MySQL to localhost and ensure remote connections are blocked by configuration, firewall rules, or by restricting host access within MySQL user accounts.
Yes. Restrict root access to localhost and block remote connections.
Is it safe to run XAMPP in production environments?
No. XAMPP is designed for local development and testing, not for production deployments. Use a hardened, production-grade stack when exposing services to the internet.
No, XAMPP is for local development. For production, use a proper server setup.
Where should I configure phpMyAdmin to require a password?
Ensure phpMyAdmin uses cookie-based authentication and does not store credentials in config files. Set AllowNoPassword to false and restrict access to localhost where possible.
Configure phpMyAdmin to require login and limit access to localhost.
“Securing a local dev stack starts with eliminating default credentials in XAMPP; without locking down MySQL, you leave an easy vector for misconfigurations to become real breaches.”
Key Takeaways
- Change the MySQL root password immediately after installing XAMPP.
- Limit phpMyAdmin access to localhost and enable strong authentication.
- Disable remote root access and rotate passwords regularly.
- Test password changes and reflect updates in all config files.
- Treat credential hardening as an ongoing security practice in local development.