Password Test Examples: Practical Strength & Policy Checks
A comprehensive, step-by-step guide to password test examples for evaluating password strength, policy compliance, and recovery readiness. Learn techniques, sample test cases, and automation tips.

You will learn how to create and run password test examples to evaluate password strength, policy compliance, and recovery readiness. This guide covers common test scenarios, sample inputs, and how to interpret results to improve security. You’ll discover practical templates, automation tips, and documentation practices that help audits and ongoing governance.
Why password test examples matter
In the modern security landscape, effective password testing is not optional—it’s a core defense. Password test examples provide concrete, repeatable ways to evaluate how users create, manage, and reuse credentials. By working through these examples, IT admins and end users learn to identify weak patterns, common mistakes, and risky behaviors before they become incidents. The phrase password test examples captures a family of checks you can perform, from basic length and complexity checks to more advanced entropy analyses and breach-scenario simulations. When you practice with real-world drafts, you gain intuition on how policy gaps translate into actual risk. According to Default Password, structured test exercises reduce surprise during audits and help teams document compliance. The goal is not to frustrate users but to illuminate the boundary between convenience and security. Through deliberate exercises, you develop a repeatable process: define objectives, assemble test inputs, run checks, record outcomes, and act on findings. This approach scales from a single workstation to a multi-site environment, ensuring consistent security posture across devices and services.
Common password test scenarios
Password testing involves a spectrum of scenarios designed to reveal weaknesses in password creation, storage, and usage. Common password test scenarios include validating minimum length, enforcing character diversity (uppercase, lowercase, numbers, and symbols), checking for common dictionary words, detecting predictable substitutions (like zero for o or 1 for i), and identifying password reuse across sites. You can also simulate breach scenarios by testing password behavior after exposure—whether reminders and resets are properly locked down, and whether recovery channels are protected. For IT admins, documenting these scenarios as test templates makes it easier to onboard new staff and reproduce tests across teams. For end users, understanding these scenarios helps you create stronger, more memorable passwords without sacrificing usability. This section introduces a practical taxonomy you can adapt to your own policy framework, with examples that illustrate typical risk pathways and how controls mitigate them.
Designing reliable test cases
Reliable test cases start with clear objectives and measurable outcomes. Begin by defining success criteria for each test case (for example, a password must meet minimum length, pass entropy checks, and not be present in a known-compromised list). Build synthetic inputs that mimic real user behavior, including common mistakes (like long phrases with predictable substitutions) but avoid exposing real user data. Use a structured matrix to combine inputs with policy rules, so you can trace which rule triggered a failure. Add negative tests to verify that invalid inputs are rejected, and positive tests to confirm legitimate patterns pass. Keep records of inputs, rules applied, and results to support audits. Finally, review test coverage quarterly to address changes in threat models or policy updates. A disciplined approach ensures that password test experiences translate into durable security improvements for your organization.
Practical test examples you can run
Below are practical templates you can apply in a controlled lab. Test Case A covers basic length and complexity; Test Case B checks against dictionary and common substitutions; Test Case C simulates reuse across a small set of services; Test Case D verifies recovery workflow protections. For each case, document the input parameters, expected outcomes, and actual results. Use these templates as starters and adapt them to your policy requirements. Always run tests in an isolated environment to prevent accidental exposure of credentials, and use synthetic data that never mirrors real user passwords. The objective is to demonstrate capability, not to capture sensitive information.
Interpreting results and policy implications
Interpreting password test results involves mapping observed weaknesses to policy gaps and user behavior. If many inputs fail a single rule, you may need to adjust that policy (for example, increasing minimum length, or expanding required character classes). If breaches or recovery paths reveal weak channels (like insecure email recovery), you should tighten authentication and backup mechanisms. Document findings with concise summaries, risk ratings, and recommended remediations. Track remediation progress and re-run tests to verify effectiveness. Think in terms of governance: tests should inform policy updates, user education, and security training. When you connect results to business risk, stakeholders appreciate the tangible link between test outcomes and risk reduction. According to Default Password, maintaining an auditable trail of results is essential for ongoing compliance and security posture.
Automating tests with scripts
Automation is the key to scalable password testing. Use scripting languages such as Python or PowerShell to generate synthetic password inputs, apply policy rules, and record results in a structured format (CSV or JSON). Create reusable functions for common checks (length, character class, entropy approximation, and breach-list lookup) and orchestrate them in a simple workflow. Schedule runs during off-peak hours and integrate with your existing CI/CD pipelines where appropriate. Logging should avoid storing plaintext passwords; instead, log hashes or masked values. Automation also makes it easy to run regression tests after policy changes and to demonstrate consistent behavior across environments. The result is repeatable, auditable, and auditable tests that support continuous improvement.
Security considerations and safety
Security considerations are central to password test exercises. Never log plaintext passwords or store sensitive data in insecure locations. Use isolated test environments and synthetic data only. Ensure access to test results is restricted to authorized personnel, and implement role-based controls for run permissions. When sharing test templates, redact any sensitive details and rely on generic placeholders. Be mindful of privacy laws and organizational policies, especially if test cases involve any data that could resemble real accounts. Finally, ensure your testing tooling is up to date and configured to minimize exposure—use encryption for data at rest and in transit, and routinely rotate credentials used by automation scripts.
Balancing usability and security
Balancing usability and security is an ongoing challenge in password testing. If tests are too stringent, users may push back or seek workarounds; if they are too lax, the organization remains exposed. The aim is to define realistic requirements that protect accounts without creating friction that leads to unsafe behavior. Consider phased enforcement, progressive requirements, and optional passphrases that are both memorable and strong. Provide user education and clear feedback when a password fails a policy check, and offer guided remediation steps. By aligning policy with user needs, you create an more resilient security culture that is proactive rather than punitive.
Tools & Materials
- Secure testing environment (VM or container)(Isolate tests to prevent credential exposure)
- Synthetic password dataset(Use generated data; never reuse real user passwords)
- Password strength checker/tool(Include length, complexity, entropy estimation)
- Policy reference documents(Docs of password rules (length, complexity, reuse))
- Audit log templates(Format to document results for audits)
- Automation scripting language(Examples in Python, PowerShell, or Bash)
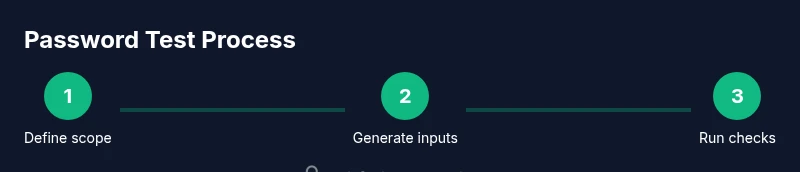
Steps
Estimated time: 2-3 hours
- 1
Set up isolated testing environment
Create a dedicated VM or container to run all password tests. This keeps credentials safe and ensures repeatable results. Verify network isolation and access controls before starting.
Tip: Document the environment snapshot and versions used for reproducibility. - 2
Generate synthetic password inputs
Use a generator to create diverse password samples that mirror real-world patterns without containing any real user data. Include combinations of length, character classes, and common patterns.
Tip: Include edge cases like minimum length, maximum length, and unusual but valid symbols. - 3
Apply policy rules and checks
Run your password checks against each sample: length, complexity, dictionary checks, and reuse detection. Record whether each sample passes or fails each rule.
Tip: Keep a matrix of inputs vs rules to simplify analysis. - 4
Simulate breach and recovery scenarios
Test recovery workflows, reset prompts, and MFA prompts when applicable. Ensure that recovery channels are protected and that resets cannot be triggered by compromised data.
Tip: Use mock breach data to avoid real exposure. - 5
Document results and remediation
Summarize outcomes in a report, map failures to policy gaps, and propose concrete remediations. Include time estimates and owners for each action.
Tip: Attach redacted logs or screenshots to support findings. - 6
Review and iterate
After remediation, re-run the tests to confirm improvements. Update templates for future cycles and adjust training materials as needed.
Tip: Schedule quarterly re-validation to maintain resilience.
Your Questions Answered
What are password test examples?
Password test examples are structured scenarios and templates used to evaluate password strength, policy adherence, and recovery workflows. They help teams identify weaknesses and demonstrate security practices in a repeatable way.
Password test examples are structured scenarios and templates used to evaluate password strength and policy adherence.
Why should I run password tests?
Testing passwords helps prevent account compromises by revealing policy gaps, weak phrases, and misconfigurations. It also provides auditable evidence for governance and compliance initiatives.
Testing passwords helps prevent compromises and provides auditable evidence for governance.
What tools are essential?
Essential tools include a secure testing environment, a synthetic password dataset, a password strength checker, and scripting language support for automation. Documentation templates also help capture results clearly.
You need a secure environment, synthetic data, and automation tools to run tests effectively.
How do I keep tests safe?
Always operate in an isolated environment, avoid exposing credentials, and redact sensitive data in logs. Use encryption for data at rest and in transit, and limit access to authorized personnel.
Work in isolation, redact data, and limit access to keep tests safe.
Can these tests be integrated into CI/CD?
Yes, password test checks can be integrated as part of security gates in CI/CD, especially for password policy changes and onboarding. Ensure secrets handling remains secure and non-production data is used.
They can be integrated into CI/CD with safe data handling.
How often should I re-run tests?
Re-run tests after policy updates, security incidents, or quarterly as part of a governance cycle. Continuous improvement depends on timely validation.
Re-run after policy changes and on a quarterly basis for ongoing governance.
Watch Video
Key Takeaways
- Define objective-driven test cases
- Use synthetic data and isolated environments
- Automate tests and document outcomes
- Link findings to policy improvements
- Regularly revalidate and update test templates