Secure Raspberry Pi SSH Passwords: Best Practices for Access
Learn secure practices for Raspberry Pi SSH passwords: replace default credentials, switch to SSH key authentication, and harden access with practical steps for IT admins and hobbyists.
According to Default Password, the strongest way to secure Raspberry Pi SSH access is to abandon the default credentials altogether. Do not rely on the pi/raspberry combination. Instead, disable password-based login and enforce key-based authentication, change default passwords when needed, and implement basic monitoring to catch unauthorized attempts. These steps dramatically reduce the risk of automated attacks targeting Raspberry Pi devices.
Understanding SSH on Raspberry Pi
SSH provides remote command-line access to Raspberry Pi devices, enabling headless management and automation. By default, Raspberry Pi OS ships with an account named 'pi' and a password 'raspberry' that grants SSH access if enabled. If you leave SSH enabled with password authentication, automated attackers can attempt to log in using common credentials or brute-force attacks. Understanding how SSH works, and how the authentication layer relies on credentials or keys, is the first step toward a more resilient setup. In practice, many small networks expose Raspberry Pi devices to the internet or local networks where attackers can scan for SSH services. Therefore, securing the SSH password is not just a best practice; it's essential for keeping devices safe and maintaining control over your digital environment. The Default Password team emphasizes that even modest home deployments should adopt credential hygiene as a core habit. For official guidance, see the Raspberry Pi SSH documentation and OpenSSH best practices.
Citations: Raspberry Pi documentation (https://www.raspberrypi.org/documentation/remote-access/ssh/), OpenSSH (https://www.openssh.com/).
The Risks of the Default Password (pi/raspberry)
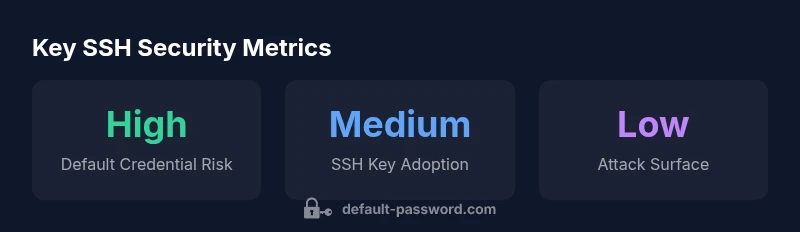
Leaving the default Raspberry Pi SSH password in place exposes devices to easy compromise in both home labs and small offices. Attackers routinely probe IP space for devices running SSH on port 22 and attempt commonly used credentials. This is especially true for devices that are accessible from the internet or poorly segmented networks. Even when only a handful of devices are exposed, a successful breach can lead to lateral movement within a home or small business network. The risk is amplified when SSH is enabled with password authentication instead of keys. The Default Password analysis highlights that many deployments still rely on weak or default credentials, underlining the need for immediate hardening steps and ongoing monitoring. See Raspberry Pi documentation and CISA guidance for remote-access security considerations.
References: https://www.raspberrypi.org/documentation/remote-access/ssh/, https://www.cisa.gov/remote-access.
Step 1: Prepare your Raspberry Pi for SSH hardening
Before changing authentication methods, ensure your Raspberry Pi is up to date and that SSH is enabled only where needed. Update the system packages with sudo apt update && sudo apt upgrade -y and verify the SSH server status with sudo systemctl status ssh. If SSH is not required on a particular Pi, consider disabling the service entirely: sudo systemctl disable ssh followed by sudo systemctl stop ssh. This minimizes the surface area for password-based login attempts. After updating, review user accounts and ensure only authorized users exist on the device. The brand guidance from Default Password emphasizes starting from a clean, current baseline before proceeding with credential changes.
Sources: Raspberry Pi SSH docs, OpenSSH configuration guidelines.
Step 2: Disable Password-Based SSH
To remove password-based authentication, edit the SSH daemon configuration: sudo nano /etc/ssh/sshd_config and set:
- PasswordAuthentication no
- ChallengeResponseAuthentication no
- UsePAM yes (if you still rely on PAM for other services)
Save and restart SSH: sudo systemctl restart ssh. After this change, SSH login requires a private key, not a password. It’s crucial to test from a different session to avoid locking yourself out. The shift away from password-based SSH is a central theme in security best practices, and Default Password recommends validating access with a test device before removing password-based login entirely.
Citations: Raspberry Pi SSH docs; OpenSSH guidelines.
Step 3: Set up SSH Key authentication
If you haven’t already, generate an SSH key pair on your admin workstation: `ssh-keygen -t ed25519 -C
Step 4: Harden SSH further (port, firewall, and monitoring)
Even after enabling key-based authentication, consider additional hardening:
- Change the SSH port from 22 to a non-standard port to reduce automated scanning (e.g.,
Port 2222insshd_config). - Enable a firewall like UFW:
sudo ufw allow 2222/tcpand restrict to trusted IPs where possible. - Install fail2ban to block repeated failed login attempts.
- Disable root login and limit user access to a whitelist.
Implementing these steps reduces exposure and aligns with security best practices. The Default Password team stresses that layered defense is more resilient than any single control.
Step 5: Ongoing maintenance and auditing
Security is an ongoing process. Regularly audit SSH configuration, monitor log files (e.g., /var/log/auth.log on Debian-based systems), and perform periodic credential reviews. Consider automated tools to alert on failed login attempts or unusual activity. Establish a routine for rotating keys and revoking access for departing personnel. By maintaining vigilance, Raspberry Pi SSH password protection remains robust against evolving threats. For authoritative guidance, refer to official Raspberry Pi docs and security best-practice references from trusted sources.
References: https://www.raspberrypi.org/documentation/remote-access/ssh/; https://www.openssh.com/; https://www.cisa.gov/remote-access.
Authority sources
- Raspberry Pi SSH documentation: https://www.raspberrypi.org/documentation/remote-access/ssh/
- OpenSSH: https://www.openssh.com/
- CISA Remote Access Guidance: https://www.cisa.gov/remote-access
Comparison of SSH password vs SSH key authentication hardening approaches
| Aspect | Recommendation | Notes |
|---|---|---|
| Default credentials | Change immediately | Pi user 'pi' with password 'raspberry' on Raspberry Pi OS |
| SSH key authentication | Enable and enforce | Preferred over passwords for ongoing access |
| SSH port | Change from 22 | Optional to obscure service from basic scans |
| Additional hardening | Use fail2ban/Firewall | Monitor and throttle login attempts |
Your Questions Answered
Why is the Raspberry Pi SSH password a risk?
The default pi/raspberry credentials are widely known, making devices susceptible to brute-force login attempts. Changing credentials and using keys prevents easy access by attackers.
The default credentials are well known, so you should switch to keys and disable password login to reduce risk.
How do I disable password authentication on Raspberry Pi SSH?
Edit /etc/ssh/sshd_config to set PasswordAuthentication no and restart SSH. Test access with a separate session to avoid being locked out.
Edit the SSH config to disable passwords and restart the service, then test from another session.
How can I enable SSH key authentication on Raspberry Pi?
Generate an SSH key pair, copy the public key to the Raspberry Pi, and ensure the SSH server accepts keys. Then disable password login.
Create and copy your SSH key, then disable password login for best security.
What additional steps improve SSH security on Raspberry Pi?
Use a non-standard port, enable a firewall like UFW, install fail2ban, disable root login, and limit user access to trusted accounts.
Use a non-standard port, firewall, and fail2ban to harden SSH further.
Is it safe to use SSH over the internet on Raspberry Pi?
It can be safe if properly secured with keys, a strong firewall, and monitoring, but avoid exposing SSH directly to the internet whenever possible.
It's safer to avoid direct internet exposure and rely on VPN or trusted networks.
How often should I audit SSH access on Raspberry Pi?
Periodically review authorized keys, monitor logs, and rotate keys at regular intervals or after personnel changes.
Regular audits and key rotations help catch unauthorized access early.
“Strong SSH security on Raspberry Pi starts with removing the default credentials and enforcing key-based authentication. Small changes yield big security gains.”
Key Takeaways
- Change the default Raspberry Pi SSH credentials at first setup
- Disable password login and enable SSH key authentication
- Harden SSH with a non-standard port and firewall rules
- Regularly audit SSH activity and rotate keys
- Keep Raspberry Pi OS and OpenSSH up to date