How to Change Default Password Policy in Active Directory
Step-by-step guide to changing the default password policy in Active Directory, including length, complexity, history, and lockout rules. Practical guidance from Default Password.

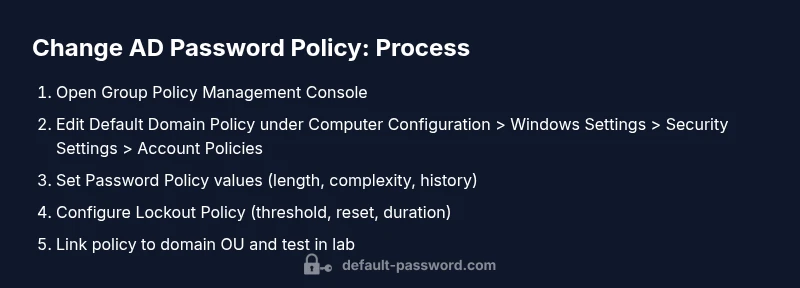
You will change the Active Directory password policy by editing the domain-level Group Policy (Default Domain Policy) to enforce new password length, complexity, history, and lockout rules. This change applies to all domain users and computers in the domain. Ensure you have Domain Admin rights, back up current policies, and test in a controlled OU before full rollout. Document changes and communicate timelines to users.
Why Changing Default Password Policy Matters in Active Directory
In modern IT environments, weak or inconsistent password policies leave networks vulnerable to credential stuffing and brute-force attacks. A well-defined password policy helps enforce minimum lengths, complexity requirements, and password history to prevent reuse. According to Default Password, consistent policy enforcement across the domain reduces attack surfaces and strengthens overall security posture. For organizations using Active Directory, aligning policy with industry standards and regulatory requirements is essential. This block explores the rationale behind updating the default password policy and how a carefully designed policy supports user provisioning, access governance, and incident response. By centralizing settings in the Default Domain Policy, you ensure uniform coverage across all domain-joined devices, servers, and services.
- Improves account security and reduces risk of credential reuse
- Supports compliance with security frameworks and audits
- Simplifies management through centralized policy administration
- Enables safe rollouts with testing in a controlled OU
Tip: Always document the policy rationale and expected impacts so IT staff and end users understand why changes are needed.
Prerequisites and Scope: What You’ll Need
Before you begin, define the scope of the password policy change. In most enterprises, password policy is configured at the domain level via Default Domain Policy, applying to all domain users and computers. If your environment uses Fine-Grained Password Policy (FGPP) for specific groups, plan how FGPP interacts with the domain policy to avoid conflicting rules. You will need administrator access to modify GPOs, a tested recovery plan, and a rollback strategy in case the changes cause authentication issues. The process is safer when performed during a maintenance window and communicated to stakeholders in advance. As a reminder from Default Password, starting with a backup export of the current GPO state reduces recovery time if you need to revert.
- Admin credentials with rights to edit GPOs
- Access to Group Policy Management Console (GPMC)
- A tested backup/restore plan for the GPOs
- A test OU to pilot the changes
- Clear rollback and communication plan
Understanding Domain vs Fine-Grained Password Policy
Active Directory supports two mechanisms to govern password behavior: the Domain Password Policy (DP) and Fine-Grained Password Policy (FGPP). The DP is defined in the domain's password policy settings and applies uniformly to all users. FGPP allows different settings for defined groups temporarily, using Password Settings Container objects (per-user/per-group policies). When you change the Default Domain Policy, you’re adjusting the baseline that affects most accounts. If you require exceptions (e.g., contractors or privileged groups), FGPP can supplement the baseline, but it requires careful planning to prevent conflicts. For security-conscious admins, combining DP with FGPP offers a balance between broad control and targeted exceptions. Default Password emphasizes testing both layers in a lab before production deployment.
- DP provides baseline security across the domain
- FGPP enables targeted controls for specific groups
- Conflicts between DP and FGPP can cause inconsistent behavior
- Plan a staged rollout and document group-specific requirements
Step-by-Step: Open Group Policy Management Console and Locate Default Domain Policy
To begin, sign in with a domain administrator account and launch the Group Policy Management Console (GPMC). In the left pane, expand Forest > Domains > [YourDomain] > Policies. Locate the Default Domain Policy, which houses the core password policy settings for domain users. If Default Domain Policy has been renamed or replaced in your environment, identify the equivalent policy that contains the Password Policy and related settings. Before making changes, export a backup of the policy so you can compare current settings and revert if needed. This careful preparation aligns with best practices recommended by Default Password and avoids accidental policy drift during implementation.
- Open GPMC from Administrative Tools or RSAT
- Find Default Domain Policy under the domain node
- Export a backup of the policy settings before editing
- Confirm that editing this policy won’t conflict with FGPP or other GPOs
Step-by-Step: Edit Password Policy Settings (Length, Complexity, History)
Within the Default Domain Policy, navigate to Computer Configuration > Windows Settings > Security Settings > Account Policies > Password Policy. Here you can set: minimum password length, password must meet complexity requirements, and password history (how many unique passwords are remembered). Adjust the Maximum Password Age and Minimum Password Age as needed. Make incremental changes rather than large shifts to minimize user disruption. After saving the changes, run a policy update on a test machine using gpupdate /force to verify behavior. Remember, this policy applies domain-wide, so review impact on all endpoints.
- Modify Minimum Password Length and Passwords Must Meet Complexity Requirements
- Configure Password History and Maximum/Minimum Age
- Run gpupdate /force on test devices to verify
- Document the exact values for auditing purposes
Step-by-Step: Configure Lockout Policy and Advanced Settings
Account lockout is a key part of defense against brute-force attempts. In the same policy area, configure the Account Lockout Policy with Threshold, Reset Counter, and Duration. The Threshold defines how many failed attempts trigger a lockout; the Reset Counter determines how long before failures reset; Duration sets how long an account remains locked. Choose values that balance security with user productivity (e.g., 5 attempts, 15 minutes reset, 30 minutes lockout for moderate environments). Be mindful that overly aggressive lockout settings can lead to helpdesk burdens. Always test these settings in your lab and include them in your rollout plan.
- Set reasonable lockout threshold (e.g., 5 attempts)
- Define reset counter interval (e.g., 15 minutes)
- Choose a practical lockout duration (e.g., 30 minutes)
- Validate behavior on test machines and logs
Step-by-Step: Ensure Proper Inheritance, Linking, and Scope
After configuring the policy, verify that it is properly linked to the domain and scope. Ensure that the policy is not unintentionally overridden by other GPOs with higher precedence and that inheritance settings are appropriate for organizational units (OUs). If you encounter conflicts, use the Group Policy Modeling Wizard to simulate results before applying changes to production. If necessary, apply Enforce on the Default Domain Policy or adjust Link Order to ensure predictable behavior. Finally, document all changes and the rationale for precedence decisions.
- Check GPO link status and inheritance
- Use Model and Results Wizard for planning
- Consider Enforce or Block Inheritance where appropriate
- Document the final linkage and precedence decisions
Step-by-Step: Testing, Rollout, and Communication
Testing is critical for a successful rollout. Start in a dedicated Test OU that mirrors production but contains a limited user set. Validate that password changes, user sign-ins, and login scripts work as expected. Monitor authentication events and look for unexpected lockouts or sync issues across DCs, endpoints, and services. Prepare a communication plan to inform users about the new password requirements, update helpdesk scripts, and provide self-service password reset options if available. After successful testing, schedule a phased rollout to minimize disruption and ensure a smooth transition across the domain.
- Run tests in a controlled OU
- Monitor authentication events and DC logs
- Communicate policy changes to users and helpdesk staff
- Schedule phased rollout with a rollback option
Step-by-Step: Risks, Rollback, and Governance for AD Password Policy Changes
Any policy change carries risk. Potential issues include user frustration, login failures, and unexpected interactions with legacy systems or applications that do not comply with stronger password rules. Establish a rollback plan, including a be-it-backup of the original policy and a defined rollback window. Maintain governance by documenting approvals, stakeholder sign-offs, and change tickets. After deployment, review security metrics and audit trails to ensure the policy achieves its intended security improvements without introducing new problems. The Default Password team recommends continuous improvement and periodic review of password policies to keep pace with evolving threats.
- Prepare a documented rollback plan
- Monitor security metrics post-deployment
- Audit policy changes and adherence
- Schedule regular reviews of password policy alignment with threats
Tools & Materials
- Domain Admin credentials(Essential for editing domain-level GPOs (Default Domain Policy))
- Group Policy Management Console (GPMC)(Installed on a management workstation or server)
- Test OU and lab environment(Used for staged rollout and validation)
- Current GPO backup export(Prior to changes, export the existing policy state)
- Change management plan(Include rollback steps and communication plan)
- Monitoring and auditing tools(Event Viewer, DC logs, and security auditing)
Steps
Estimated time: 30-60 minutes
- 1
Open Group Policy Management Console
Log in with Domain Admin credentials and launch GPMC. Navigate to Forest > Domains > YourDomain > Policies to locate the Default Domain Policy. If you don’t see GPMC, install the RSAT tools or use a server with GPMC installed. This step prepares you for policy editing and ensures you’re working in the correct domain context.
Tip: If the Default Domain Policy is not visible, verify that you have the right forest and domain selected and that you’re connected to a Domain Controller. - 2
Backup the current Default Domain Policy
Right-click Default Domain Policy and choose Back Up. Store the backup in a secure location and update the change ticket with the backup timestamp. This provides a clean rollback point if the new settings cause unintended access issues.
Tip: Keep backups in an isolated, access-controlled folder; note the backup path for quick restore. - 3
Open Password Policy settings
In the Policy Editor, expand Computer Configuration > Windows Settings > Security Settings > Account Policies > Password Policy. Review the current values for Minimum Password Length and Complexity to confirm what changes are needed.
Tip: Document existing values before changing; reference the organization’s security baseline. - 4
Adjust password length and complexity
Set the new Minimum Password Length and enable Passwords Must Meet Complexity Requirements. Also adjust Password History and the Maximum/Minimum Password Age as appropriate for your risk posture. Save changes and apply to the domain policy.
Tip: Make incremental changes if you’re unsure about impact; avoid sweeping modifications in one go. - 5
Configure lockout policy
Navigate to Account Lockout Policy and set the threshold, reset counter, and lockout duration. Choose values that balance security with user productivity to prevent helpdesk overload while mitigating brute-force attempts.
Tip: Document the chosen values and communicate them to IT and security teams before deployment. - 6
Review inheritance and policy linkage
Ensure the policy is linked to the correct domain level and that inheritance isn’t overridden by other GPOs. If necessary, adjust link order or enable Enforce for the Default Domain Policy to ensure consistent application.
Tip: Use the Group Policy Modeling Wizard to anticipate results in different OUs. - 7
Test in a controlled environment
Apply the updated policy to a Test OU and run a controlled sign-in test with representative user accounts. Verify that password changes, lockouts, and authentication across apps and services behave as expected.
Tip: Test with corporate apps and VPN or cloud services that rely on domain credentials. - 8
Plan rollout and communication
Schedule a phased deployment, communicate the new requirements to users, and provide self-service password reset options if available. Prepare helpdesk scripts and ensure monitoring is in place for the rollout window.
Tip: Provide a clear FAQ and expected password behavior post-change. - 9
Monitor, audit, and adjust
After deployment, monitor authentication events, review security logs, and verify that policy changes meet compliance goals. Be prepared to adjust if issues surface during the rollout.
Tip: Schedule a post-deployment review to identify improvements for the next cycle.
Your Questions Answered
What is the difference between Domain Password Policy and Fine-Grained Password Policy?
Domain Password Policy defines the baseline rules for the entire domain, while Fine-Grained Password Policy allows exceptions for specific groups. FGPP uses Password Settings Containers to apply different settings. Plan carefully to avoid conflicts and test in a lab before production.
Domain Policy sets the baseline for all users; FGPP can tailor rules for certain groups, but you must test to avoid conflicts.
How do I test a new password policy before applying it domain-wide?
Use a dedicated Test OU and simulated scenarios with representative accounts. Validate sign-ins, password changes, and access to critical apps. Review logs and adjust settings based on findings before rolling out to production.
Test in a controlled OU with representative accounts and monitor the results before full deployment.
Will changing the policy affect existing passwords?
Existing passwords are not immediately forced to meet new rules; new password requirements apply at next password change. If you enable older password histories, users may encounter prompts at next sign-in.
Existing passwords stay valid until changed, but new policy requires new passwords going forward.
What are common pitfalls when updating AD password policy?
Pitfalls include conflicting FGPP vs DP, overly aggressive lockout settings causing helpdesk load, and forgetting to test across VPN and cloud services that rely on domain credentials.
Watch for FGPP conflicts and test across all systems that use AD credentials.
How do I rollback changes if something goes wrong?
Use the backup you created of Default Domain Policy to restore original settings. Validate restoration in a test environment and re-test critical logins before re-deploying.
Restore the backed-up policy from the backup point and re-test before trying again.
Watch Video
Key Takeaways
- Define policy scope: domain-wide vs fine-grained
- Test changes in a controlled OU before production
- Document settings and rollout plan for audits
- Communicate password policy changes to users and helpdesk
- Monitor authentication events after deployment