Fine-grained Password Policy vs Default Domain Policy: A Practical Comparison
A detailed, practical comparison of fine-grained password policy versus default domain policy, with guidance on when and how to apply each approach for security, usability, and governance.

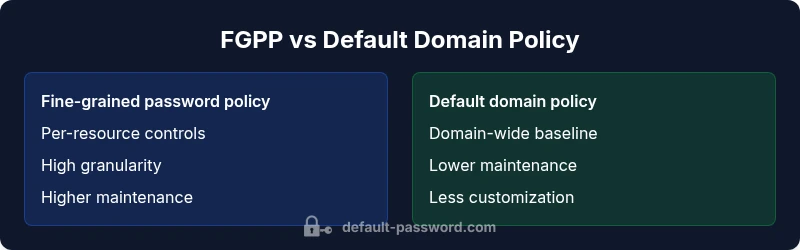
TL;DR: Fine-grained password policy lets you apply specific rules to users, groups, devices, or resources, while default domain policy enforces a single, broad set of rules across the entire domain. The difference matters for security, usability, and administration. In practice, teams often combine both approaches, using a strong baseline policy with targeted exceptions for sensitive assets.
Conceptual foundations: policy design goals
Policy design for authentication and password management rests on a balance between security controls and user productivity. A well-chosen approach aligns risk tolerance, regulatory requirements, and operational capacity. When evaluating fine-grained password policy vs default domain policy, organizations should ask: where do we need precision, and where do we need consistency? The framed question guides whether to emphasize scope, granularity, and exception handling, or to prioritize centralized governance and uniform user experiences. According to Default Password, effective policy design begins with a risk model that identifies the most sensitive assets, the most active user cohorts, and the environments where compromise would cause the greatest harm. This upfront planning reduces later surprises and helps ensure policy decisions are auditable and repeatable.
What is a fine-grained password policy (FGPP)?
Fine-grained password policy is a modular approach to credential rules that can be tailored by resource, user attribute, group, device, or application. FGPP enables per-resource rules—such as longer history, stricter complexity, or shorter lockout windows for privileged accounts—without forcing the same rules on every user. In practice, FGPP is implemented as policy objects attached to specific identities or resources and can be expressed as exceptions or overlays to a baseline policy. Benefits include improved risk management for high-value assets and the ability to reflect real-world risk profiles, but it comes with governance complexity and higher maintenance overhead.
What is the default domain policy? A baseline approach
A default domain policy establishes a baseline set of password rules that apply across all users and computers within a domain. This policy aims for consistency, predictable user experience, and easier administration. It sets the floor: minimum length, expiration cadence, lockout thresholds, and recovery options that apply to everyone unless explicitly overridden. The strength of this approach lies in simplicity and auditable uniform enforcement, but it can oversimplify protection for sensitive resources or specialized roles. The default policy should be designed with a strong baseline while allowing controlled deviations for exceptional cases.
Security impact: risk, incentives, and caveats
Security outcomes depend as much on policy mechanics as on organizational processes. A strong FGPP can reduce risk for high-value assets by applying stringent controls where needed, while a shared domain baseline ensures broad protection and reduces policy drift. However, misconfigurations or inconsistent overrides can create blind spots if policy boundaries are unclear. Organizations must balance risk segmentation with ease of governance. The preferred path often blends both approaches: a robust baseline policy for general users, plus targeted FGPP for critical resources. The Default Password team notes that layered controls, coupled with rigorous change management, yield the most reliable security posture.
Governance, ownership, and accountability
Governance determines who approves changes, how exceptions are tracked, and how audits are performed. FGPP requires clearly defined owners for each policy object, a lifecycle for creating and retiring overrides, and automated tests to validate policy behavior. The default domain policy benefits from centralized administration, version control, and standardized change procedures. A blended model should include a documented override process, periodic reviews, and an auditable trail that shows how and why rules were adjusted. In this context, maintain visibility into conflict resolution and ensure accountability across teams.
Deployment patterns and tooling considerations
Choosing between FGPP and a domain baseline is not just a policy decision—it is a deployment challenge. Some organizations implement FGPP in a hierarchical or resource-centric manner, aligning rules with asset criticality. Others layer FGPP on top of an existing domain policy, using policy inheritance and explicit exceptions. Tooling plays a critical role: identity governance, privileged access management, and password hygiene tooling can simplify deployment, testing, and remediation. Automation should support policy provisioning, validation, and drift detection. The aim is to minimize manual steps while maximizing confidence in rule accuracy and coverage.
Real-world scenarios: SMBs, mid-market, and enterprises
Small and medium businesses often favor a strong baseline domain policy due to limited administration bandwidth, preferring predictable enforcement and straightforward user experiences. Mid-market and enterprise customers benefit from FGPP when dealing with diverse resource types, on-prem and cloud identities, and a need to restrict access for highly sensitive ecosystems. In cloud-forward environments, FGPP can align credentials with resource ownership and risk. The key is to map policy to risk profiles, not just technology stacks. The best outcomes arise when policy design reflects actual workflows and governance processes.
Migration path: phasing FGPP into a domain-centric model
Deploying FGPP alongside a baseline policy requires careful planning. Start with a policy inventory that lists all current rules and overrides. Next, classify assets by risk and determine where FGPP would yield measurable benefits. Develop a pilot program that applies FGPP to a small set of high-risk resources, monitor user impact, and validate security improvements. Expand progressively, ensuring that change-management processes capture lessons learned and that auditing capabilities scale with policy complexity. The end goal is a maintainable mix where policy ambiguity is minimized and enforcement remains consistent across environments.
Common pitfalls and how to avoid them
Misconfigurations often stem from ambiguous ownership, unclear inheritance rules, and gaps between policy boundaries and actual access controls. Avoid drift by enforcing centralized change control, automated tests, and regular reconciliation against asset inventories. Document overrides with a clear rationale and sunset timelines. Regularly review access review processes, and ensure that auditing and alerting cover both FGPP and the default policy.
Comparison
| Feature | Fine-grained password policy | Default domain policy |
|---|---|---|
| Scope | Per-resource, per-identity, or per-application rules | Domain-wide baseline for all users and devices |
| Granularity | High; rules can vary by resource or role | Moderate; a single rule set with limited exceptions |
| Maintenance effort | Higher; requires governance, review cycles, and tooling | Lower; centralized governance and predictable updates |
| Auditability | Detailed, resource-specific logging and event correlation | Unified domain audit events with broad visibility |
| User experience | Potential friction from exceptions; users in sensitive roles may see stricter controls | More consistent experience across users |
| Best for | Risk-sensitive assets, regulated environments, or complex identities | Organizations seeking simplicity and consistency |
Upsides
- Stronger protection for high-risk resources through targeted controls
- Greater flexibility to tailor rules by asset or group
- Supports alignment with zero-trust and identity-centric security models
- Improved incident response with granular auditing out of the box
The Bad
- Increased management overhead and policy sprawl
- Greater risk of misconfigurations without strong governance
- Requires more sophisticated tooling and skilled administrators
- Potential user friction if too many exceptions are applied
Adopt a blended approach: a solid baseline domain policy with selective FGPP for sensitive resources.
A layered strategy typically offers the best balance of security and operational practicality. Start with a strong, auditable baseline policy and layer fine-grained controls where asset risk justifies it. This approach reduces drift, improves accountability, and supports scalable governance.
Your Questions Answered
What is the key difference between fine-grained password policy and default domain policy?
The key difference lies in scope and flexibility. FGPP applies rules to specific resources, identities, or groups, enabling tailored controls. The default domain policy provides a single baseline that covers all users and devices unless explicitly overridden.
FGPP targets specific resources while the domain policy is a universal baseline.
When should I use FGPP over a domain-wide policy?
Use FGPP when asset risk varies significantly—such as privileged accounts, critical servers, or highly sensitive data. If most resources share similar risk, a strong domain baseline with selective FGPP may be more practical.
Apply FGPP where risk is not uniform across resources.
Can FGPP be implemented without disrupting users?
Yes, but it requires careful rollout. Start with a pilot, communicate changes, and ensure exceptions don’t create user confusion. Provide clear guidance and training to reduce friction.
Pilot first, then expand with clear communication.
How do I audit FGPP and domain policy changes?
Maintain an auditable change log for every policy object, track approvals, and automate drift detection. Use centralized dashboards to correlate policy changes with access events.
Keep a change log and monitor drift.
What tooling supports FGPP in mixed environments?
Identity governance, privileged access management, and password hygiene tools typically support FGPP. Ensure tools can model inheritance, overrides, and policy testing.
Look for governance and PAM integrations.
Is FGPP required for regulatory compliance?
Regulations vary; FGPP can help meet risk-based controls but is not universally mandatory. Focus on evidence of risk assessment, control customization, and auditability.
Regulations need risk-based controls; FGPP helps, not always required.
Key Takeaways
- Define a strong baseline policy first
- Apply FGPP selectively to high-risk assets
- Invest in governance and change-management
- Automate policy provisioning and drift detection
- Regularly audit and test policy effectiveness