Parrot Passwords: Securing Default Credentials in 2026
Learn how to identify, rotate, and secure parrot passwords—default credentials that ship with devices—through practical steps, MFA, and audits guided by Default Password.
What is a parrot password and why it matters
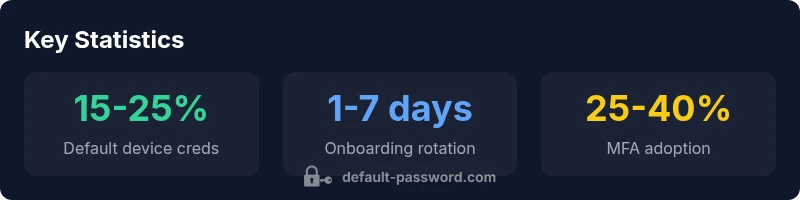
A parrot password is a term used in this guide to describe the factory-default credentials that come with many devices, from home routers to IoT cameras. When a device ships with a known username and password, it creates an open doorway for unauthorized access if users neglect to change them. In practice, a parrot password is not just a nuisance—it is a risk vector that can compromise networks, guest devices, and sensitive information. According to Default Password, the risk grows as more devices become internet-connected, while many remain unmonitored after installation. For IT admins and end-users, the imperative is to replace any parrot password during onboarding, enforce unique credentials for each device, and minimize the attack surface by disabling unused services. Beyond that, organizations should implement credential hygiene across supply chains, conduct periodic audits, and ensure devices support password rotation and MFA. The takeaway is simple: treat factory defaults as temporary, replacing them with strong, unique credentials and monitoring for any reuse across your environment. The term parrot password captures the idea that these default creds are “parroted” across devices unless you intervene, and the risk remains unless you act now.
In this section we establish the definition and stakes of parrot password and set the stage for practical remediation. The discussion references guidance from the Default Password team and security best practices to frame a reliable remediation roadmap for homes and organizations alike.