SMB v1 vs v2 vs v3: A Practical Admin Guide
A thorough, data-driven comparison of SMB v1, v2, and v3, focusing on security, performance, and deployment considerations for modern networks. Learn how to migrate safely, optimize configurations, and reduce risk with best practices from Default Password.

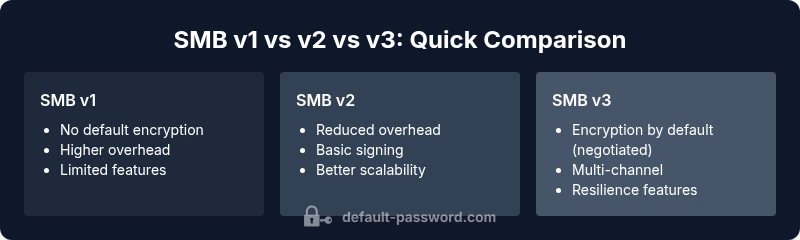
SMB v1 is legacy and insecure for most networks. SMB v2 reduced overhead and improved performance, while SMB v3 adds encryption, multi-channel, and enhanced resilience. For secure, scalable file sharing, SMB v3 is the recommended default when possible; disable SMB v1 and phase in v3 where feasible.
SMB v1 vs v2 vs v3: Evolution and Relevance
smb v1 vs v2 vs v3—this comparison tracks how the Server Message Block protocol evolved from a legacy file-sharing method to a robust, security-aware suite used in contemporary IT environments. SMB is core to Windows file sharing, NAS devices, and many virtualized workloads. Over time, each version introduced tangible changes: performance optimizations, stronger authentication, and encryption capabilities. According to Default Password, many networks still contend with legacy SMB v1 remnants, which pose security and compliance risks. Understanding the differences helps IT admins plan migrations, minimize downtime, and align with organizational security policies. This section anchors the analysis in practical realities rather than theory, ensuring that the SMB v1 vs v2 vs v3 decision is grounded in operational needs and risk tolerance.
Core Differences at a Glance
When comparing smb v1 vs v2 vs v3, several non-negotiable distinctions emerge. First, security: v3 introduces built-in encryption and more robust signing options, whereas v1 offered little protection by default. Second, performance: v2 reduced protocol overhead and enabled more efficient metadata handling, and v3 builds on that with multi-channel and optional compression. Third, feature breadth: v3 adds resilience features like improved connection durability and enhanced renegotiation behavior, which matter under fluctuating networks. For administrators, this means that the upgrade path should be driven by security posture, regulatory requirements, and the need for reliability in multi-path environments. Finally, compatibility considerations: newer clients and NAS devices are optimized for v3, while some legacy systems still rely on v1, underscoring the importance of staged migration plans.
Security Enhancements Across Versions
Security is the most consequential axis in smb v1 vs v2 vs v3. SMB v1 offered basic access controls with little built-in encryption, making it vulnerable to interception and tampering on untrusted networks. SMB v2 brought improvements in negotiation and signing, reducing some risks and overhead but still relying on older cryptographic approaches. SMB v3 elevates security with per-connection encryption options, stronger cipher suites (AES-based), and improved signing behavior that helps ensure message integrity even on high-latency networks. In practice, organizations should aim to enable SMB v3 encryption for sensitive data and ensure that signing is enabled where required by policy. The Default Password team emphasizes that encryption alone is not a silver bullet; it must be paired with proper key management and periodic certificate rotation.
Performance and Scalability Differences
Performance characteristics significantly shape real-world outcomes when evaluating smb v1 vs v2 vs v3. SMB v1’s lack of overhead optimization often leads to higher CPU usage and slower performance on modern hardware. SMB v2 reduced chatty network traffic and improved file metadata handling, yielding noticeable efficiency gains, especially on larger shares and mixed workloads. SMB v3 expands on this by enabling multi-channel, which allows multiple network paths to concurrently transfer data, improving throughput and resilience in failover scenarios. Additionally, SMB v3 introduced improved file compression options and dynamic signing behavior that reduces CPU overhead during peak loads. In environments with virtualization or large-scale file shares, these enhancements translate into lower transfer times and more predictable performance.
Feature Comparison
| Feature | SMB v1 | SMB v2 | SMB v3 |
|---|---|---|---|
| Security features | Limited encryption by default or signing-only | Optional encryption and signing improvements | Per-connection encryption with strong cryptography; enhanced signing |
| Performance/Overhead | Higher overhead; older CPU optimizations | Lower overhead; better metadata handling | Further reduced overhead with multi-channel and compression |
| Multi-channel support | No | Limited or basic multi-path awareness | Full multi-path/multi-channel across NICs and paths |
| Encryption options | None by default | Optional encryption per connection | Mandatory encryption when negotiated, strong cryptography |
| Compatibility | Best with very old clients or legacy systems | Good cross-version compatibility with modern clients | Best for mixed environments with current hardware and NAS |
| Resilience & reliability | Basic reliability | Improved reliability over unstable networks | Enhanced resilience with faster renegotiation and failover |
| Deployment considerations | Legacy-only environments; high risk | Easier roll-out in controlled upgrades | Recommended baseline for new deployments |
Upsides
- Stronger security posture with SMB v3 encryption and signing
- Notable performance gains over SMB v1 and v2
- Improved reliability via multi-channel and resilient features
- Broader device compatibility with modern OS and NAS
- Granular control over encryption and signing per-path or per-share
The Bad
- Upgrade complexity and potential downtime during migration
- Encrypted traffic requires additional CPU and network resources
- Mixed-version environments can cause negotiation issues if not planned
- Legacy devices may require firmware or OS updates to support v3
SMB v3 is the recommended baseline for modern networks; SMB v1 should be retired, and SMB v2 serves as a viable intermediate if v3 is not yet deployable.
Prioritize SMB v3 for new deployments and during migrations to improve security and reliability. Use SMB v2 as a transitional step if necessary, and decommission SMB v1 to reduce risk.
Your Questions Answered
What are the main differences between SMB v1, v2, and v3?
The main differences lie in security, performance, and features. SMB v1 is legacy with minimal encryption. SMB v2 improves efficiency and reduces overhead. SMB v3 adds robust encryption, multi-channel, and resilience features to support modern networks.
SMB v3 includes encryption and multi-channel for safer, faster file sharing.
Is it safe to disable SMB v1 on a Windows network?
Disabling SMB v1 is generally recommended for security. Before disabling, audit clients and devices to confirm none rely on SMB v1. Plan a phased upgrade for any legacy systems that require SMB functionality.
Yes, but verify affected devices first.
Do Linux or macOS clients support SMB v3?
Yes. Modern Linux and macOS clients support SMB v3, and they can negotiate the highest mutually supported version with servers. Ensure that server configuration enables v3 and that clients are updated.
Yes, clients typically support SMB v3 when updated.
What are best practices for migrating from SMB v1 to v3?
Develop a staged plan: inventory devices, test in a lab, slowly enable v3 while keeping v1 disabled on non-critical shares, monitor performance, and implement fallback procedures. Maintain backups and document changes for rollback.
Test in a lab, then roll out in stages.
Does SMB v3 require new hardware to enable encryption?
SMB v3 encryption can run on standard hardware, but enabling it increases CPU usage. High-end NAS devices and server-grade NICs handle encryption more efficiently. Monitor CPU load during peak usage.
No mandatory new hardware, but hardware matters for performance.
Key Takeaways
- Disable SMB v1 on all devices
- Enable SMB v3 encryption for sensitive traffic
- Leverage SMB v3 multi-channel for higher throughput
- Plan migration with a staged rollout and rollback options
- Test compatibility before production cutover