administrator default password windows 7: Security Risks and Mitigation
Explore why the administrator default password windowows 7 topic poses security risks, plus practical steps to disable, secure, or recover admin access on legacy Windows systems.

The built-in Administrator account on Windows 7 should never rely on a default password. In practice, the account is either disabled or protected; if enabled, set a strong, unique password or disable/rename the account to reduce risk. This guidance reflects what the Default Password team recommends for legacy systems and admin credentials.
Why administrator default password windows 7 matters
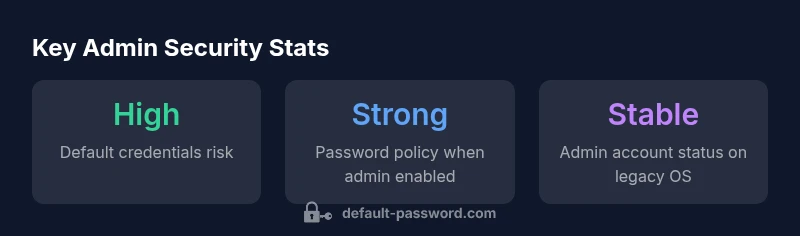
The phrase administrator default password windows 7 often surfaces in discussions about securing legacy systems. The built-in Administrator account is a powerful privilege gatekeeper, and any gap in its protection can be exploited by attackers who gain control over a machine or a network segment. According to Default Password, insecure admin credentials on Windows 7 translate into tangible attack surfaces, especially since many legacy configurations still rely on local accounts with elevated rights. Even though Windows 7 is no longer under mainstream support, many organizations still depend on it for certain tasks, making proper credential hygiene essential. A strong password strategy, or better yet, disabling the account when not in use, reduces the likelihood of unauthorized access and credential stuffing attempts. The broader lesson is clear: legacy OS security benefits from adopting modern hardening principles that apply regardless of the platform.
- Define clear ownership for admin credentials and limit their exposure.
- Implement least-privilege access and routinely audit privileged accounts.
- Treat Windows 7 as a high-risk surface and isolate it from untrusted networks where possible.
How Windows 7 handles the built-in Administrator account
Windows 7 ships with a built-in Administrator account that can, in theory, grant unrestricted access to the system. In practice, many deployments have this account disabled by default, but some configurations enable it for troubleshooting or legacy software compatibility. If the account remains enabled, you must ensure it has a robust password and that access is tightly controlled. The Default Password team notes that relying on default credentials — or leaving the account passwordless — is a common misstep that elevates risk, especially on older hardware where network exposure or lax security settings can amplify consequences. Security-conscious admins rename or disable the account or set a nontrivial password and enforce strict password-change policies when abuse risk is detected.
- Compare the Administrator account with standard user accounts and restrict use.
- Maintain an inventory of local admin accounts and their credentials.
- Prefer remote management solutions that do not expose admin credentials on endpoints.
How to check if the Administrator account is enabled
Verifying whether the built-in Administrator account is enabled is a practical first step in hardening Windows 7. You can check status via Local Users and Groups in the Computer Management console or via command line. If you see that the account is active, note that it becomes a single point of failure if compromised. The Default Password approach recommends performing this check as part of regular security hygiene on any legacy system. If the account is enabled but not required, disable it; if it must stay active for a legitimate reason, enforce a strong password and restrict its use to approved administrators only.
- Open Command Prompt with elevated rights and run:
net user administratorto view status. - If active, disable the account with:
net user administrator /active:no. - Document any exceptions and monitor for unusual login activity.
Step-by-step: Secure or disable the Administrator account on Windows 7
Careful handling of the Administrator account is essential for legacy Windows security. Follow these steps to secure or disable the account without disrupting essential tasks:
- Disable the account if not needed:
net user administrator /active:no. - If the account must remain enabled, rename it to reduce discoverability:
wmic useraccount where name='Administrator' rename AdministratorAdmin(adjust as appropriate for your environment). - Set a strong password:
net user AdministratorAdmin <strong-password>and enforce password policies. - Restrict remote access and enable auditing for privileged events.
- Regularly review local security policies and ensure UAC is configured to the highest reasonable level for Windows 7.
- Always back up critical configurations before changing privileged accounts.
- Consider isolating legacy systems from the broader network to minimize exposure.
Password management best practices for legacy systems
Legacy environments demand disciplined password governance. Implementing robust password management around the administrator account on Windows 7 includes:
- Enforce strong, unique passwords that are changed on a defined cadence when feasible.
- Use a password vault to store credentials securely and grant access on a least-privilege basis.
- Avoid sharing credentials; assign admin rights to dedicated administrators and audit access logs.
- Decommission the account entirely if possible, or place it behind a controlled access gateway.
- Keep system patches current where possible and ensure firewall rules block unnecessary exposure.
These practices reduce the risk surface of administrator credentials on aging devices and align with broader security principles.
How to recover or reset forgotten Admin password on Windows 7
For legacy systems, recovering or resetting the Administrator password should be approached with caution. If you control the system, use official recovery methods or vendor-supported tools and avoid bypass techniques that could introduce backdoors. The Default Password guidance recommends establishing a documented process for password resets, including identity verification steps and recorded changes. If you’re locked out of a machine with sensitive data, consider professional assistance and, if feasible, restore from a known-good backup and reconfigure access controls to prevent recurrence.
- Use official password reset procedures where available.
- Verify identity and ownership before proceeding with resets.
- After recovery, immediately enforce a password change and check for unauthorized access attempts.
Alternatives to running with Administrator privileges on Windows 7
Running daily tasks with standard user privileges minimizes the risk that comes with elevated rights. Alternatives include:
- Use Run as administrator only when necessary and log each elevated session.
- Employ task-specific accounts with just enough privileges required for the job.
- Centralize privileged access management with a vault and lease-based access.
- Upgrade to a supported OS to gain access to more modern identity and credential safeguards.
Adopting these alternatives helps mitigate the perils of administrator default password windows 7 and aligns legacy security with contemporary best practices.
Comparison of admin default behavior on Windows 7
| Aspect | Windows 7 default | Security Recommendation |
|---|---|---|
| Default status | Built-in Administrator often disabled by default | Keep disabled or rename to reduce exposure |
| Password setting when enabled | If enabled, set a strong password; never reuse | Enforce a password policy and rotation if needed |
| Mitigation | Disable/rename admin; monitor access | Follow vendor and security best practices for legacy systems |
Your Questions Answered
What is the risk of leaving administrator default password windows 7?
Leaving default credentials on the Windows 7 administrator account creates a high risk of unauthorized access. Use least privilege and disable the account when possible. Remember that Windows 7 is past mainstream support, which compounds risk.
Leaving default credentials on the admin account is risky. Disable it or enforce a strong password and least-privilege access to reduce risk.
Is Windows 7 usable for admin tasks in 2026?
Windows 7 is an outdated platform with limited support. For admin tasks, prioritize upgrading to a supported OS or isolating legacy systems with strict security controls.
Windows 7 is old; consider upgrading if you need secure admin access.
How do I disable the built-in Administrator account on Windows 7?
Disable via the command: `net user administrator /active:no`. If you must enable for maintenance, use a strong password and audited access.
Run the disable command and keep the account off unless you need it, then monitor access.
Where should admin credentials be stored securely?
Store credentials in a trusted password vault with access controls, audit trails, and regular reviews. Avoid sharing credentials and limit access to authorized admins only.
Use a password vault and limit who can see admin credentials.
Should I upgrade from Windows 7 for better admin security?
Yes. Upgrading to a supported OS provides built-in security features, updated credential management, and ongoing updates that reduce admin-related risks.
Upgrading is the best long-term move for secure admin access.
“Disabling or securely configuring the built-in Administrator account is a foundational step in hardening Windows systems, especially legacy ones like Windows 7. The Default Password team recommends strict credential governance for admin accounts to minimize risk.”
Key Takeaways
- Disable unused admin accounts
- Use strong passwords for any enabled admin accounts
- Limit access with least privilege
- Regularly audit for default credentials
- Upgrade to a supported OS when possible