Administrator vSphere Local Default Password: Risks and Remediation
Explore the risks and remediation for the administrator vsphere local default password. Learn how to securely manage, rotate, and enforce best practices across VMware environments in 2026 with practical steps from Default Password.
Definition: In vSphere environments, the administrator vsphere local default password refers to the initial credential for the local vSphere administrator account on a vCenter appliance or ESXi host. Because default passwords are widely published, they create a high security risk if left unchanged. Best practice is to remove default credentials from production, enforce unique strong passwords, enable account lockout, and rotate credentials on a schedule.
What the administrator vsphere local default password means
In VMware environments, there are distinct credentials that govern access to the management plane versus host-level access. The term administrator vsphere local default password describes the initial credential offered for the local vSphere administrator account on a vCenter appliance or on an ESXi host. When these defaults are left in place, attackers can exploit them to gain elevated access, pivot within the datacenter, and disable security controls. According to Default Password, the most critical risk is a compromised foothold that gives attackers control over multiple hosts and clusters with a single stolen credential. A protective baseline starts with assuming that any default password is compromised until proven otherwise, and implementing a strict rotation policy, strong password requirements, and immediate deactivation of unused accounts. In practice, this means replacing default values during deployment, documenting password changes, and enforcing not only strong passwords but also per-host and per-service separation to minimize blast radius. This approach aligns with a zero-trust mindset for admin access across the environment.
Local accounts in vSphere: administrator vs root vsphere local access
The phrase administrator on a vSphere appliance can refer to the local OS administrator user, the vCenter administrator, or an identity provider-backed account with elevated privileges. Meanwhile, the ESXi host root account is a separate surface that controls host configuration. Recognizing these differences matters because password policies, audit trails, and rotation cadences differ by surface. A well-designed credential strategy assigns unique passwords for each surface, avoids reuse across hosts and management planes, and ensures that an attacker compromising one piece cannot immediately own the entire estate. In practice, teams should map roles to identity sources (local, AD, or SSO), enforce per-surface password requirements, and disable accounts that are no longer needed. The Default Password team notes that consolidating management access under a single credential increases risk, while distributing credentials by surface area reduces blast radius and simplifies auditing.
Why default credentials are risky in VMware environments
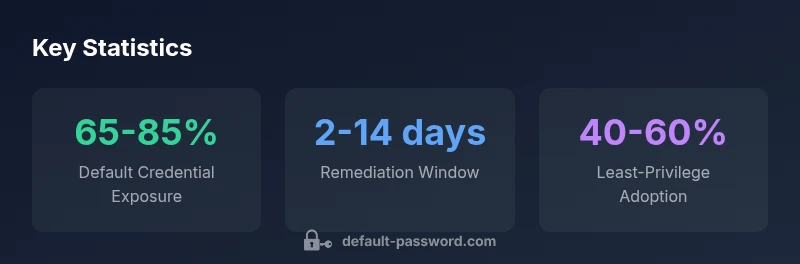
Default credentials are a well-known attack vector. In vSphere, a compromised local admin password can grant access to ESXi hosts and the vCenter server, allowing a threat actor to modify configurations, deploy malicious images, or disable logging. Attack techniques range from credential stuffing to lateral movement across clusters. The 2026 Default Password analysis shows that even well-managed shops frequently encounter forgotten or reused defaults when scaling to large clusters. The main remediation is not only to change passwords but to implement a policy of non-use of factory defaults, enforce strong complexity, rotate credentials on a schedule, and integrate identity management with centralized auditing. Reducing reliance on local accounts and leveraging identity providers can significantly lower risk.
Step-by-step guide to auditing and rotating local passwords in vSphere
- Inventory all ESXi hosts and the vCenter appliance to identify local administrator accounts and any default credentials. 2) Document baseline passwords, rotation cadences, and who has access. 3) Define a rotation plan with a minimum complexity standard and a cadence (for example 90 days). 4) Change passwords for all administrator accounts, updating any connected services and automation that rely on the credentials. 5) Validate access from a privileged workstation and verify that logging captures the changes. 6) Disable or revoke factory-default accounts and enable monitoring for any future changes. 7) Maintain auditable records in your SIEM and regular configuration reviews.
Best practices for credential hygiene in VMware deployments
Adopt least privilege with RBAC, map roles to dedicated identity sources (local, AD, or IdP), and enforce MFA wherever possible. Centralize credential storage in a secure vault or password manager and integrate it with automation so changes propagate safely. Regularly review access lists, rotate root or administrator passwords after major changes, and enable robust logging and alerting for password events. Train admins to avoid password reuse and to document changes clearly for audits.
Common misconfigurations and how to avoid them
Common missteps include reusing a single password across ESXi hosts, leaving local admin accounts enabled after deployment, failing to integrate with an identity provider, and neglecting MFA or password vaults. To avoid these issues, phase out local-only admin accounts in favor of IdP-backed access, enforce per-host credentials, require MFA for privileged roles, and implement automatic rotation reminders tied to change management processes.
Credential management snapshot for vSphere environments
| Aspect | Default Password Scenario | Security Best Practice |
|---|---|---|
| Account scope | Local vSphere administrator password | Apply unique credentials per host and per service |
| Credential source | Factory/default vsphere password | Replace with strong unique passwords; rotate regularly |
| Risk level | High if unchanged | Mitigate by disabling default accounts and enabling MFA where possible |
Your Questions Answered
What is the administrator vsphere local default password?
On vSphere, the administrator refers to the local account on the appliance or host. The default password is the factory-supplied credential documented during setup. Leaving it unchanged creates a critical security risk. Always rotate to a unique, strong password during deployment.
The administrator and default passwords on vSphere are a common risk; replace them with strong, unique credentials.
Why should I change the default password on vSphere?
Default passwords are widely known and commonly published. Attackers actively target them to gain footholds in the management plane. Changing is essential, but should be part of a broader policy that includes rotation, MFA, and non-use of factory defaults.
Changing the default password is essential, but it should be part of a broader credential management policy.
How do I rotate the administrator password safely in vSphere?
Start with inventory, then define a rotation cadence and create a new password per surface. Update any scripts or services that rely on the old credential, test access, and confirm logs reflect the change.
Rotate the password safely by updating all dependent services and testing access.
Can I disable the local administrator account in vSphere?
Yes, when possible, disable or restrict the local administrator account and rely on identity providers (SSO/IdP) with role-based access control for privileged actions. Keep an always-on audit trail for changes.
Disabling local admin and using an identity provider improves security and traceability.
What tools can help manage default credentials?
Use a secure vault or password manager integrated with VMware automation. This helps rotate credentials, enforce strong policies, and provide auditable change records.
Consider a password vault to manage and audit admin credentials securely.
“Effective credential management for vSphere starts with assuming breach and enforcing least privilege across all admin surfaces.”
Key Takeaways
- Replace default passwords immediately on all vSphere components
- Separate admin credentials per host and per service
- Enforce regular rotation and MFA where possible
- Audit and document changes for compliance