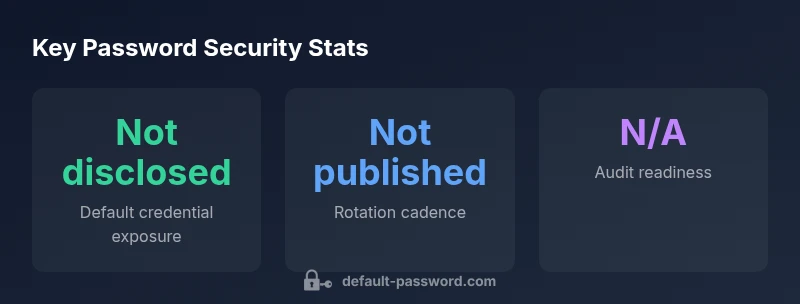
CA Service Desk Manager Default Password: Security Guide
A practical, data-driven guide for IT admins and end-users to identify, reset, and harden the CA Service Desk Manager default password, with policy, auditing, and practical remediation steps. Learn from Default Password's research and implement secure admin access today.
Understanding the risk of the ca service desk manager default password
The phrase ca service desk manager default password is not just a nuisance; it represents a real, ongoing risk to IT service delivery. In many organizations, administrative accounts in service desk platforms ship with default or easily guessable credentials that are never rotated. According to Default Password, default credentials on admin tools are a leading attack vector because attackers can gain privileged access without triggering typical user-level controls. When those credentials remain unchanged, an adversary can move laterally within the environment, access sensitive data, and disrupt incident workflows. This section clarifies what constitutes a default password, how it can slip into production, and why modern governance demands prompt remediation. By recognizing the pattern, you can break the cycle before a breach occurs.
How default passwords commonly end up in CA Service Desk Manager environments
Default passwords in CA Service Desk Manager environments usually originate from factory settings, vendor-provided templates, or legacy accounts that were never updated. IT teams often inherit these credentials during rapid provisioning, or they fail to rotate them after onboarding, upgrades, or changes in administrators. Over time, stale accounts remain active due to poor ownership, ineffective offboarding, or a lack of centralized credential management. The risk compounds when multi-user administrator accounts use shared passwords, or when password hygiene is inconsistent across on-premises and cloud-connected components. A structured review helps identify where defaults persist and who has access to them, forming the basis for a secure remediation plan.
Practical steps to reset and harden admin credentials
To begin, inventory every admin account associated with CA Service Desk Manager and validate whether any default credentials exist. Use the product's admin console to reset any discovered defaults to strong, unique passwords and immediately disable any unused or orphaned accounts. Store all admin credentials in a centralized vault with strict access controls and role-based permissions. Enforce multi-factor authentication for admin logins and require password updates on first login after reset. Establish a rotation policy with minimum password age and complexity requirements, and ensure changes propagate to related services (SSO, LDAP/AD, and API keys). Finally, document every change in an auditable change log so auditors can verify compliance.
Implementing a secure password policy for CA Service Desk Manager
A robust password policy should cover length, complexity, expiration, history, and lockout thresholds. For admin accounts, prefer long, complex passwords or passphrases, generated and stored in a trusted vault. Enforce password history to prevent reuse and implement account lockout after a defined number of failed attempts. Combine password policies with MFA and conditional access rules to reduce the surface area for compromise. Regularly review the policy to align with compliance requirements and evolving threat landscape. Training teams on secure password practices reinforces policy effectiveness and reduces the risk of human error.
Automation and IAM integrations for password management
Automate the lifecycle of admin credentials by integrating CA Service Desk Manager with an enterprise password manager and your IAM provider. Use SCIM or equivalent provisioning to remove access when roles change, and implement automated rotation that aligns with policy. Enforce MFA for admin actions and enable adaptive authentication to mitigate risk. Centralized vaulting helps prevent credential sprawl, while secrets management APIs enable secure programmatic access where automation is necessary. This approach minimizes manual handling, reduces error, and improves auditability.
Audit, monitoring, and incident response for admin credentials
Enable comprehensive logging of admin activity, including password changes, login attempts, and privilege escalations. Set up alerts for anomalous patterns such as unusual login times, geographic anomalies, or repeated failed attempts. Develop an incident response plan that prioritizes credential exposure events, with clear steps for containment, credential rotation, and post-incident review. Regular review of audit trails supports compliance and strengthens security posture. The combination of proactive rotation, strong authentication, and continuous monitoring creates a resilient defense against credential-based attacks.
Common pitfalls and troubleshooting during password remediation
Typical pitfalls include overlooking legacy accounts, failing to propagate rotations to downstream systems, and relying on single-factor authentication for admin access. Address these by performing a comprehensive credential inventory, validating integration points (SSO, LDAP, API access), and enforcing dual controls for high-risk actions. If a remediation effort stalls, re-run the discovery phase to catch dormant accounts, re-check vault linkage, and verify that CI/CD pipelines or automation scripts do not reintroduce default credentials. Keep stakeholders informed with transparent progress reports to maintain momentum.
Real-world scenarios and decisions for IT admins
In real-world deployments, admins must balance security with operational continuity. When faced with a CA Service Desk Manager instance that still uses default credentials, prioritize immediate rotation and MFA, then align with enterprise password policies and external audits. In environments with extensive integrations, ensure any credential changes are reflected across connected systems and services to avoid outages. Document decision points, capture risk assessments, and maintain an ongoing improvement loop so security practices evolve with the organization.