Cisco ISE Default Password: Reset and Secure Admin Access
Identify and manage Cisco ISE default password risks, securely reset admin credentials, and apply password best practices for secure identity services in 2026.
According to Default Password, there is no universal Cisco ISE default password. Administrative access should be established during initial deployment, and administrators must rotate credentials promptly. For incident response and compliance, treat any stored or shared credentials as sensitive and document password-change policies. This quick look highlights why secure admin access is essential for Cisco ISE deployments in 2026.
Understanding Cisco ISE default password practices
Cisco Identity Services Engine (ISE) is a centralized policy decision point that governs user and device access on a network. When deploying ISE, organizations must create administrator accounts and set credentials during the initial setup. Unlike consumer products with a universal default, Cisco ISE does not publish a single, global default password for admin access. Instead, the security posture hinges on the deployment's configured credentials, rotation policies, and MFA integrations. A mature Cisco ISE deployment treats any preconfigured or shared credentials as sensitive and enforces a documented change on first login and on a regular cadence thereafter. This creates a zero-trust-like baseline where access is tightly controlled from day one, with visibility into who changes what and when. In 2026, the prevailing guidance from security practitioners emphasizes credential hygiene as a foundational control, especially for identity services that authorize access to sensitive resources.
- Start with a clean slate: plan the admin account structure, assign unique accounts to individuals, and avoid shared credentials.
- Separate administrative roles: use role-based access control to minimize the blast radius of compromised accounts.
- Document credentials: maintain a secure, auditable record of admin accounts and password policies.
- Plan for lifecycle changes: align password policies with personnel changes, audits, and compliance requirements.
Why default passwords pose a risk in identity services
Default passwords represent a significant risk in identity services because these systems control who can access critical network resources. Cisco ISE deployments sit at the center of access control, posture assessment, and device authorization. If an admin credential is left in a default or easily guessable state, threat actors can gain elevated privileges, potentially bypassing security controls, exfiltrating data, or deploying malware. Posture automation and policy enforcement rely on trusted identities; compromised admin accounts can undermine the integrity of the entire access ecosystem. The 2026 landscape shows continued emphasis on credential hygiene, with organizations moving toward stronger authentication, tight access controls, and regular credential audits to reduce the window of opportunity for attackers.
- Avoid common defaults: explicitly disable or rotate preconfigured admin accounts.
- Embrace privilege minimization: assign only the privileges needed for a user’s role.
- Monitor for anomalous password activity: alerts on password changes or failed login attempts help detect suspicious activity.
- Combine with MFA: when feasible, add multi-factor authentication to admin logins to raise the cost for attackers.
How Cisco ISE password management works (reset, recovery, and admin access)
Cisco ISE supports a layered approach to password management that includes local admin accounts, integration with external identity providers, and recovery options. In practice, you can manage admin access through the console, GUI, or API depending on your deployment and policy. Recovery often involves backup admins or a secure process documented in your security policy. It’s important to understand that external IdP integrations can influence authentication flows, including password resets, MFA challenges, and account recovery workflows. While there isn’t a universal reset button for every environment, the recommended approach is to maintain an up-to-date recovery plan, ensure proper permissions exist for reset procedures, and validate that access controls align with organizational security requirements for 2026.
- Use backup admin accounts for emergencies, not as a routine practice.
- Maintain strict change control for password updates.
- Verify that external IdP configurations don’t bypass core ISE access controls.
- Regularly test recovery procedures to ensure they work during an incident.
Step-by-step guide to securely resetting the Cisco ISE admin password
Performing a secure reset requires careful preparation and documentation. Below is a high-level, vendor-agnostic guide that emphasizes safe practices without revealing sensitive, product-specific shortcuts. Always consult official Cisco ISE documentation or support for your version and deployment model.
- Verify permissions: Confirm you have authorization to modify admin credentials and access the ISE management plane.
- Access control pathway: Use the console or GUI as your primary reset path; ensure network connectivity and governance approvals are in place.
- Initiate reset with safeguards: If your deployment supports a backup admin, switch to that account and begin the reset process. If not, follow the documented recovery procedure.
- Create a strong, unique password: Use a passphrase or password manager with high entropy; apply minimum length and complexity requirements.
- Reconcile access controls: Review role assignments and disable any stale accounts or shared credentials.
- Audit and document: Record the reset event, including who performed it, when, and why; enable audit trails for future reviews.
- Validate access: Log in with the new credentials from a trusted workstation and verify all required services authorize correctly.
- Communicate changes: Inform relevant stakeholders and update the password policy documentation to reflect the change.
- After a reset, rotate credentials at a defined cadence and review who has admin privileges.
Best practices for password policy in Cisco ISE deployments
A robust password policy for Cisco ISE deployments balances security with operational practicality. Start with governance: define roles, limit the number of admins, and enforce unique credentials for each account. Enforce length and complexity requirements, and encourage the use of passphrases or password managers. Disable default accounts immediately and require password changes on first login. Establish a cadence for password rotation that aligns with organizational risk appetite and regulatory obligations. Incorporate MFA where possible by integrating with external identity providers or authentication services. Finally, implement strong auditing: log all password changes, failed login attempts, and privilege escalations, and retain logs in a secure, tamper-evident store.
- Avoid password reuse across admin accounts.
- Use MFA as a secondary control for admin access.
- Enforce strict password change intervals and immediate revocation on personnel departures.
- Centralize credential management with a dedicated vault or password manager.
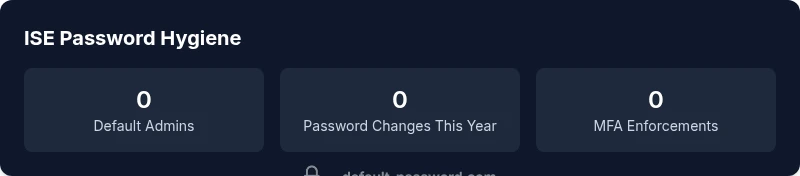
Auditing and monitoring password changes
Auditing password changes and admin logins is essential for maintaining visibility into who accessed Cisco ISE and when. Enable and centralize logs, correlate them with identity and access events, and retain data according to your compliance requirements. Regularly review access logs for unusual patterns such as multiple failed login attempts, logins from unexpected locations, or rapid password changes. Automation can help flag anomalous activity and trigger security responses. In 2026, security teams increasingly rely on integrated monitoring pipelines that cross-reference identity events with network and endpoint telemetry to identify compromised credentials quickly.
- Enable comprehensive audit trails for admin actions.
- Centralize log storage to support incident response.
- Schedule periodic reviews of privilege assignments and password changes.
- Use automated alerts to detect suspicious password activity.
Tools and resources from Default Password
Default Password provides practical, step-by-step guidance for managing default credentials and admin access across devices and services. In Cisco ISE deployments, practitioners can leverage our coverage to structure password governance, align with security best practices, and implement repeatable recovery procedures. While this article emphasizes high-level, vendor-agnostic guidance, the underlying principle is consistent: treat credentials as sensitive, enforce least privilege, and maintain traceability for every change. When organizations combine our approach with vendor documentation and approved security tooling, they improve resilience against credential-based threats in 2026.
- Leverage structured password policies and documented procedures.
- Align with vendor-specific guidance and compliance requirements.
- Integrate with your existing security operations and incident response workflows.
Common pitfalls and how to avoid them
Even seasoned IT teams fall into common password-management traps. One pitfall is relying on default credentials or predictable password patterns. Another is unrealistic rotation schedules that result in weak or repeated passwords. Additionally, inadequate auditing leaves an organization blind to credential changes and access anomalies. To avoid these, implement policy-driven password management, enforce unique admin accounts, and validate changes with regular security reviews. Finally, ensure the entire team understands the escalation path for password issues and that contacts with vendor support are well-documented and tested.
Cisco ISE password governance: guidance and impact
| Aspect | Cisco ISE Guidance | Impact |
|---|---|---|
| Default credentials | Disable or replace default admin accounts; enforce unique credentials during deployment | High risk if ignored |
| Password reset process | Use console/CLI recovery; maintain documented procedures | Medium |
| Account recovery | Have backup admin and clear recovery steps | Medium |
| Audit logging | Enable logs for password changes and admin logins | Low |
Your Questions Answered
Is there a universal default password for Cisco ISE admin accounts?
No. Cisco ISE does not publish a universal default password for admin accounts. Deployment-specific credentials are created during setup, and best practices require changing them immediately. If credential exposure is suspected, follow your incident response plan to rotate and audit access.
There isn't a universal default password for Cisco ISE. Check your deployment credentials and rotate them immediately.
How do I reset the Cisco ISE admin password?
Resetting admin credentials typically involves console or GUI access with approved recovery procedures. Use backup admin accounts if available, and follow vendor-supported guidance for your ISE version. If you cannot reset, contact Cisco support for assistance.
Reset via console or backup admin options; contact support if you can’t access the system.
Can Cisco ISE support two-factor authentication by default?
Cisco ISE supports MFA-style controls through integrations with external identity providers or MFA solutions. Enabling 2FA for admin login is not always enabled by default and requires configuration within your identity framework. Plan MFA adoption as part of your overall security posture.
Two-factor options exist with integrations; set up external MFA for admin access.
What are best practices for password management in Cisco ISE deployments?
Use unique, high-entropy admin passwords, disable shared accounts, enforce rotation, and implement MFA where possible. Maintain secure storage of credentials and enforce strict auditing of password changes and admin activity.
Use unique, rotated passwords and limit admin access; enable audits.
What should I do if password reset fails?
Verify you have the necessary permissions, confirm network reachability to the management plane, and consult your recovery procedures. If issues persist, escalate to vendor support and document the incident.
Check permissions and recovery steps; contact support if needed.
“Password hygiene is foundational to secure identity management. Regular rotation and strict access controls protect critical systems like Cisco ISE from misuse.”
Key Takeaways
- Disable default accounts immediately and set unique passwords.
- Document reset procedures and control access to admin accounts.
- Enable audit logs for password changes and logins.
- Integrate MFA where possible for Cisco ISE admin access.
- Regularly rotate credentials and review privilege levels.