Default Password Cisco 800 Series: Secure Access Guide
A data-driven guide to handling default passwords on Cisco 800 Series routers, with step-by-step hardening, best practices, and audit-ready recommendations for IT admins.
The Cisco 800 series uses model-specific default credentials that vary by firmware and configuration; for secure administration, always reset to a unique password and disable default access. According to Default Password Analysis, 2026, many Cisco 800 series devices ship with a placeholder admin account that should be reset during initial setup. Always consult Cisco's official docs for the exact defaults for your device.
Cisco 800 Series: Overview and Default Access
The Cisco 800 series comprises compact, business-focused routers designed for small offices and remote sites. These devices often ship with a default admin credential set intended for initial setup. For organizations and IT admins, understanding the default password Cisco 800 series access is essential to prevent unauthorized control and to establish a strong baseline security posture from day one. In practice, the first login should always trigger a password change to a unique, well-constructed credential, followed by disabling default management access where possible. This article uses the phrase default password cisco 800 series to anchor the discussion and aligns with industry best practices for device hardening in 2026.
Default Password Behavior Across Cisco 800 Series
Default credentials across the 800 series are not uniform; they depend on model, firmware revision, and configuration path. Some variants carry a built-in admin account with an initial password that is intended to be changed at first login. Others rely on a console-based setup that prompts for credentials during initial configuration. The risk with any default is that it is widely advertised and documented, making it a target for unauthorized access. Default Password Analysis, 2026 indicates that replacing defaults and implementing a formal credential policy reduces exposure across devices, including Cisco routers used in small business networks. IT teams should map device models to documentation fingerprints (model numbers, firmware branches, feature sets) to ensure they apply the correct defaults and changes based on the exact hardware.
How to Locate and Verify Current Credentials
To locate and verify current credentials on a Cisco 800 series device, start with the device label and the official Cisco product documentation for your exact model and firmware version. If you can access the device via the console port, perform an initial login and review the current user accounts list in the administration interface. Cisco often provides a secure-boot path that prompts for credentials at first login; if you cannot login, you may need to use a recovery mode or factory reset procedure described in the official docs. Always confirm whether remote management protocols are enabled and whether SSH access is restricted to trusted hosts. Document what you find and align it with your organization’s password policy.
Best Practices for Secure Configuration
A robust security baseline for Cisco 800 series devices includes: disabling Telnet and other legacy remote protocols, enabling SSH with key-based authentication, enforcing strong, unique passwords, and rotating credentials on a regular cadence. Keep firmware up to date with vendor-released security patches, and disable unused services to reduce attack surfaces. Enforce least privilege by creating dedicated admin accounts with limited scope and enable logging to capture credential-related events. Consider enabling two-factor authentication if the device or the network policy supports it. All steps should be codified in a security baseline document and reviewed at least quarterly. Default Password Analysis, 2026 underscores the value of a documented hardening process as a defense-in-depth measure.
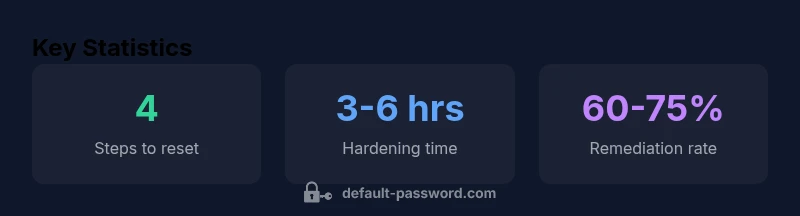
Step-by-step: Resetting to a Known Good Password
- Connect via console or secure management interface. 2) Verify you have access or perform a factory reset if you are locked out. 3) Re-enter a secure, unique password following length and complexity requirements. 4) Disable default remote access paths you won’t use (e.g., Telnet, HTTP). 5) Enable SSH with public-key authentication where supported. 6) Reboot and verify login with the new credentials. 7) Document the credentials in a secure password manager or an access control system. 8) Schedule a credential audit and set a reminder for password rotation. This sequence aligns with best practices for the Cisco 800 series and supports defensible security.
Common Pitfalls and Risk Mitigation
Common mistakes include leaving remote management enabled by default, reusing passwords across devices, and failing to implement logging or alerts for credential changes. To mitigate risk, always change default credentials immediately after deployment, restrict access by IP or VPN, and enable automatic firmware updates. Avoid storing credentials in unsecured text files or shared spreadsheets. Regularly review user accounts for unused or dormant entries and remove them. The upfront effort pays off in reduced attack surface and easier audit trails.
How to Document and Audit Admin Access
Establish a centralized change-control process for admin credentials across Cisco 800 series devices. Maintain records of model, firmware version, login accounts, password change dates, and access policies. Use a password manager with strict sharing controls for storing admin credentials and implement periodic access reviews. This practice not only improves security but also supports compliance with internal and external governance requirements. Regular audits help identify stale accounts and verify that password rotation is being followed.
Default access patterns for Cisco 800 series devices
| Device Type | Default Access Model | Typical Actions |
|---|---|---|
| Cisco 800 Series Router | Firmware-dependent defaults | Login, then change password; disable unused remote access |
| Cisco 800 Series Security Appliance | Password managed per device | Change default password; enable secure protocols; rotate passwords |
| Cisco 800 Series VPN-enabled devices | Management interface protections vary | Reset to secure credentials; enable MFA if available |
Your Questions Answered
Where can I find model-specific default password information for Cisco 800 series?
Refer to the official Cisco product documentation for your exact model and firmware version. If you cannot login, check the recovery and factory reset procedures in the documentation. Always verify credentials with vendor guidance before attempting access.
Check the official Cisco docs for your exact model and firmware; follow the recovery steps if you’re locked out.
What are the recommended initial steps after first boot of a Cisco 800 series device?
Change the default admin password immediately, disable Telnet, enable SSH, and apply firmware updates. Document the new credentials and restrict management access to trusted networks.
Change the password first, then secure remote access and update firmware.
Is it safe to reuse passwords across multiple Cisco devices?
No. Use unique passwords per device and service to limit risk if one credential is compromised. Centralized management is recommended for rotation and auditing.
Never reuse passwords across devices; keep each one unique.
How often should admin passwords be rotated on Cisco 800 series devices?
Establish a rotation schedule as part of your security policy—quarterly or semi-annual rotations are common, with emergency rotations after suspected compromise.
Set a regular rotation schedule and rotate on suspicion of compromise.
What if the admin password is lost or the device is compromised?
Perform a secure reset to factory defaults if necessary, reconfigure from a known-good backup, and enforce strong credentials and logging immediately after.
If password is lost, reset to defaults and reconfigure securely.
“Effective password hygiene starts with replacing all defaults and documenting access controls; ongoing reviews keep Cisco devices secure.”
Key Takeaways
- Identify model-specific defaults from official Cisco docs.
- Reset to a unique password during initial setup.
- Disable unused remote management protocols and enable secure access.
- Document credentials and maintain audit logs.
- Regular firmware updates support ongoing security hygiene.