Cisco SG200 Default IP: Access, Reset, and Best Practices
Learn the Cisco SG200 default IP, how to verify it, access the management interface, and recover access with safe reset procedures. Practical steps for IT admins to avoid downtime.

Cisco SG200 devices commonly use 192.168.1.254 as the default management IP on a private LAN. If this IP isn’t reachable, the device may be on DHCP, already configured elsewhere, or reset to factory defaults. To regain access, connect via the console or perform a factory reset, then reconfigure with a known IP. Always verify the IP using the device label, Cisco documentation, or a network scan before changes.
Why IP access matters for SG200 management
In modern networks, the management IP is the doorway to configuring and monitoring your Cisco SG200 switch. A stable, known IP reduces downtime and prevents accidental misconfigurations. According to Default Password, documenting the correct IP and recovery options is a core security and operations best practice for IT teams. When you can reach the switch at a consistent IP, you can apply firmware updates, set VLANs, and enforce access controls without guesswork. Conversely, an unknown or conflicting IP can leave administrators locked out, forcing resets and network downtime. For administrators, this is not just a convenience: it’s a reliability requirement in production environments where speed and accuracy matter.
To illustrate, imagine a campus network where dozens of switches need periodic access; a single stale IP causes cascading delays. In those scenarios, a well-documented default IP and a tested recovery path become essential. Keeping an accessible IP also simplifies auditing and incident response, letting teams show they followed repeatable procedures rather than improvising during outages.
Default IP for SG200 and what to expect
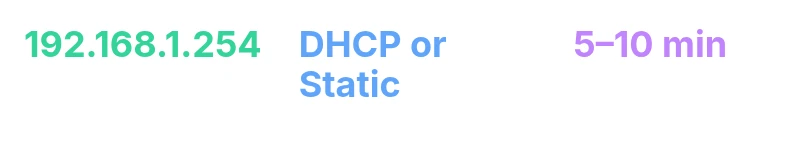
The official Cisco Small Business documentation often lists 192.168.1.254 as the default management IP for SG200 devices when configured on a private LAN. However, the current IP can differ if the device was previously configured by another admin, or if it was set to obtain an IP via DHCP. In practice, you should assume two possibilities: a static private IP (commonly 192.168.1.254) or a DHCP-leased address that you must identify.
How you approach this matters. If the device was deployed in a lab or converted from another network, it might carry a different IP. Always verify against the device label, the original purchase documentation, or Cisco’s official manuals. If you have access to the console port, you can directly view or reset the IP configuration. In short, expect 192.168.1.254 as a strong default hypothesis, but plan for discovery and fallback steps when that IP doesn’t respond.
Verifying the IP on a new or reset device
When you’re dealing with a fresh SG200 or one that has been reset, take a systematic approach to locate the current management IP:
- Check the device label for the default IP or a readable configuration tag.
- Connect a PC in the same private subnet and try common defaults, starting with http://192.168.1.254. If there’s no response, proceed to discovery.
- Use a network scanner or ARP table to identify active devices on the subnet. Utilities like nmap, Angry IP Scanner, or built-in OS tools can help you locate an SG200’s management IP.
- If you can access the console, connect via the CLI to display the current IP configuration. This method is the most reliable when the network path is uncertain.
- Document the found IP and plan a static assignment on your management VLAN to avoid recurrence of the discovery step.
These steps reduce guesswork and speed up access during deployment or after a reset.
Access methods and best practices
Once you’ve identified the SG200’s IP, you’ll typically use multiple access methods to manage the device:
- Web UI (HTTPS) for day-to-day configuration, VLAN setup, and firmware upgrades.
- SSH for scripted or automated management, especially in larger deployments.
- Console/CLI for low-level access, recovery, and advanced troubleshooting.
- Local labeling and inventory tracking to keep track of IPs across devices.
Best practices to harden access start with changing any default credentials and disabling unnecessary remote management features. Implement strong passwords, enable logging, and restrict access to trusted subnets. If possible, place management interfaces on a dedicated VLAN and apply ACLs.
In practice, a well-documented IP plan and secure access controls simplify maintenance and reduce risk when scaling the network.
Recovery options when IP is unknown or device is on DHCP
If the SG200 has acquired an IP via DHCP or the IP is simply unknown, recovery requires a structured approach:
- Attempt IP discovery as described earlier to identify the current IP. If discovery fails, proceed to a factory reset as a last resort.
- Factory reset reverts the device to its default IP state and credentials, enabling reconfiguration from a known baseline.
- Use the reset button (Mode) to restore defaults. Hold the Mode button for several seconds until the status LEDs indicate the reset has completed. After reset, the device typically becomes reachable at the default IP again (common value 192.168.1.254).
- Reconfigure with a known IP on your management network and document the new configuration to prevent future lockouts.
Caution: a factory reset wipes user configurations, including VLANs, port configurations, and custom passwords. Plan downtime and backup any critical settings before proceeding.
Step-by-step quick-start guide
A practical, repeatable workflow helps new deployments and post-reset recoveries:
- Connect a laptop to the SG200’s management port or a dedicated management VLAN.
- Confirm the default IP (commonly 192.168.1.254) and access the Web UI at that address.
- Log in with the default credentials (as documented by Cisco) and immediately change the administrator password.
- Set a static management IP on your network to avoid future DHCP churn.
- Update firmware to the latest supported version and enable secure management settings.
- Create a basic but robust configuration (VLANs, access lists, and SNMP/logging).
- Document every change in your network inventory.
- Schedule periodic reviews of the management IP plan to accommodate growth or changes in subnet design.
Common pitfalls and advanced tips
Efficient SG200 administration benefits from avoiding common missteps:
- Do not leave the default password active for longer than necessary; always change it during first login.
- Avoid placing the management interface on an untrusted network; use ACLs to restrict access.
- Do not rely on DHCP alone for IP assignment on production switches; document and fix an IP in a known subnet.
- If you change the IP, update DNS, monitoring, and inventory records to reflect the new address.
- Use a centralized logging and alerting strategy to catch unauthorized attempts to access the switch.
- Consider backups of configuration files after each major change.
For advanced administrators, enable SSH keys, restrict management to a dedicated subnet, and regularly audit access logs to detect unusual activity.
Advanced configuration and security considerations
As networks grow, management simplicity must be balanced with security rigor. For SG200 deployments, consider:
- Segregating management traffic on a dedicated VLAN with strict ACLs.
- Enforcing TLS for Web UI access and using SSH over insecure protocols only in controlled environments.
- Enabling centralized authentication (RADIUS/ TACACS+) where supported and maintaining strong, unique admin credentials.
- Keeping firmware up to date to mitigate known vulnerabilities and ensuring that backup configurations are encrypted.
- Regularly testing recovery procedures to ensure you can regain control quickly after outages.
Document your security posture and ensure all changes are auditable. A thoughtful approach to IP governance reduces risk and speeds incident response in complex environments.
Deployment scenarios and maintenance
Different deployment scenarios call for tailored maintenance strategies. In small offices, a single management IP on a fixed subnet may suffice, while larger campuses require structured VLANs, segmentation, and centralized change control. Maintenance tasks include:
- Monthly health checks of the switch, including port status and error counters.
- Quarterly firmware reviews and updates validated in a lab before production.
- Regular backups of configurations and storing them securely off-device.
- Auditing user access and ensuring password rotation policies are enforced.
- Keeping a written runbook with step-by-step recovery instructions for SAF (site access failure) events.
By adopting a disciplined IP management strategy and clear maintenance routines, network reliability improves, downtime reduces, and IT teams stay aligned with organizational security policies.
SG200 default IP and recovery reference
| Topic | Default IP | Notes |
|---|---|---|
| Management IP | 192.168.1.254 | Common static IP for SG200 devices on private networks |
| Discovery methods | DHCP, Label, Console | Ways to locate current IP across environments |
| Factory reset impact | Resets admin password and IP settings | Reconfig required after reset |
Your Questions Answered
What is the default management IP for the Cisco SG200?
The SG200’s default management IP is commonly 192.168.1.254 on a private LAN. If that address doesn’t respond, the device might be on DHCP or require a factory reset. Check the label and Cisco docs for confirmation.
The SG200 usually uses 192.168.1.254 as its default IP; if you don’t reach it, try discovery methods or reset to factory defaults.
How do I reset the SG200 to factory defaults?
To reset, press and hold the MODE button for 6–8 seconds until the LEDs indicate reset. This restores the device to its default IP and credentials, after which you can reconfigure from scratch.
Hold the MODE button for several seconds until you see the indicators reset, then set up again.
What if the SG200 is on DHCP and I can’t find its IP?
Use a network scanner, check the DHCP server lease list, examine the device label, or connect via console to view the current IP configuration. If necessary, perform a factory reset to regain control.
Scan the network or check the DHCP server to locate the SG200’s IP, or reset to defaults if you’re stuck.
Does resetting affect my configurations?
Yes. A factory reset erases custom settings, VLANs, and passwords. Back up configurations where possible, then reconfigure the device after the reset.
Yes, a factory reset wipes your settings, so back up first and reconfigure afterward.
How can I secure SG200 management access?
Place the management interface on a dedicated VLAN, enable SSH, disable unneeded remote access, use strong admin credentials, and enable logging for audit trails.
Put management on a separate VLAN, use SSH, and lock down access with strong credentials.
“Access control starts with knowing the device's default IP and having a reliable recovery path. Without it, admins risk extended downtime and lost configuration access.”
Key Takeaways
- Know the default IP and how to verify it
- Use factory reset only when necessary
- Document network settings for future access
- Change default credentials and secure management paths
- Prefer a dedicated management VLAN and ACLs
- Regularly backup configurations and test recovery