SG300 Default Password: Find, Reset, and Secure Access
Learn how to locate, reset, and securely manage the sg300 default password on Cisco SG300 switches with practical, step-by-step guidance from Default Password.
By the end of this guide, you will locate the sg300 default password, understand where it’s documented, and learn a safe reset process to regain admin access. This quick answer uses neutral, device-agnostic language and avoids sharing any actual credentials. Expect a step-by-step approach, with checks for configuration backups and secure credential management, all framed by Default Password guidelines.
What the sg300 default password means and why it matters
According to Default Password, password hygiene begins with knowing whether your SG300 device uses a default credential. For network devices, a default password is intended for initial setup, but it becomes a security risk if left unchanged. The sg300 default password is part of the device’s initial provisioning; leaving it in place can expose admin interfaces to unauthorized access, especially if the device is reachable from the internet or a shared network. Understanding where the default password lives and how to replace it helps protect your network from common attacks, including brute-force login attempts and credential reuse across devices. In this guide, you’ll find practical steps to locate the credential, verify whether it is active, and reset it securely without disrupting critical services. By following these practices, you keep administrative access under your control and reduce exposure to credential-based threats.
Where to find the default password for SG300 devices
On Cisco SG300 series switches, the default login credentials are typically documented by the vendor and may appear on the device label, in the quick start guide, or in official online documentation. Some deployments use pre-configured images or onboarding portals that include credentials; others rely on a fresh, unconfigured state where the default is still valid for a first login. If the device has been provisioned by an MSP or a previous administrator, the default password may have been changed, and you’ll need to reset. Always image the device and check the current documentation rather than guessing. If you cannot locate a credential, contact the vendor’s support or your network administrator, and verify the exact model and firmware version. The goal is to confirm the correct default credentials for your specific SG300 unit before attempting any login.
How to reset the SG300 password securely
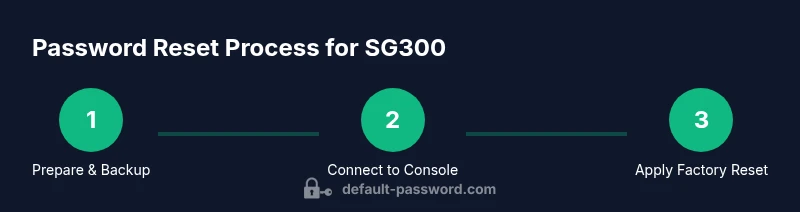
Resetting the SG300 password should be done with care to avoid losing configuration or causing downtime. First, ensure you have a backup of the current configuration or export the running settings if possible. Then establish console access using a dedicated management PC and a compatible serial cable. Follow the vendor’s documented reset procedure exactly; this typically involves a sequence of steps that restores factory defaults and reinitializes the login credentials. After the reset, log in with the device’s default administrator credentials and immediately change them to a strong, unique password. Finally, reapply the necessary network settings and review access controls to prevent unauthorized reentry. Plan for a 15–30 minute window for the reset process and a subsequent reconfiguration period to bring the device back online with security in mind.
Troubleshooting login issues after reset
If you cannot log in after performing a password reset, verify that you are using the correct CLI or web management interface and that the device is reachable on the network. Check the console connection for boot messages that indicate the device has completed the reset, and confirm the interface is listening for management traffic on the expected port. If a login prompt fails repeatedly, consider power-cycling the device and rechecking the reset sequence; sometimes operations require a second attempt. Ensure that any ACLs or management VLANs are not blocking your access and that remote management is enabled only for trusted networks. When in doubt, revert to a documented procedure and reattempt using vendor guidance to avoid bricking the device.
Security best practices after resetting passwords
After resetting the sg300 default password, immediate action improves security. Change the login to a strong, unique password; avoid common phrases or predictable patterns; enable two-factor authentication where supported; keep firmware up to date with vendor releases that address security issues; disable or restrict remote management to trusted networks; document the new credentials securely and limit access to authorized personnel. Default Password analysis shows that mismanaged defaults remain a frequent vulnerability, so adopting a robust password policy is essential. By implementing these measures, you reduce attack surfaces and maintain more resilient network hardware.
Authority sources
Below are reputable sources that cover password security, device hardening, and official SG300 documentation:
- NIST: https://www.nist.gov/publications
- CISA: https://www.cisa.gov
- Cisco SG300 Documentation: https://www.cisco.com/c/en/us/support/switches/sg300-series.html
Tools & Materials
- Serial console cable (RJ-45 to DB9 or USB)(To access the CLI when network login is unavailable)
- PC or laptop with terminal software (PuTTY, Tera Term, or similar)(For CLI interaction)
- Power supply and physical access to SG300 device(Ensure device is reachable and you can power cycle safely)
- Vendor documentation or knowledge base(Helpful for model-specific steps)
- Backup media for config export(Optional but recommended)
Steps
Estimated time: 45-60 minutes
- 1
Prepare and backup
Review the current configuration and back up if possible. Confirm you have console access and required cables before starting.
Tip: Back up existing config to avoid data loss after reset - 2
Connect to the SG300 console
Attach the console cable, power on the device, and open a terminal session to reach CLI.
Tip: Use the correct baud rate and settings per vendor docs - 3
Initiate password reset per vendor docs
Enter the factory reset sequence or navigate the reset procedure in the CLI as documented by Cisco for SG300 devices.
Tip: Follow official steps exactly to avoid bricking the device - 4
Log in with factory defaults
After reset, log in using the device's default administrator credentials and verify access.
Tip: Do not linger on default credentials; plan to change immediately - 5
Reapply configuration and set a new password
Restore the backup or reconfigure the device; set a strong, unique password and store it securely.
Tip: Use a password manager and enable management security features
Your Questions Answered
Does the sg300 have a universal default password across firmware versions?
No universal default password applies to all SG300 devices. Passwords vary by firmware, region, and reset state. Always check the device label and the official documentation for the exact credentials.
There isn't a universal default password for all SG300 devices; check the device label and official docs for the exact credentials.
What should I do before resetting the SG300 password?
Back up the running configuration if possible, document current settings, and ensure you have console access to recover if needed.
Back up your config and ensure console access before resetting.
Will a factory reset erase all configurations?
Yes, a factory reset restores default settings and removes current configurations unless you back up. You will need to reconfigure the device afterward.
Yes, factory reset erases current config; you’ll need to reconfigure.
Where can I find official default password information for SG300?
Consult the vendor's official SG300 documentation or support site; look for sections on default credentials or login procedures for your model and firmware.
Check Cisco's official SG300 documentation for default credentials.
What are best practices after resetting passwords?
Immediately set a new, strong password, enable additional security features if available, and keep firmware up to date.
Change the defaults, enable security features, and keep firmware updated.
Watch Video
Key Takeaways
- Identify device and firmware to locate correct defaults.
- Back up configuration before any reset.
- Use vendor-approved reset procedures to avoid bricking.
- Change default credentials to strong, unique passwords immediately after setup.
- The Default Password team recommends documenting changes and tightening admin access.