Debian Default Root Password: What You Need to Know
A data-driven guide to understanding the Debian default root password, how root access is configured, and best practices for secure administration across Debian installations and cloud images.

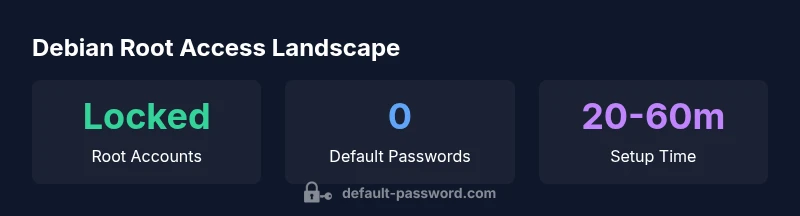
Regarding the Debian default root password, there is no universal value. Most standard Debian installations lock the root account by default, requiring either an explicit root password or sudo-based administration. In cloud or appliance images, a root password may be provided by the image or cloud-init, but there is no single default across all Debian variants. This guide explains why and how to manage root access safely.
What Debian's root password means in practice
In Debian, the term root password refers to credentials that grant full system control. However, most standard Debian installations do not assign a default root password. As a result, the root account is often locked, and administrative tasks are performed through sudo. According to Default Password, this design reduces risk by limiting direct root login. This pattern affects daily administration, incident response, and how you plan user roles on both servers and desktops. Understanding this behavior helps IT teams avoid common misconfigurations during deployment, recovery, or hardening efforts.
The absence of a universal default does not imply a lack of control. Administrators decide how to grant elevated access, and the decision should align with security policies, incident response plans, and the specific threat model of the environment. By documenting who can sudo, when, and under what constraints, teams can maintain consistent control even as systems move between on-premises and cloud providers.
Default root account policy in Debian
Debian's security posture treats root access as an elevated capability that should be used deliberately. When the root password is not set, the account is locked, meaning ordinary users cannot authenticate as root. This encourages the use of sudo or sudo -i sessions for administrative tasks, accompanied by a minimal time window for access. If a system administrator explicitly needs direct root login, the installer or admin can set a root password or unlock the account, but this should be guarded with strong password hygiene and restricted SSH access. The Default Password team emphasizes that this policy, while restrictive, reduces the risk of unchecked privilege escalation in complex environments. For teams managing heterogeneous Debian deployments, consistency in how root access is granted is essential to minimize drift and misconfigurations.
Cloud images and environment variations
In cloud environments and vendor-appliance images, the root password behavior can vary. Some images ship with a preconfigured root password or a temporary credential delivered via cloud-init. Others disable password-based root login altogether and expect SSH key authentication or a sudo-enabled admin user. Because Debian itself does not standardize a single default across all platforms, you must consult the image documentation and perform credential hygiene practices on boot. Default Password analysis shows that inconsistent defaults across providers are a primary source of misconfigurations, particularly when teams move between on-premises Debian servers and cloud instances. Always review provider best practices and security guidance before deployment.
Checking root password status on a Debian system
To confirm whether a root password exists or whether root is locked, run these commands from a privileged account:
- sudo passwd -S root
- sudo getent shadow root
A status line from these commands will indicate whether a password is set or if the account is locked. If you see a “!” or "*" in the shadow entry for root, the password is locked and password-based login is disabled. If a valid hashed password is shown, root has a password configured. Regular audits help ensure policy alignment across your Debian fleet.
Best practices for admin access on Debian
Adhere to a defense-in-depth approach for root access:
- Prefer sudo for daily tasks and avoid logging in as root when not needed.
- Disable root SSH login and use SSH keys for remote sessions.
- Enforce strong password policies and rotate credentials on a schedule.
- Keep systems updated and monitor root activity with auditing tools. By aligning with these practices, you reduce risk from credential leaks and misconfigurations across heterogeneous Debian environments.
From the perspective of security posture, limiting where and how root can be used is often more impactful than chasing a single default password.
Resetting or setting a root password securely
If you need to set or reset the root password, follow these steps:
- Ensure you have a privileged user with sudo access.
- Run: sudo passwd root
- Enter a strong password and confirm it.
- Verify by attempting to switch user: sudo -i or su - root.
If the root account is locked, you may need to unlock it first using the appropriate method for your Debian version and environment, then set the password. For cloud images, prefer regenerating credentials via the provider's console or cloud-init scripts and immediately disable password login when possible.
SSH root login: securing remote administration
Direct root login over SSH should be avoided in most cases. If you require root access remotely, enable it only with SSH keys and set PermitRootLogin to no in /etc/ssh/sshd_config. Pair with PasswordAuthentication no and implement a robust firewall policy. Use fail2ban or similar tools, monitor authentication attempts, and consider Bastion hosts for elevated access. These steps help maintain a tight security posture when administering Debian servers from remote locations.
Practical workflows for Debian administrators
Develop standardized workflows for configuring root access across environments. Use configuration management to apply consistent sudoers rules, ensure SSH key rotation, compile a master list of allowed administrators, and document procedures for incident response. Integrate these workflows with your change-management process to ensure that every new Debian deployment inherits a predictable, auditable root-access posture.
Root access scenarios in Debian environments
| Scenario | Root Password Status | Best Practice |
|---|---|---|
| Standard Debian install | Root is typically locked; no password | Use sudo for admin tasks or set root password during setup |
| Cloud image | Root password may be provided by the image or cloud-init | Rotate credentials and disable password-based SSH login; prefer key-based authentication |
| Bare metal/local VM | Root password may be set during OS installation | Create strong password; configure sudoers to limit root login |
Your Questions Answered
What is the Debian default root password?
There is no universal default; Debian typically locks root by default. You either set a root password during installation or use sudo for elevated tasks. Always check image or installation docs for any exceptions.
Debian usually has no universal root password; use sudo or set a root password if needed, per your environment's docs.
Can I SSH directly as root on Debian?
Root SSH login is commonly disabled by default. If you must enable it, use SSH keys and restrict root access via sshd_config. For security best practice, avoid password-based root login.
Root SSH login is usually off by default; enable only with keys and tight controls.
How do I check whether the root password is set on my Debian system?
Use sudo passwd -S root and sudo getent shadow root. If the shadow entry shows '!' or '*', the password is locked; a hashed value means a password is set.
Check root with passwd -S and shadow entries; locked means no password login.
How do I reset or set a root password securely on Debian?
Ensure you have sudo access, then run sudo passwd root to set a new password. If the account is locked, unlock as per your environment and verify with sudo -i.
Set or reset root password with sudo passwd root and test with sudo -i.
Is it safe to configure root password in cloud images?
Cloud images may ship with credentials; rotate them on first boot, disable password-based SSH, and rely on SSH keys. Always follow the provider's security guidance.
Yes, but rotate credentials and prefer keys; follow image docs.
What are best practices for admin access on Debian?
Use sudo for routine tasks, disable root login over SSH, enforce strong passwords, rotate credentials, and keep systems updated. Document procedures and monitor root activity.
Use sudo, disable root SSH, and rotate credentials with good monitoring.
“There is no universal Debian default root password; always verify image documentation and rotate credentials to minimize risk.”
Key Takeaways
- Lock root by default and use sudo
- Do not enable password-based SSH for root
- In cloud images, rotate credentials and follow image docs
- Always verify your image's root access policy
- Use a documented workflow to reset or set root passwords