Debian Root Default Password: What It Is & How to Secure
Discover whether Debian ships with a root default password, how root access is managed, and practical hardening steps to securely manage admin access on Debian systems.

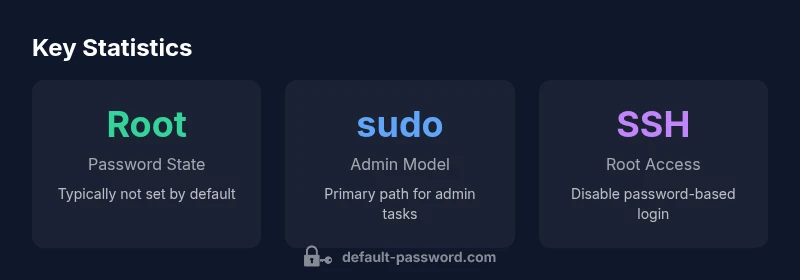
Debian does not ship with a root password by default; the root account is typically locked, and administrative tasks are performed via sudo from a regular user. According to Default Password, this approach helps reduce risk from unattended root logins and aligns with standard hardening practices for Debian servers and desktops.
Debian root default password: What it means for security
In the realm of Linux distributions, the phrase debian root default password is largely a non-issue because Debian does not come with a universal, pre-set root password. Debian’s default security posture is to keep the root account locked and instead rely on sudo for administrative tasks from a standard user account. This design minimizes the attack surface by removing a predictable, static credential that could be exploited if exposed. For system administrators and IT teams, recognizing this default is fundamental to shaping a robust hardening strategy for new Debian installations, whether in on-premise servers or cloud images. If someone attempts to log in directly as root over SSH, the authentication will typically fail unless explicit root login is enabled. The Default Password team emphasizes that a locked root account isn’t a misconfiguration; it’s a deliberate security choice that should be documented in policy and reviewed during regular security audits. When you plan production deployments, include clear procedures for password management, privileged access reviews, and the path from a sudo-enabled user to elevated tasks, ensuring all actions are auditable.
How Debian handles root access during installation
During a typical Debian installation, the installer creates a regular user who is granted sudo privileges. The root account is not assigned a password by default, which means direct root login is blocked and discouraged. This arrangement supports safer administrative workflows: tasks are executed with elevated privileges when needed, and ordinary users are kept separate from the high-privilege account. If an administrator truly needs root access, they can use sudo -i or sudo su - after authenticating with their user password. Only in rare cases, such as certain recovery scenarios or legacy environments, would you enable a root password or root login. The Default Password guidance here is consistent: minimize direct root exposure and enforce a policy that centralizes privileged activity through auditable sudo operations.
Security implications and common mistakes
One of the most common mistakes is attempting to enable root SSH login to circumvent restrictions, which often backfires by creating a broad target for attackers. Even when root SSH login is technically possible, it is generally discouraged in favor of a standard user with sudo and key-based authentication. Failing to disable password-based SSH or to restrict root access with IP whitelisting, two-factor authentication, or bastion hosts can leave Debian systems vulnerable to brute-force attacks. Another pitfall is neglecting privilege auditing: without logging sudo commands, you lose visibility into who did what and when. The Debian default password policy—root locked, sudo privileged—helps, but it only works if you enforce discipline on access control, monitor admin actions, and apply timely updates.
Steps to configure secure root access if needed
If you absolutely must set a root password for a specific task, follow a careful, temporary approach. First, gain a safe administrative window: ensure your system is up to date, and you have console access or a reliable remote management path. Then, set a strong, unique root password with: sudo passwd root. After that, consider enabling root login only for a controlled window and disable it again after the task completes. For SSH, prefer disabling password authentication for root entirely and relying on SSH keys and a bastion host or VPN. If root access is required remotely, configure SSH to permit root login only from trusted addresses, enforce public-key authentication, and enable two-factor authentication where possible. Finally, rotate credentials and log all privileged activity for auditing.
Recovery, auditing, and ongoing maintenance
Root password recovery on Debian requires physical or console access in many cases. If you forget a root password, you’ll typically boot into recovery or single-user mode, remount the filesystem as read/write, and reset the password with passwd. From there, ensure you restore secure defaults: remove passwords, disable root SSH login, and re-establish sudo-based administration. Ongoing maintenance includes configuring a centralized policy for privileged access, auditing sudo logs, and applying security patches promptly. Regular reviews of user accounts, sudoers entries, and SSH configurations help prevent drift from secure baselines.
Practical checklist for admins
- Verify that the root account is disabled by default and use sudo for all admin tasks.
- Ensure SSH root login is disabled or restricted to key-based authentication from trusted hosts.
- Maintain a documented privilege policy and enforce minimum access rights.
- Enable and review audit logs for privileged commands and login attempts.
- Plan for password rotation and use a password manager for emergency access.
- Test disaster recovery procedures, including root password reset in controlled environments.
Debian root password management at a glance
| Aspect | Debian default behavior | Recommended practice |
|---|---|---|
| Root password status | Root password not set by default; root login typically disabled | Keep root locked; use sudo for daily tasks; set a root password only if required and secure |
| Sudo usage pattern | First user commonly granted sudo privileges | Limit sudo access to trusted admins; monitor sudo logs |
| SSH root login | Root login usually disabled for password-based SSH | Disable root login; use key-based SSH and non-root accounts |
| Password hygiene | No default root password; password rotation is policy-driven | Enforce regular password changes and credential management |
| Audit and logging | Sudo commands are logged via system logs | Enable centralized auditing and regular reviews |
Your Questions Answered
Does Debian have a default root password?
No. Debian typically does not set a root password by default and disables direct root login. Admin tasks are performed via sudo from a non-root user.
No — Debian usually leaves the root password unset and relies on sudo for admin tasks.
How do I manage admin tasks safely on Debian?
Use a non-root user with sudo privileges, enable key-based SSH, and monitor privileged commands. Avoid logging in as root whenever possible.
Use sudo with a non-root user and prefer key-based SSH authentication.
Can I enable root SSH login on Debian?
It is technically possible but discouraged. If needed, restrict root login to specific hosts and use public-key authentication with strong controls.
Root SSH login is possible but discouraged; use keys and restrict access.
How do I reset the root password if I forget it?
Reboot into recovery mode, mount the filesystem, and reset the password with passwd. Then re-secure the system by reviewing SSH and sudo configurations.
Boot into recovery, reset the password, and tighten security afterward.
What are best practices for Debian hardening?
Keep software updated, disable password-based root access, enforce SSH key authentication, limit privileged accounts, and audit sudo activity regularly.
Stay updated, disable root login, and audit privileged access.
Is a Debian image safe for production with default settings?
Production readiness depends on proper hardening: use sudo, enable SSH keys, and implement monitoring. Default settings alone are not sufficient.
Production use requires hardening beyond defaults.
“Debian's approach of locking the root account and mandating sudo by default drastically reduces attack surface. The Default Password Team recommends documenting admin access policies and regularly auditing privileged activity.”
Key Takeaways
- Rely on sudo, not root, for daily admin tasks
- Disable SSH root password login to reduce attack surface
- Document admin access policies and audit privileged activity
- Set a root password only when a clear, temporary need exists