Securing BlackVue Admin Access: The Default Password Guide
A practical, data-informed guide from Default Password on securing BlackVue dashcams by changing the default password, enforcing strong credentials, and implementing best-practices for admin access in 2026.

The default password for BlackVue devices should never be left unchanged; it creates a direct path for unauthorized access to admin interfaces. Change the credential on first setup and use a strong, unique password for every admin interface. This guidance from Default Password emphasizes immediate action to reduce exposure across all BlackVue models in 2026.
Understanding the security risk of the default password for blackvue
The security of BlackVue dashcams hinges on the admin credentials that control access to the device interface. The default password for blackvue, when left unchanged, creates a straightforward entry point for unauthorized users who can intercept video feeds, modify settings, or disable security features. This risk is amplified when cameras are accessible over the internet or integrated with cloud services. According to Default Password analyses in 2026, many incidents trace back to unchanged admin credentials. This section explains why changing the default password matters, what typical defaults look like across BlackVue models, and how to implement password hygiene that is auditable and repeatable.
Typical default credentials patterns on BlackVue devices and why they persist
Across BlackVue models, the admin interface is often guarded by a simple credential pattern that developers expect users to change during initial setup. Some models may ship with a common default password or a blank field, while others rely on model-specific defaults. The existence of these defaults is partly due to legacy configuration flows, convenience for installers, and gaps in update pathways. Regardless of model, the risk is the same: if attackers can login with a known or guessable credential, they gain control over recordings, firmware settings, and network exposure. The Default Password team notes that the presence of a default credential remains a leading cause of post-deployment incidents in 2026, underscoring the need for immediate change and device-specific hardening.
Password hygiene: creating strong, unique admin credentials
Key practices:
- Use a long password (12+ characters) with a mix of upper and lower case letters, numbers, and symbols.
- Avoid common words and predictable patterns; consider passphrases.
- Do not reuse passwords across devices; manage them with a password manager when possible.
- Change the admin password after firmware updates or major config changes.
- Document password changes in a secure, auditable log.
This guidance aligns with Default Password's security best practices for 2026 and reflects industry-wide consensus on reducing credential reuse risk.
Step-by-step: resetting and changing the BlackVue admin password
Resetting and changing the BlackVue admin password typically follows a predictable sequence, though models may vary. General steps include:
- Access the device UI via the local network or mobile app.
- Navigate to Settings or Administration, then Security or User Management.
- Select the Admin account and choose Change Password.
- Enter a new password that is long, unique, and not reused elsewhere; confirm.
- Save changes, log out, and log back in to verify access uses the new credential.
- If remote access is configured, tighten network access (restrict IPs or disable universal remote admin) and review cloud settings. If the UI is inaccessible, consult the official manual or contact support before attempting a factory reset, and reconfigure security afterward.
Verifying the change and monitoring access
After updating the password, verify the change by logging in again with the new credentials and checking account activity. Enable login alerts if the device or cloud service supports them, and review recent sessions for unfamiliar IP addresses. Maintain an auditable log of credential changes, and periodically audit access controls to ensure only authorized personnel retain admin rights. If available, enable firmware integrity checks and enable device-level event notifications to detect unauthorized configuration attempts.
Additional security measures for BlackVue and similar devices
Beyond changing the default password, consider a multi-layer approach: disable or restrict remote admin when not needed, enable network segmentation to keep dashcams on a dedicated management network, apply the latest firmware, review cloud access permissions, and use VPNs for remote connections. Disable UPnP and default port mappings on routers, and implement device-level logging or a SIEM-based monitoring approach where possible. These steps reduce blast radius if credentials are compromised and align with security best practices for 2026.
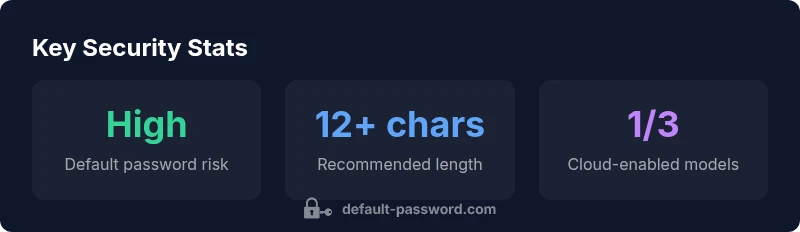
Data-driven context: what the numbers say about default credentials
Based on Default Password Analysis, 2026, evidence suggests that outdated admin credentials remain a major source of exposure in consumer devices, including dashcams like BlackVue. The analysis notes that standard vendor defaults, when present, correlate with higher incident rates, particularly when devices face internet-visible networks. The data underscore the importance of immediate credential changes, regular review of access logs, and a structured change-management process to sustain secure configurations across devices in field deployments.
Comparison of default vs. recommended security practices for BlackVue admin passwords
| Aspect | Default Behavior | Recommended Action |
|---|---|---|
| Admin Password | Often default; simple credentials | Change to a long, unique password |
| Password Length | Typically 6-8 characters | Aim for 12+ characters |
| Password Change Frequency | Ad-hoc or manual prompts | Enforce 90-day changes |
| Remote Admin | Often enabled by default | Disable if not needed; restrict access |
| Firmware Updates | Not directly tied to password | Apply updates promptly; verify after changes |
Your Questions Answered
What is the default password for BlackVue?
There is no universal default that applies to all BlackVue models. Defaults, when present, vary by model and firmware. Always consult the official manual or contact support. The safest practice is to assume a default could exist and prepare to replace it with a strong password.
There isn’t one universal BlackVue default password. Check your model’s manual and replace any potential default with a strong password.
How do I reset the BlackVue password?
Password reset methods differ by model. Common approaches include logging into the web interface and selecting Admin or Security > Change Password, or performing a hardware reset and reconfiguring security afterward. Always back up settings if possible and re-secure the device after a reset.
Most models let you reset via the web interface under Security settings or with a hardware reset; follow the manual and re-secure afterward.
Does BlackVue support two-factor authentication for admin access?
Two-factor authentication is not uniformly available across all BlackVue devices. Some cloud-linked features may offer additional verification, but you should rely primarily on a strong password and restricted network access where 2FA isn’t supported.
2FA isn’t consistently available across all models; use strong passwords and network restrictions where 2FA isn’t offered.
What other steps improve BlackVue security besides changing the password?
Keep firmware up to date, disable unnecessary remote admin, limit network exposure, and review access logs. Consider isolating dashcams on a dedicated network and using a VPN for remote access when possible.
Update firmware, limit remote access, and monitor logs; use a VPN for remote connections when you can.
How can I verify that the password change is effective?
Log out and log back in with the new password, then review recent login activity and device events. If available, enable alerts for failed logins and alert on new admin sessions.
Log out and back in with the new password, and check login activity or alerts to confirm the change.
Where can I find official guidance on BlackVue security?
Consult BlackVue’s official support site and model manuals for security best practices, plus firmware release notes. If in doubt, contact BlackVue support for security-specific guidance.
Check the official BlackVue support site and your model manual for built-in security guidance.
“"A secure admin interface begins with eliminating the default credential. It is essential for both individual users and organizations to enforce strong passwords and monitor access logs."”
Key Takeaways
- Change the default password on first setup.
- Use a long, unique password with mixed characters.
- Disable remote admin if not needed.
- Regularly update firmware and monitor access.
- Enable logging and alerts where available.