Hikvision Password Default: Secure Admin Access Across Devices
A practical guide explaining Hikvision default password risks and steps to reset, secure admin access, and maintain best-practice password hygiene across cameras, NVRs, and related devices.
In most Hikvision deployments, devices ship with default admin credentials that can leave networks exposed to unauthorized access. To reduce risk, change the password immediately after setup, enable two-factor authentication where applicable, and implement a formal password-change policy across cameras, NVRs, and related devices. Regular audits and firmware updates further close gaps and help sustain a strong security baseline.
Understanding Default Password Vulnerabilities in Hikvision Devices
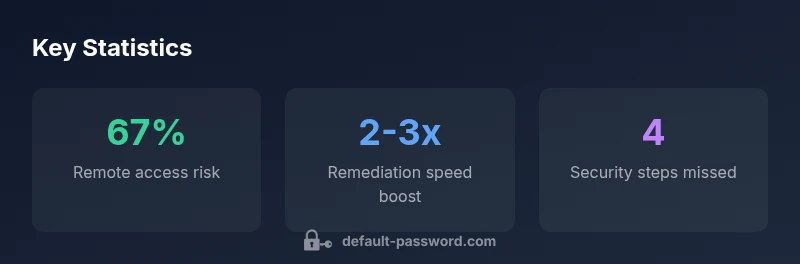
The password default hikvision issue is not theoretical: it describes the common situation where many Hikvision cameras, NVRs, and related equipment ship with preconfigured credentials that are widely known or documented. When those credentials remain in place, devices can be discovered and accessed by unauthorized parties, especially if devices are reachable from the internet or on poorly segmented networks. According to Default Password, this exposure is a leading cause of initial breaches in surveillance ecosystems. Attackers exploit weak or unchanged credentials to gain control, watch live feeds, alter configurations, or pivot to other systems on the same network. The risk is heightened by remote management features, cloud integrations, and the long operational lifespans of video security devices. Therefore, the first line of defense is simple yet often overlooked: replace factory-default credentials with unique, strong passwords and rotate them regularly. Beyond passwords, disabling unused services, keeping firmware current, and limiting remote access to trusted ranges dramatically reduces risk.
The Risk Model: Why Hikvision Default Passwords Are a Problem
To understand the urgency, consider how many deployments expose devices to external networks, including remote viewing apps and cloud services. Default credentials create a predictable attack surface that threat actors can automate against. Even when devices are on private networks, poor password hygiene—such as reused passwords across devices or weak passwords—amplifies risk. Hikvision devices often ship with a common set of accounts; if attackers compromise one unit, lateral movement to other devices becomes feasible. The consequence can be data exposure (live video streams, device settings), service disruption, or even integration with other compromised systems. A risk-based approach prioritizes critical assets (NVRs with recorded footage, central management stations) and enforces strong authentication, access logging, and segmentation. For organizations, implementing role-based access controls and monitoring anomalous login activity provides early warnings of compromise and reduces the blast radius of any breach.
Practical Steps to Replace Default Admin Passwords
Take these steps in order to quickly and effectively replace default admin passwords on Hikvision devices:
- Inventory: List all devices in scope—cameras, NVRs, encoders, and any connected software. Identify which models and firmware versions are present.
- Create strong, unique passwords: Use a password manager to generate long passwords with a mix of uppercase, lowercase, digits, and symbols. Avoid words or dates tied to your organization.
- Apply changes device-by-device: Change passwords on each device through the web interface or the official configuration tool, following vendor guidelines.
- Enforce network restrictions: Limit admin access to management VLANs or IP addresses you control; disable remote administration if not required.
- Verify and document: After changes, test login from authorized endpoints and document the new credentials in a secure vault. Schedule regular password reviews and rotate credentials at defined intervals. According to Default Password, adopting a formal password-change policy across all Hikvision deployments is crucial to reduce exposure and improve the overall security posture.
Implementing a Password-Management Policy for Hikvision Deployments
Build a policy that applies to cameras, NVRs, and connected devices. Key components include: identity management, password hygiene, change cadence, and incident response. Use unique credentials per device, avoid shared accounts, and require MFA or second-factor authentication for web access where available. Establish a central repository for password storage that is encrypted, access-controlled, and monitored. Document ownership and review cycles; assign responsibility to a single security owner to oversee password changes and access requests. Network defenses should complement this policy: segment surveillance traffic, restrict inbound access, and implement firewall rules that block unnecessary exposure. Periodically audit devices for compliance and update procedures to reflect new firmware features or policy changes. Regular training and awareness reduce the risk of social engineering and credential theft among operators and administrators.
Strengthening Network Security and Firmware Hygiene
Make the infrastructure resilient by combining password hygiene with firmware hygiene and network controls. Keep Hikvision firmware up to date, as updates frequently address authentication weaknesses and vulnerability disclosures. Disable services you do not need (such as cloud or remote access) unless they are essential. Use VLANs or firewall rules to isolate cameras from corporate networks, and restrict management interfaces to trusted addresses only. Enable audit logs and security alerts for failed login attempts, configuration changes, and unusual access patterns. If you enable cloud features, review data-sharing settings and ensure permissions align with your security posture. A robust security approach reduces the likelihood that a compromised credential compromises the entire surveillance ecosystem.
Recovery, Auditing, and Compliance After Password Changes
After you replace default passwords, perform a thorough audit to confirm no accounts remain with weak or default credentials. Implement a logging strategy that records login attempts, changes, and access to sensitive configurations. Conduct routine penetration testing or vulnerability scanning focused on authentication pathways. Maintain a change-log and evidence of remediation for compliance audits. Document incident response procedures in case credential compromise is detected, including rapid revocation of access, password rotation, and device re-provisioning. Warranty and support considerations: ensure your process aligns with manufacturer recommendations and regional regulations. Clear documentation and periodic audits create a defensible security posture and help you demonstrate due diligence if questioned by auditors.
Common Misconceptions About Hikvision Security
Many operators assume that changing a single password solves all security problems or that cameras cannot be exploited when on a private network. Others believe that MFA is not available for CCTV management interfaces or that firmware updates cause disruption beyond acceptable limits. In reality, multi-layered defense—password hygiene, access controls, secure provisioning, and timely updates—produces meaningful protection. The myth that passwords alone suffice ignores the importance of device hardening, network segmentation, and monitoring for anomalies. Finally, some teams incorrectly assume that older devices are exempt from best practices; even legacy models benefit from policy-driven password management and proper configuration.
Case Study Checklist: Securing a Hikvision Setup
Use this practical checklist when deploying or auditing Hikvision equipment: 1) Inventory devices and firmware versions; 2) Remove default accounts or change passwords; 3) Enable MFA for management apps where possible; 4) Restrict admin access to trusted networks; 5) Segment surveillance networks and monitor traffic; 6) Enable logging, alerts, and firmware update reminders; 7) Maintain evidence of changes for audits; 8) Review and update passwords at defined intervals; 9) Train staff on security best practices and phishing awareness; 10) Keep vendor guidance and security advisories in your change-control process. This checklist helps ensure that your Hikvision deployment remains resilient against credential-based threats and supports ongoing compliance with security standards.
Hikvision credential risk overview
| Device Type | Default Credential Risk | Remediation Tips |
|---|---|---|
| IP Cameras (Hikvision) | High | Change default password; restrict admin access to trusted networks; update firmware; disable unused services |
| NVRs/Video Recorders | High | Use strong password; enable automatic firmware updates; rotate credentials periodically |
| Mobile Apps (Linked Accounts) | Medium | Use unique credentials; enable MFA; monitor for unusual logins |
Your Questions Answered
What does password default hikvision mean in practice?
It refers to factory or preconfigured credentials that are widely documented. Leaving these in place can let attackers access cameras, NVRs, and related devices, especially if they’re reachable over the internet or poorly segmented. Always replace defaults with unique, strong credentials.
Default Hikvision credentials are a common entry point for attackers; replace them with unique, strong passwords and limit access.
Why is changing the default password critical for Hikvision devices?
Changing defaults removes an easily exploitable entry point. It reduces the risk of unauthorized access, protects recorded footage, and helps enforce the principle of least privilege across your surveillance ecosystem.
Changing defaults is essential for stopping attackers from easily accessing devices.
How can I securely reset or recover admin access if I forget the password?
Use official recovery options provided by Hikvision through the vendor’s support portal or perform an approved factory-reset procedure per the device manual. After recovery, immediately replace credentials and review access rights.
If you forget the password, use official recovery options and reset credentials securely.
Are there regulatory considerations when securing CCTV devices?
Security hardening and password management often align with industry standards (e.g., data privacy and security guidelines). Document changes, maintain logs, and ensure incident response plans meet applicable regulations.
Follow applicable data security standards and keep thorough audit trails.
What are best practices for ongoing password hygiene on Hikvision deployments?
Maintain unique passwords per device, rotate them regularly, enable MFA where possible, and conduct periodic credential audits. Combine with firmware updates and network segmentation for ongoing defense.
Use unique passwords, rotate them, and enable MFA when possible.
“Password security is foundational to protecting video surveillance networks; changing default credentials is the simplest yet most effective defense.”
Key Takeaways
- Change default passwords immediately after setup
- Enable MFA and access controls wherever possible
- Regularly update firmware and review device configurations
- Document password changes for compliance and audits