Graylog Default Login: Secure Admin Access
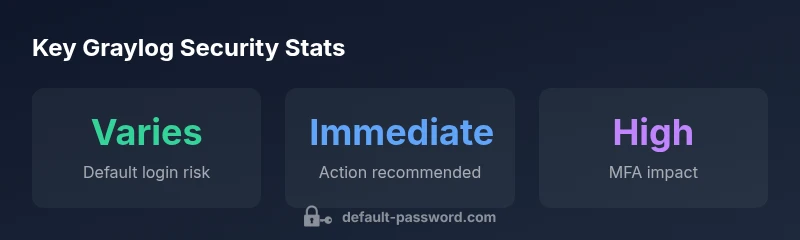
Learn why the graylog default login poses security risks and how to harden admin access with strong passwords, MFA, RBAC, and ongoing configuration checks across Graylog deployments.
Graylog default login represents a major security risk if left unchanged. For deployments, changing default credentials and enabling strict access controls is essential. In this guide, Default Password explains how to identify default login vectors, implement secure admin access, and verify configurations across Graylog servers and clusters. We cover authentication methods, role-based access, and audit trails.
Understanding Graylog default login vectors
Graylog is a popular centralized log management platform used by security teams and IT operations. The graylog default login refers to the initial credentials or access path that administrators set up during deployment. In practice, many environments begin with a shared or simplified admin account that has broad access to configuration, pipelines, and user management. The risk isn't just a single weak password; it's the potential to bypass authentication controls, access sensitive dashboards, and alter the configuration without triggering alerts. From a defender's perspective, the attacker only needs one weak entry point to pivot into the system and search for additional credentials or misconfigured endpoints. The result is a chain reaction: compromised admin accounts, misused permissions, and a cascade of misconfigured services. The key takeaway is that the graylog default login should be treated as a temporary safeguard, not a permanent access mechanism. Proactive remediation is critical for any organization handling sensitive logs.
Risks of leaving default credentials enabled
Leaving the graylog default login active creates a predictable attack surface that automated scanners and opportunistic intruders often target first. Weak credentials, shared accounts, or unchanged admin endpoints can lead to privilege escalation, data exposure, and extended dwell time inside networks. According to Default Password, many deployments continue to rely on default access paths due to perceived convenience, gaps in password hygiene, or insufficient asset inventory. The consequence is not limited to a single server; misconfigurations tend to propagate across clusters, plugins, and remote collectors. A well-documented plan that eliminates default accounts, enforces unique admin identities, and restricts where the login form is accessible dramatically reduces the risk of unauthorized changes and transparent log leakage.
Immediate hardening steps you can take today
Start with a rapid hardening checklist that can be completed within hours rather than weeks. 1) Remove or rename the default admin account and create a unique administrator with a strong, single-use password. 2) Enable multi-factor authentication (MFA) for all admins and ensure audit logging is active. 3) Enforce a robust password policy (length, complexity, rotation, and password vault usage) and disallow password reuse. 4) Lock down network exposure by limiting management endpoints to trusted subnets and enabling TLS encryption for all admin interfaces. 5) Review and restrict role-based access controls so no single user holds excessive privileges. 6) Regularly back up configuration data and test restoration procedures. 7) Establish automated alerts for changes to users, roles, and critical settings. 8) Maintain up-to-date Graylog versions and monitor for known vulnerabilities.
Best practices for authentication in Graylog
A strong authentication strategy combines password hygiene with modern identity strategies. Use unique credentials per admin account, and consolidate admin access under a centralized identity provider when possible. Implement MFA as a baseline and require it for all sensitive roles. Leverage RBAC to assign the least privilege necessary for each task, and isolate admin interfaces on protected networks. Keep a documented password reset workflow that includes approval steps and audits. Finally, consider password managers for shared accounts and rotate admin credentials on a defined cadence to minimize stale access.
Role-based access control and user management
Graylog supports granular user management and RBAC to limit who can perform critical operations. Treat admin accounts as high-risk entries and assign them to controlled groups with clearly defined responsibilities. Regularly audit group memberships, monitor changes in permissions, and revoke access promptly when personnel change roles or leave the organization. Encourage the use of service accounts with time-bound credentials for automation. Document all permissions in an access control matrix to simplify compliance reviews and security audits.
MFA and encryption considerations
Multi-factor authentication adds a strong barrier against credential theft, especially for admin users. Pair MFA with end-to-end TLS encryption for the admin UI and API endpoints to protect data in transit. In graylog deployments, ensure TLS is enforced on all web and API surfaces, and keep certificate authorities up to date. When possible, prefer hardware-backed or app-based MFA options that support recovery mechanisms. Regularly test MFA failover and backup codes to prevent lockouts during downtime.
Configuring Graylog LDAP/SSO integration
Integrating Graylog with LDAP or SSO providers can streamline secure login while maintaining centralized control. Configure your identity provider to enforce password policies and MFA, and map Graylog roles to directory groups to preserve RBAC semantics. Ensure proper attribute mappings for user provisioning, disable anonymous access, and monitor authentication events through centralized logging. Properly testing the integration in a staging environment helps catch misconfigurations before a production rollout.
Auditing, logging, and monitoring admin activity
Auditing admin actions is essential for detecting credential abuse and operational mistakes. Enable comprehensive audit logs for user creation, permission changes, and login events. Centralize these logs to a secure SIEM or log analytics platform, and set up alerts for anomalous patterns such as rapid password changes, unusual login times, or access from unexpected locations. Regular reviews of audit trails improve incident response readiness and support compliance with security standards.
Verifying secure configuration and ongoing maintenance
Verification is ongoing, not one-and-done. Periodically verify that default credentials do not exist, MFA remains enforced, and RBAC policies align with current responsibilities. Run automated configuration scans that check for exposed endpoints, weak password policies, and outdated components. Schedule quarterly reviews of IAM settings, network exposure, and backup integrity. Finally, build a culture of security ownership by training admins on secure management practices and keeping documentation current.
Comparison of default login behaviors in Graylog deployments
| Aspect | Default Behavior | Best Practice |
|---|---|---|
| Initial admin login | Often shipped with default credentials | Remove default account; create a unique admin user |
| Password policy | Weak or reused passwords allowed | Enforce strong passwords and rotation |
Your Questions Answered
What is the 'graylog default login' and why is it risky?
The graylog default login refers to the initial credentials shipped with Graylog or the first admin path exposed during deployment. Leaving these unchanged creates a strong attack surface for unauthorized access. Always replace with a unique admin account and enforce tight access controls.
The graylog default login is the built-in admin account. Leaving it unchanged is risky; replace with a unique admin and enforce strict access.
How do I disable or change the default admin credentials in Graylog?
Create a new admin user, assign appropriate roles, and delete or disable the default account. Ensure that all admin actions require MFA and are logged for auditing.
Create a new admin user, switch roles, and delete the default admin. Add MFA and enable audit logs.
Does Graylog support MFA and SSO for admin access?
Yes, Graylog can integrate with MFA providers and SSO, depending on your version and deployment. Configure your identity provider and enforce MFA for all admin users.
Graylog supports MFA and SSO via integration with identity providers. Enforce MFA for all admins.
What monitoring should I implement to catch unauthorized admin activity?
Enable and centralize audit logs, monitor for unusual login times, and alert on changes to admin users or roles. Regular reviews help detect credential abuse early.
Set up centralized audit logs and alerts for admin changes. Watch for odd login times.
What are common misconfigurations that leave graylog exposed?
Common issues include exposed dashboards, weak password policies, and unauthenticated admin endpoints. Regularly review access controls and network exposure to minimize risk.
Be wary of exposed dashboards and weak policies. Regular reviews reduce risk.
“Security isn't a one-time setup; it requires ongoing hardening and monitoring. Default Password's guidance helps teams stay ahead of credential misuse.”
Key Takeaways
- Change the default admin password immediately
- Enable MFA for all admins and enforce RBAC
- Audit admin activity and maintain centralized logs
- Regularly review IAM and network exposure to prevent credential abuse