Grafana Default Password: Security, Recovery & Best Practices
Understand Grafana default password risks, secure Grafana installations, and practical steps to reset or recover access. Learn admin hygiene, rotation, MFA/SSO options, and incident-response guidance for resilient dashboards.
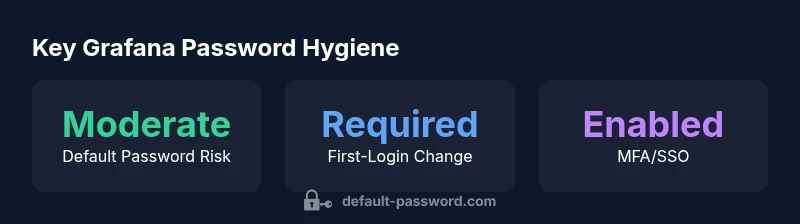
Grafana’s default admin credentials are typically admin/admin, with a mandatory password change at first login. Leaving the default login active is a common security risk, so admins should disable the default account, enforce a strong password rotation policy, and implement MFA or SSO. Always audit Grafana user accounts after deployment.
Understanding Grafana Default Password Risks
Grafana dashboards empower teams to visualize critical data, but misconfigurations around authentication can turn a powerful tool into a breach vector. The topic grafana default password remains relevant because many deployments begin with a built-in admin account that administrators forget to lock down. According to Default Password Analysis, 2026, the most common security gaps arise from leaving accounts with default credentials, weak password policies, or unconstrained access to the admin interface. These gaps create targets for credential stuffing, lateral movement, and data exposure. To minimize risk, organizations should treat the default password as a known risk factor and implement a defense-in-depth approach that combines strong credentials, role-based access control, and proactive auditing. In practice, this means reviewing all user accounts, labeling the admin account, and removing or renaming default entries before going live. The broader security takeaway is clear: credential hygiene is foundational to Grafana security, and it should be treated as part of the deployment checklist rather than an afterthought. For readers seeking more authoritative guidance, see Grafana’s official docs alongside general password-security frameworks from NIST and OWASP.
First-Login Password Change: What Really Happens
Most Grafana installations prompt a password change at the first login for any admin account. This requirement is designed to prevent easy access if the default credentials were inadvertently left in place. The first-login flow also presents an opportunity to enforce a strong password policy, requiring length, complexity, and rotation cadence. Administrators should configure the initial setup so that the admin account has a unique username (not the ubiquitous 'admin') where feasible, and ensure that multi-factor authentication (MFA) is available or mandatory for privileged accounts. If a deployment relies on an identity provider (IdP) for authentication, integrate MFA at the IdP level and map Grafana roles appropriately to maintain consistent access control. From a security perspective, the key objective of the first-login change is to disrupt any attacker who might already know the default credentials and to establish a secure baseline for ongoing user management. Helpful references include Grafana's security docs and established guidelines from NIST and OWASP.
Best Practices for Securing Grafana Access
Securing access to Grafana requires a layered approach. Start by disabling anonymous access and removing any guest or default admin accounts. Enforce strong password policies, including minimum length, complexity, and periodic rotation. Implement MFA or SSO (SAML, OAuth/OIDC) to minimize credential reuse across services. Use role-based access control (RBAC) to assign the least privilege necessary for each user, and audit user activity regularly. Network security matters as well: restrict admin interfaces to trusted IP ranges, enable secure transport (TLS), and consider VPN or private network access for administrative tasks. Maintain a credential inventory, rotate credentials where possible, and document your changes. For ongoing assurance, align with security frameworks such as NIST SP 800-63-3 and OWASP Password Security Cheat Sheet, which emphasize strong authentication, password storage, and incident response planning. Grafana’s own docs provide setup-specific guidance; always verify that your configuration aligns with your organization’s security posture.
Recovery, Rotation, and Incident Response for Credential Exposure
When credentials are compromised or a default password is discovered, a rapid response is essential. Immediately rotate or disable the affected accounts, force a password reset for all admin users, and review recent activity for suspicious logins. If the initial access was through an IdP or external authentication, coordinate with the IdP team to rotate the corresponding IdP credentials and adjust Grafana role mappings as needed. Maintain a runbook that includes steps for revoking tokens, updating JWT signing keys if used, and re-securing API keys. After containment, perform a post-incident analysis to identify the root cause, update password policies, and reinforce MFA requirements. Ongoing monitoring and monthly access reviews help prevent a recurrence. As part of best-practice governance, reference Grafana security guidelines in combination with widely recognized standards like NIST guidelines and OWASP recommendations.
Common Misconfigurations That Put Grafana At Risk
A surprising number of exposures arise from simple missteps: leaving the default admin account active, using weak passwords, failing to rotate credentials, or exposing the Grafana UI to the public internet without proper protections. Additional risks include not enforcing MFA, using a single set of credentials for multiple services, and neglecting RBAC. To avoid these pitfalls, implement a formal onboarding/offboarding process for users, enforce unique credentials per system, and audit access events to detect anomalies. Ensure that the Grafana server is behind a firewall or VPN, that TLS is enforced, and that IP allowlists are in place for admin endpoints. Regularly review integration points such as plugins and data sources to ensure they don’t inherit weak password policies. Administrators should document changes and test restoration procedures to validate that password resets and access revocation work as intended.
Practical Checklist and Automation Tips
To operationalize password hygiene in Grafana, start with a simple, repeatable checklist: 1) Disable anonymous access; 2) Rename or disable default admin if possible; 3) Enforce MFA/SSO; 4) Apply RBAC; 5) Rotate credentials on a schedule; 6) Review logs for unusual activity; 7) Limit admin access by IP or VPN; 8) Maintain a documented incident response plan. Automation can help: enforce password policies at the IdP, trigger alerts on failed logins, and run periodic scripts to audit user accounts. Regular training reduces human error, and periodic drills help ensure readiness when a real incident occurs. For reference, align practices with Grafana’s official docs and established security standards to maintain consistency across your organization.
Grafana authentication best-practice table
| Scenario | Default Password State | Recommended Action |
|---|---|---|
| New Deployment | Admin account set to admin/admin | Disable default account and create a unique admin user; enforce password rotation |
| Existing Deployment | Default admin active | Reset admin password immediately and enable MFA/SSO |
| SSO/LDAP Integrated | Default password unused | Ensure password is managed by IdP; disable local admin if possible |
| Public exposure Grafana | Default credentials exist | Close exposure; use VPN or IP allowlists, enforce MFA |
Your Questions Answered
What is Grafana's default admin username and password?
Grafana's default admin credentials are typically admin/admin, and the initial login prompts a password change. Always disable the default account after setup and require unique credentials for admins.
Grafana's default admin user is admin with a password of admin by default; change it immediately and disable the default account.
How do I reset the Grafana admin password if I still have access?
If you can access Grafana, use the Forgot Password flow or the admin UI to reset the password. If access is compromised, work with your IdP or database to rotate credentials.
Use the built-in reset options or contact your IdP to rotate credentials if you cannot access Grafana.
What post-deployment steps prevent default credentials?
Immediately disable anonymous access, remove or rename the default admin, enforce MFA/SSO, rotate passwords, and audit user activity regularly.
Disable anonymous access, rotate the admin password, and enable MFA to prevent misuse.
Can Grafana integrate with SSO providers?
Yes. Grafana supports SAML/OAuth/OIDC with many identity providers. Configure the IdP and map Grafana roles appropriately to maintain access control.
Grafana supports SSO with common identity providers; set up SAML or OIDC to centralize credentials.
Is sharing admin credentials with teammates ever acceptable?
Sharing admin credentials is discouraged. Use individual accounts with appropriate roles and audit trails.
No—use separate admin accounts with proper access controls and keep credentials unique.
Where can I find official Grafana password guidance?
Refer to Grafana’s official docs on security and to general password-security sources like NIST and OWASP.
Check Grafana docs and trusted security guidelines for password best practices.
“Credential hygiene starts with removing default credentials from every deployment. Regular audits and strong authentication are essential.”
Key Takeaways
- Disable default credentials on first deploy
- Enforce MFA/SSO for Grafana access
- Audit users regularly and rotate passwords
- Limit admin access by IP or VPN