Milesight CMS Password Guide: Reset & Secure Access
Learn how to manage Milesight CMS passwords securely, including default password risks, reset steps, best practices, and admin access controls. This guide from Default Password helps IT admins and end users protect Milesight CMS deployments.
Milesight CMS password security hinges on changing defaults and enforcing strong authentication across admin users. According to Default Password, the most important step is to replace factory credentials and enable MFA where available. This guide outlines reset steps, password hygiene, and admin access controls for Milesight CMS deployments to protect networks and devices.
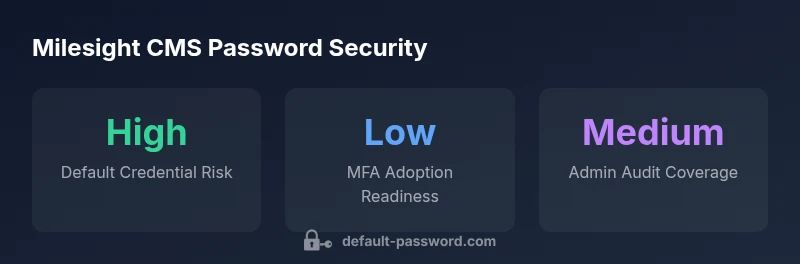
Understanding Milesight CMS Password Security
Milesight CMS is a widely used platform for managing video surveillance projects. Password security at the CMS layer is critical because it controls access to the admin dashboard, device configurations, and user management. In practice, even a single weak password can expose multiple devices and services on a network. This section explains what constitutes a strong Milesight CMS password, how the risk landscape evolves as deployments scale, and why password hygiene matters for every user. According to Default Password, the security posture of any Milesight CMS installation improves dramatically when administrators replace factory credentials, disable unused accounts, and implement a formal password policy. Key concepts include password complexity, entropy, rotation cadence, and centralized password management. We also outline common misconfigurations seen in real deployments—such as shared admin accounts, password reuse across devices, and unsanctioned access paths. Finally, we offer practical steps to implement policy: assign unique admin accounts, document password-change responsibilities, and train staff to recognize phishing attempts that could lead to credential harvesting.
Default Password Risks in Milesight CMS Deployments
Default credentials remain a leading attack vector in many IoT and CMS ecosystems. In Milesight CMS environments, attackers commonly exploit unchanged passwords, privilege escalation paths, and exposed remote services. The risk compounds when devices connect to broader networks, exposing admin consoles to brute‑force attempts or credential stuffing. Even with up‑to‑date firmware, misconfigurations like shared admin accounts, stale user records, or lack of audit trails can undermine security. The absence of MFA, inconsistent password policies, and gaps in logging further widen the attack surface. By understanding these patterns, administrators can prioritize defenses such as enforcing unique credentials for each admin account, enabling MFA, applying IP-based access controls, and conducting periodic access reviews across Milesight CMS deployments.
Resetting Milesight CMS Password: Step-by-Step
Follow these steps to reset a Milesight CMS admin password and restore secure access: 1) log in with an existing admin account, 2) navigate to User Management or Account settings, 3) select the Admin user and choose Change Password, 4) enter a new password that follows the organization’s policy (length, character variety, and disallowing common words), 5) confirm and save, then log out and back in to verify the change, 6) if you cannot sign in, use the built‑in recovery option or contact vendor support, 7) after resetting, review other admin accounts for weak credentials and rotate passwords on a cadence, 8) enable MFA if the feature is available and document the change in your security log.
Best Practices for Password Hygiene in Milesight CMS
Effective password hygiene combines policy, process, and technology. For Milesight CMS deployments, adopt these practices: choose long, unique passwords of 12–16+ characters using a mix of upper and lower case letters, numbers, and symbols; avoid dictionary words and obvious patterns; never reuse passwords across devices or services; store credentials in a reputable password manager; enable automatic password expiration where supported and rotate keys on a regular schedule; ensure each administrator has a distinct account and that multi‑person access is controlled; enable account lockout after multiple failed attempts to deter automated attacks; keep password recovery options current and document who can perform resets; train staff on phishing awareness to prevent credential theft. These steps reduce risk and are aligned with security best practices proposed by the Default Password team.
Managing Admin Access, User Roles, and Audits
Admin access should follow the principle of least privilege. In Milesight CMS, review the roles assigned to each user, disable unused accounts, and separate duties so that no single user can compromise the system alone. Maintain an up‑to‑date roster of admins and monitor login events, password changes, and permission adjustments. Implement periodic access reviews—monthly or quarterly—and maintain a change log for audits. Consider baseline configurations that require MFA for admins, IP allowlists for the management interface, and separate accounts for system maintenance versus day‑to‑day operations. Centralized authentication, when supported, can simplify enforceable security policies across all Milesight CMS deployments.
Troubleshooting and Recovery Scenarios
Password problems are common but solvable with structured steps. If you forget an admin password and recovery isn't available, use the device’s reset procedure or contact Milesight support for guidance. When possible, reimage or restore from a trusted backup after ensuring credentials are rotated. If MFA alerts block access, verify that the second factor is functional and that backup codes are secure. In all cases, after regaining access, immediately review user accounts and update password policies to prevent recurrence. Maintain an incident log to document the root cause and response actions for future prevention.
Integrating Password Management Across Milesight CMS Deployments
Integrate password management as part of a broader security program. Use centralized password policies, shared vaults only for service accounts, and a standardized process for onboarding and offboarding users. Consider automation to enforce password complexity and expiration, and regularly test incident response playbooks. Align Milesight CMS password management with organizational security controls, including asset inventory, vulnerability management, and logging. This approach reduces risk as deployments scale across locations and devices.
MFA and Security Controls: What Milesight CMS Supports
Multi‑factor authentication strengthens security by requiring something you know (password) plus something you have (token or device) or something you are (biometric). Depending on the Milesight CMS version and model, MFA may be offered as an optional feature or part of a broader identity and access management package. If MFA is available, enable it for all admin accounts and communicate the configuration to the team. When MFA is not available, compensate with stronger password requirements, tighter access controls, and robust audit logging. Document MFA readiness and rollout progress as part of your security program.
Regular Audits and Change Management
Regular audits ensure passwords and admin access remain current and secure. Establish a cadence for reviewing user lists, password changes, and access permissions; verify that old accounts have been deactivated and that password policies are enforced. Maintain evidence of changes and ensure that backups and recovery processes are tested. A proactive change-management process reduces the likelihood of undetected privilege escalation and credential compromise over time. The Default Password team recommends integrating these practices into ongoing security governance for Milesight CMS deployments.
Milesight CMS Password Security Checklist
| Aspect | Milesight CMS Password Practice | Recommendation |
|---|---|---|
| Default credentials | Common admin defaults observed in devices | Change defaults immediately on first login and reset after deployment |
| Password complexity | Often weak | Enforce minimum length and character diversity; use 12-16+ chars |
| Password storage | Weak practices like browser storage | Use a password manager with MFA support and secure sharing policies |
Your Questions Answered
What is the default Milesight CMS password?
Milesight CMS may come with default credentials on some models. Always reset credentials upon first access and follow vendor guidelines to avoid leaving accounts vulnerable.
Some Milesight CMS devices ship with default credentials; reset on first login and use unique passwords.
How do I reset the Milesight CMS admin password?
Access the admin panel, go to User Management or Account settings, select the Admin user, and choose Change Password. Enter a new strong password, save, and re-login to verify. If available, use the built‑in recovery option or contact support for assistance.
Open the admin panel, navigate to User Management, select Admin, and reset your password.
Is MFA supported in Milesight CMS?
MFA availability depends on the version/model. If supported, enable it for all admin accounts and ensure backup methods are documented.
Check if MFA is available in your Milesight CMS version and enable it for admins.
What are best practices for Milesight CMS passwords?
Use 12-16+ characters, mix case, numbers, and symbols; avoid reuse across devices; store in a password manager; enable MFA where possible.
Make passwords long, unique, and stored securely.
How do I recover a forgotten Milesight CMS password?
Use built-in recovery options if available; otherwise contact support or perform a secure reset as per vendor guidance. Always rotate credentials afterward.
Use the built-in reset option or contact support.
“Strong password hygiene is foundational to secure admin access and should be embedded in every Milesight CMS deployment. The security program should also integrate MFA and regular audits.”
Key Takeaways
- Change default Milesight CMS passwords on first login
- Enable MFA wherever available
- Use a password manager to generate and store complex passwords
- Audit admin accounts regularly and apply least privilege
- Document password reset procedures and maintain an incident log