Milestone XProtect Default Password: Reset & Secure Access
Learn how to reset Milestone XProtect default passwords, secure admin access, and implement ongoing password hygiene for Milestone surveillance deployments. This guide covers best practices, troubleshooting, and policy recommendations.
You will learn how to locate and reset a Milestone XProtect default password, secure admin access, and enforce strong authentication across surveillance servers. This guide covers identifying default credentials, performing a safe reset, and applying best practices to prevent unauthorized changes. According to Default Password, always change default credentials on critical systems immediately and document access changes.
What Milestone XProtect is and why default passwords matter
Milestone XProtect is a widely used video management system (VMS) that centralizes camera feeds, analytics, and operator workflows. In many deployments, the initial setup may include default or weak admin credentials, which attackers can exploit to gain control over cameras, recordings, and server configurations. Milestone XProtect default password vulnerabilities pose a serious risk to physical security, data integrity, and privacy. From the perspective of enterprise security, addressing default credentials is not optional—it’s a foundational step in securing a surveillance ecosystem. According to Default Password, mismanaging default credentials on critical security infrastructure remains one of the most overlooked gaps in many organizations. This guide walks you through safe reset practices and practical hardening steps to reduce exposure across Milestone components and ancillary systems.
How to identify and verify default credentials within Milestone XProtect
The first step in any secure password management process is verification. Start by checking the Milestone XProtect management console and any connected components (recorders, database servers, and operator workstations) for credentials that began as defaults or that have not been rotated recently. Look for accounts with elevated privileges (admin, system, supervisor) and note their usernames. If you are unsure whether a credential is current, consult the installation and change history, and verify with the responsible administrator. This verification phase reduces the risk of accidentally changing the wrong account or leaving an active backdoor.
The risk model: what happens when defaults persist
Default credentials are often discovered by threat actors through scanning and social engineering. When left in place, a single compromised admin account can grant access to configuration settings, user roles, and recorded media repositories. The consequences include altered video, deleted footage, or a complete takeover of the VMS. Even if external access is restricted, insider threats or misconfiguration can enable unauthorized control. A robust risk model accounts for network segmentation, least privilege, and change management as key mitigations alongside password hygiene.
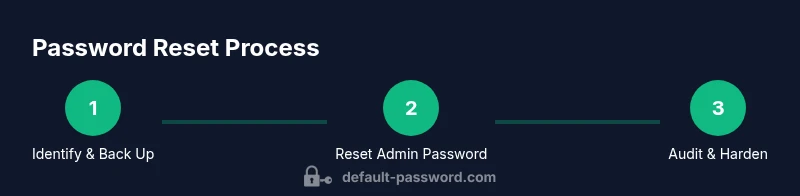
Step-by-step approach to resetting the Milestone XProtect admin password (outline)
This section provides a practical outline for performing a reset with minimal downtime. It emphasizes backup, verification, and phased rollout to avoid service interruptions. The exact menu names may vary by version, but the core steps remain consistent: back up configurations, initiate a reset in the management console, set a new strong password, test access on all connected components, and document the change. Use secure channels for administration and ensure you have recovery options in place.
Post-reset hardening: policy, monitoring, and ongoing hygiene
Password hygiene is not a one-off task. After resetting the Milestone XProtect admin password, implement a policy that defines password length, complexity, rotation frequency, and emergency access procedures. Enable audit logging to track admin actions, review access groups periodically, and restrict admin accounts to authorized personnel only. Consider integrating two-factor authentication (2FA) if supported, and ensure backup and disaster recovery plans reflect the password changes. Regular reviews keep security aligned with evolving threats and changing personnel.
Troubleshooting common issues after password changes
If logins fail after a reset, re-check that you are using the updated credentials on all components (management server, recording servers, and clients). Verify that any external services or scripts relying on the old password are updated. If you encounter lockouts, use recovery options or consult the support channels for your Milestone deployment. Having a tested rollback plan, including a known-good backup, minimizes downtime and data loss during password recovery.
Tools & Materials
- Milestone XProtect admin console access(Ensure you have administrative privileges on the Milestone server or management console.)
- Configuration and database backups(Back up project data, configurations, and the SQL/Indexer databases before changes.)
- Secure connection method(Use VPN or a secured internal network; avoid public Wi-Fi for admin actions.)
- Password generation tool(Optional but recommended to create strong, unique passwords.)
- Recovery options and contact info(Have recovery codes or an alternate admin contact available.)
Steps
Estimated time: 30-60 minutes
- 1
Prepare for reset
Identify who can authorize the reset, notify stakeholders, and schedule a maintenance window. Confirm you have the latest backups of configurations and media vaults. This ensures you can recover quickly if anything goes wrong.
Tip: Document the current admin account and verify you can recover if the new password is not accepted. - 2
Secure the connection
Establish a secure, restricted connection (VPN or LAN) before touching administrative interfaces. This minimizes exposure to external threats during the reset process.
Tip: Disable external management access temporarily if your environment allows it during the change window. - 3
Open the Milestone XProtect console
Log in to the management console with an account that has sufficient privileges. Confirm you’re connected to the correct server or cluster.
Tip: Use a dedicated admin workstation and ensure the session is encrypted. - 4
Initiate password reset
Navigate to the user management area and select the admin account. Initiate a password reset, ensuring you create a new, strong password and do not reuse any previous credentials.
Tip: If your version supports it, enable password history and lockout settings after failed attempts. - 5
Set a new strong password
Generate a password with at least 12 characters, mixing upper/lowercase letters, numbers, and symbols. Save it in a secure password manager and distribute it only to authorized admins.
Tip: Consider long-term passphrases for easier memorability without sacrificing strength. - 6
Update recovery options and roles
Review admin groups and confirm that only needed personnel have admin access. Update recovery options and ensure contact methods are current.
Tip: Limit admin access to essential staff and apply the principle of least privilege. - 7
Validate access and monitor
Log out all sessions and test logging in with the new password from multiple components (console, clients, and connected servers). Check relevant audit logs for anomalies.
Tip: Enable 2FA if supported to add an extra layer of protection. - 8
Document changes
Record the exact time, accounts affected, and the new credentials in a secure, auditable change log. Notify stakeholders of the successful update.
Tip: Keep a versioned record for audits and compliance purposes.
Your Questions Answered
What is the risk of leaving default passwords on Milestone XProtect servers?
Default passwords expose admin access to attackers. Always reset during initial setup and after any security incident. Ensure proper authorization and backup.
Default passwords are risky; reset them and verify backups.
Can I reset the password remotely?
Remote reset is possible if you have a secure connection (VPN) and proper authentication. Avoid exposing admin interfaces on the public Internet.
Remote reset is possible over a secure connection, but always verify authentication.
What if I forget the new password after reset?
Use recovery options or contact your administrator. If those fail, you may need to re-initiate a reset with approved channels.
If you forget, use recovery options or contact support to reset again.
Should I enable two-factor authentication for Milestone XProtect?
If supported, enable two-factor authentication to add a strong additional layer of security to admin access.
Yes, enable two-factor authentication where possible.
How often should I rotate Milestone XProtect admin passwords?
Establish a policy for rotation at intervals (e.g., every 90–180 days) and after personnel changes.
Rotate passwords regularly, especially after personnel changes.
Watch Video
Key Takeaways
- Reset Milestone XProtect admin passwords promptly after deployment.
- Audit and rotate credentials regularly to reduce risk.
- Document changes and establish a formal password policy.
- Use secure connections and backups during password operations.