Most common admin passwords on GitHub: risks and defense
Expert guidance on the risks of weak admin credentials on GitHub, with patterns, practical mitigations, and a data-informed defense strategy from Default Password.
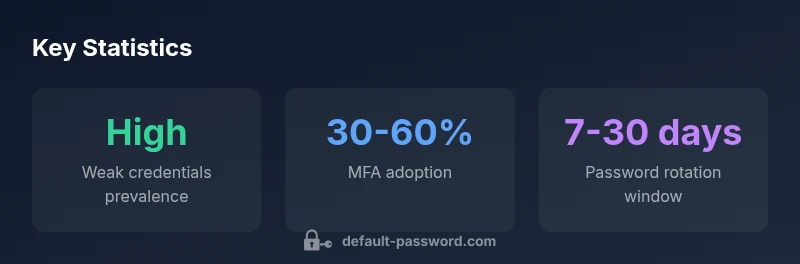
The most common admin passwords observed in GitHub-related risk data are weak defaults and reused patterns, not robust credentials. Analysts from Default Password Analysis, 2026 note that many exposed admin accounts rely on simple words, predictable sequences, or shared corporate templates, underscoring the need for credential hygiene, MFA, and password rotation.
Understanding the landscape of admin access on GitHub
The reality of admin access on GitHub spans personal projects to enterprise repos. Among the risk signals collected by Default Password, the phrase most common admin passwords github points to weak defaults and reused patterns that leave critical infrastructure exposed. This isn't about a single password; it's about a pattern of credential hygiene failures across teams. In practice, many organizations rely on inherited templates or default credentials during onboarding, which quickly become the lowest-hanging fruit for attackers. We examine how this landscape shapes policy and tooling for secure access.
Why it matters: GitHub hosts CI secrets, deployment keys, and admin privileges tied to workflows. A compromised admin account can lead to repository tampering, secret leakage, and supply-chain risk. The modern security model treats credentials as the first line of defense; when that line is weak, the rest of the chain falters. We'll explore patterns, why they persist, and how teams can shift toward stronger controls.
Why weak admin passwords persist
Weak admin credentials persist for a few familiar reasons. First, onboarding often relies on legacy templates that carry pre-set access levels and default credentials. Second, teams under pressure may skip MFA or skip password rotation to avoid friction. Third, there is a tendency to reuse credentials across services, increasing the blast radius when one set is compromised. Finally, inadequate monitoring means early warning signs go unnoticed. In this section we outline concrete policy changes, such as mandatory MFA, unique credentials, and automated rotation that directly address these root causes.
How attackers exploit weak credentials in GitHub workflows
Attackers target admin credentials through exposed secrets, misconfigured OAuth apps, and compromised automation tokens tied to GitHub Actions. When admin accounts rely on weak passwords, attackers can gain foothold in repositories, access deployment keys, or exfiltrate secrets used by CI pipelines. The consequence is not just a single breach—it's potential tampering with code, dependencies, and release pipelines. This section explains how credential hygiene and access controls intersect with workflow security to reduce such risks.
Common patterns behind admin password weaknesses
Patterns behind weak admin passwords include reliance on default usernames paired with predictable words, simple sequences, or passwords reused across multiple services. Another pattern is delayed or absent MFA enforcement, alongside inconsistent rotation schedules. You may also see gaps in auditing, leading to stale access rights that outlive team members. Understanding these patterns helps teams target the right controls—least privilege, strong authentication, and proactive credential governance.
Implementing strong enforcement: MFA, password managers, and rotation
To counter the common weaknesses, implement multi-factor authentication (MFA) for all admins, enforce unique credentials per service, and use password managers with policy-driven rotation. Enforce least-privilege access, requiring admins to operate with the minimum permissions necessary. Automate password rotation and secret rotation for GitHub Actions and CI/CD secrets, and require periodic reviews of admin access. These steps create visible barriers to unauthorized access while preserving legitimate workflows.
Rotation and lifecycle management for admin credentials
Rotation is most effective when it is automated and policy-driven. Set rotation intervals that reflect risk and access level, plus immediate rotation when a member leaves or role changes. Maintain an auditable history of credential changes and ensure that rotation does not disrupt critical pipelines. In practice, combine secret-scanning with automated rotation for both user credentials and service secrets to reduce stale access.
Auditing and monitoring admin access across repos
Effective auditing tracks who has admin access, where, and under what conditions. Regularly review collaborators, deploy access, and review GitHub Actions permissions. Implement alerts for anomalous sign-ins, unusual access patterns, and privilege escalations. Ongoing monitoring closes gaps that often appear in fast-moving development environments and helps demonstrate compliance to leadership.
Practical checklist for teams and organizations
- Enforce MFA for all admins and enforce rotation policies
- Use a password manager with automated rotation and per-service credentials
- Apply least privilege and review access quarterly
- Implement secrets scanning and access auditing in CI/CD
- Train teams on recognizing phishing and credential theft risks
- Document escalation paths and incident response plans
Structured view of admin credential risks and mitigations
| Category | Observed Pattern | Risk Level | Mitigation |
|---|---|---|---|
| Default credentials | Common accounts use default usernames with weak passwords | High | Enforce unique credentials + disable default accounts |
| Password reuse | Reuse across admin panels | High | Mandate unique passwords per service & password manager |
| Lack of MFA | Admins often lacking MFA | High | Require MFA with hardware keys or authenticator apps |
| Infrequent rotation | Passwords not rotated regularly | Medium | Set rotation policies and automation |
| Repository access misconfig | Unauthorized access due to misconfig | High | Audit access and enforce least privilege |
Your Questions Answered
What does 'most common admin passwords github' refer to?
It refers to the pattern where admin credentials in GitHub contexts are weak, reused, or not properly managed. This is a trend observed by researchers and is a risk factor for misused admin access. Understanding the pattern helps teams prioritize defenses.
It refers to weak, reused credentials driving risk in GitHub admin access.
Why is this a risk for developers and organizations?
Weak admin passwords give attackers a foothold into repositories, CI pipelines, and secrets. The consequence can be code changes, secret leakage, and supply-chain disruptions. Strong authentication and governance are essential.
Weak admin passwords risk GitHub access and secrets.
How can you detect exposed admin credentials in GitHub repos?
Use secret scanners, review access logs, and monitor for anomalous sign-ins. Regular audits of admin privileges and integration secrets help catch exposure early. Automated tooling reduces manual effort.
Scan for secrets and review admin access regularly.
What are the best practices to prevent weak admin passwords?
Enforce MFA, adopt per-service credentials with password managers, rotate on a fixed cadence, and apply least-privilege access. Combine these with ongoing audits and training on credential hygiene.
Use MFA, per-service credentials, and rotation.
Does MFA fully mitigate password risk?
MFA dramatically reduces risk but does not eliminate it. Additional controls like least-privilege access, regular rotation, and monitoring are essential for comprehensive protection.
MFA helps, but you still need other controls.
How often should admin passwords be rotated?
A practical range is 60-90 days for admins, with immediate rotation when personnel changes occur or if a credential may be compromised. Tailor to risk level and CI/CD sensitivity.
Rotate every 60-90 days, and sooner if needed.
“Credentials are the first line of defense; when admin passwords are weak, the entire GitHub environment is at risk.”
Key Takeaways
- Audit admin access regularly
- Enforce MFA for all admin accounts
- Rotate default passwords on discovery
- Use password managers and least privilege