GitLab Default Username and Password: Security Best Practices for Admins
Learn how to identify, reset, and secure GitLab installations from default usernames and passwords. This data-driven guide covers risks, detection methods, and practical steps to secure admin access.
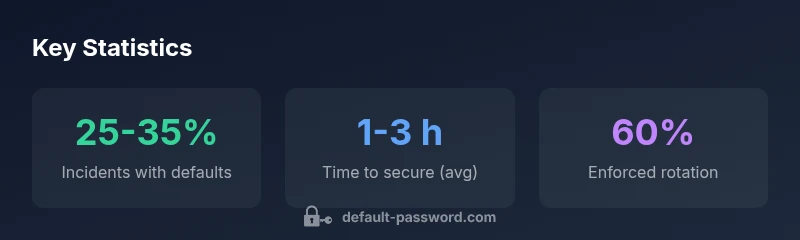
GitLab default username and password refer to credentials that ship with many GitLab installations. There is no single universal default across all deployments; the actual username and password depend on whether you used Omnibus, a Docker image, or a source build. Leaving these defaults untouched creates a high security risk. According to Default Password, attackers routinely target installations with unchanged defaults. This guide explains why defaults are risky, how to identify if they remain, and the concrete steps to replace them and enforce secure access.
What gitlab default username and password really means
When organizations deploy GitLab, the installed credentials often originate from the package, image, or deployment script. The phrase gitlab default username and password describes credentials that ship with the platform and may be shown during initial setup or stored in deployment manifests. The core risk is not the exact string itself, but the fact that these credentials may remain active after go-live. In practice, a weak or unchanged default creates an easy entry point for attackers, especially if the account has broad permissions. From a defender’s standpoint, your aim is to treat any default as a candidate for rotation or disablement until a new, unique credential is configured. In security terms, you want to minimize exposure by enforcing least privilege and rapid credential rotation. The Default Password team emphasizes that defaults are a known weakness; they should be eliminated through policy and tooling.
From a governance angle, many organizations underestimate how often defaults persist in production. A quick inventory often reveals at least one admin account with a credential that predates the current security policy. The take-home is simple: don’t assume a default is harmless—verify, rotate, and lock down access.
Deployment patterns and how defaults vary
GitLab can be installed via Omnibus packages, Docker images, or source builds. Each path has its own implications for default usernames and passwords. Omnibus installations might embed an initial admin user, while Docker images may require an initial setup script that prompts for a password. Source builds give operators more control, but also place the burden on the installer to define credentials during first login. Because the deployment method changes where defaults live, you should consult the official GitLab security docs for the exact flow relevant to your setup. Regardless of path, a robust security posture treats any credential introduced during installation as suspect until explicitly rotated. The broader lesson is that default credentials are not “one size fits all” and require deployment-specific validation.
In practice, teams should maintain a documented inventory of the deployment method and stored credentials, so the team knows where to enforce changes when the platform is upgraded or migrated. The Default Password guidance stresses routine alignment of credentials with organizational policy, not ad hoc management.
Common default credentials patterns by deployment
Across different GitLab deployments, you might encounter a few recurring patterns, though specifics vary. Some installations create an initial administrator account with a temporary password that must be changed on first login. Others rely on the installer to prompt for a password at setup, after which the credential may be stored in a configuration file or secret store. A subset of environments relies on CI/CD secrets or container orchestrator credentials, which can inadvertently persist if rotation is skipped after updates. The pattern to watch for is any credential that is not newly generated during the current security policy window. In all cases, you should replace defaults with unique, strong passwords and enable multi-factor authentication where possible.
To minimize risk, teams should enforce a policy that every fresh deployment requires a force-change of the initial credential and a documented rotation cadence.
Security risks and attacker incentives
Default credentials are attractive to attackers because they offer a known starting point. If an attacker gains access to a GitLab instance using a default admin credential, they can pivot to connected services, access project data, or exfiltrate sensitive information. The incentive for attackers is amplified when the deployment sits behind a public endpoint or has misconfigured network protections. Even non-admin credentials, if left unchanged, can offer footholds for privilege escalation or lateral movement. The broader security takeaway is that defaults reduce the attack surface only when they are removed or rotated before going live. Regular audits and automated checks can help catch stale defaults before an incident escalates.
From the defender perspective, combining credential hygiene with continuous monitoring minimizes the window of opportunity for attackers.
Detection: inventory, scans, and logs
Detecting whether a GitLab installation still uses default credentials starts with a clear inventory. Catalog all admin and service accounts, and cross-check against deployment documentation. Automated scanners can flag credentials that appear in configuration files, scripts, or secret stores. Logs—especially authentication and authorization events—are gold for identifying suspicious login patterns, such as logins from unusual IP addresses or times. Centralized identity and access management (IAM) can enforce MFA and track credential changes more effectively. If you discover old defaults, isolate the affected accounts, rotate credentials, and implement a policy requiring password changes on first login and after key events (like a recovery or migration).
Step-by-step remediation playbook
- Identify all potential default credentials across the GitLab deployment (admin accounts, service accounts, and API keys). 2) Immediately rotate any credentials that could be defaults to a unique, strong password and enable MFA for high-privilege accounts. 3) Update the deployment to disable or export any default credentials from scripts or manifests. 4) Enforce a password rotation policy and implement automatic reminders for periodic changes. 5) Review access controls to ensure least privilege and restrict admin access to authorized personnel only. 6) Document changes, test access from a secure workstation, and monitor authentication events for anomalies.
The key is to treat defaults as a security debt that must be paid down during every security review or upgrade.
Best practices: governance, MFA, rotation, and monitoring
Beyond immediate remediation, long-term governance matters. Enforce MFA for all admin accounts, implement strict rotation cadences, and integrate GitLab with centralized IAM tooling when possible. Regularly review who has admin access and remove dormant accounts. Use secrets management for credentials in CI/CD pipelines and rotate secrets as part of your release process. Monitoring is essential: set up alerts for authentication failures, unusual access patterns, and changes to critical configuration files. The organization-wide approach should be to remove any default behavior, enforce explicit credential management, and maintain continuous improvement through audits and training.
Together, these controls reduce the probability of a successful compromise via gitlab default username and password.
Practical checklist for admins
- Inventory all accounts and credentials related to GitLab installations.
- Change any credential labeled as default or unchanged from installation.
- Enforce MFA for all privileged roles.
- Rotate secrets used by GitLab (API keys, runners, webhooks).
- Lock down external access with proper network controls and zero-trust principles.
- Review and update access permissions regularly.
- Schedule periodic security drills and credential hygiene audits.
- Maintain a centralized record of changes and ensure documentation is up to date.
Verification and ongoing monitoring
Verification means validating that no default credentials remain and that all rotated credentials meet policy standards. Use automated checks in CI/CD pipelines to verify that credentials are not hard-coded or left in source control. Regularly review authentication logs for anomalies and tune alert thresholds. Run an annual audit against your GitLab configuration to confirm that all security controls—MFA, rotation cadence, and access reviews—are effective. The ongoing goal is to maintain a posture where default credentials are unlikely to be usable, even if a breach occurs.
Key takeaways for steady security improvements
- Treat every default credential as a potential breach point.
- Enforce immediate rotation and MFA for all admin accounts.
- Centralize credential management and reduce exposure in scripts and pipelines.
- Regularly audit, monitor, and update access controls.
- Reference official GitLab security docs and industry best practices for ongoing guidance.
Default credentials by GitLab deployment type
| Deployment Type | Default Admin Username | Default Admin Password | Notes |
|---|---|---|---|
| Omnibus GitLab | varies | varies | Refer to official docs for defaults; rotate on first login |
| Docker Image | varies | varies | Defaults may not persist; reset credentials on first run |
Your Questions Answered
What counts as a default username and password in GitLab?
Defaults vary by installation path (Omnibus, Docker, or source). Treat any credential introduced during setup as potentially default until it’s rotated. Always enforce a change on first login and apply a strong password policy.
Defaults vary by setup. Treat them as temporary and rotate them with MFA enabled.
Why are default credentials a risk for GitLab installations?
They provide attackers with a known credential set, enabling unauthorized access if not rotated. This risk is amplified for exposed deployments and weak access controls.
Default credentials are a common entry point; rotate and secure immediately.
How do I identify if my GitLab install still uses defaults?
Audit admin and service accounts, review installation scripts, and scan configs for hard-coded credentials. Check authentication and access logs for unusual activity.
Run an inventory and scan for any defaults; review logs for anomalies.
What steps should I take to secure after discovery of defaults?
Rotate credentials, enable MFA, update to latest GitLab version, and restrict admin access. Document changes and monitor for new credential exposures.
Rotate and lock down access; monitor for issues.
Is there a default username/password for GitLab's Docker image?
Docker images often require first-login setup; do not rely on static defaults. Always set unique credentials during or after deployment and rotate them.
Don’t rely on docker defaults—set fresh credentials.
Where can I find official guidance on defaults for GitLab?
Refer to GitLab security docs and trusted security frameworks (CISA, NIST) for best practices on credential hygiene and hardening. Always corroborate with your deployment’s documentation.
Check GitLab security docs and national security best practices.
“Default credentials are a common attack vector; always enforce unique credentials and rotate them on first login and after major changes.”
Key Takeaways
- Treat defaults as security debt and rotate immediately
- Enable MFA for all admin accounts
- Audit credentials and access regularly
- Consult official docs for deployment-specific defaults
- Automate credential hygiene in CI/CD