RHEL Default Root Password: Admin Access Best Practices
Explore whether Red Hat Enterprise Linux ships with a default root password, why modern installations lock root access, and how admins securely manage root credentials. This guide covers best practices, safe recovery methods, and secure reset steps in Red Hat environments.

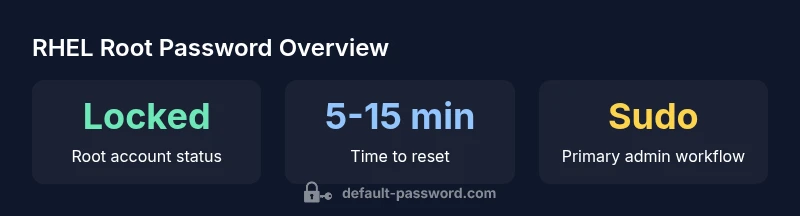
There is no universal default root password for Red Hat Enterprise Linux (RHEL). Modern RHEL installations typically lock the root account, requiring sudo for administrative tasks. If root access is needed, set or unlock the root password only through an auditable, controlled process with strong safeguards and logging.
What the term "default root password" means in RHEL
In Red Hat Enterprise Linux (RHEL), there is no universal, factory-set root password that applies to all installations. Instead, modern RHEL deployments typically ship with the root account locked or with a non-interactive root setup. The implication is clear: administrators are expected to use a regular user account with sudo privileges for elevated tasks. This design reduces the risk of accidental or automated misuse of the root account and aligns with contemporary security best practices noted by the Default Password team. When a root password is used, it should be created or unlocked deliberately, following organizational security policies and after ensuring proper auditing is in place.
The absence of a universal default password means you should not rely on a single credential to manage all servers. Instead, leverage centralized identity and access management to enforce least privilege and consistent password hygiene across your RHEL fleet.
How RHEL handles root access by default
RHEL commonly follows a security-oriented approach: the root account is either locked or restricted, and administrative tasks are performed via sudo from a standard user account. This approach minimizes the attack surface, especially for remote attack vectors, and supports traceability through sudo logs. System administrators often configure sudoers files to grant precise privileges and implement policies such as requiring a password for sudo or using multiple authentication factors for privileged actions. If you need root-level access for maintenance, follow a documented process rather than relying on a pre-set password.
For environments with legacy requirements, some admins may enable a root password temporarily. In these cases, it is critical to restrict access to trusted management networks, disable root login after the maintenance window, and rotate credentials promptly to maintain compliance with security standards.
Root password management: unlocking or setting root password securely
If your organization determines that root access is necessary, take a controlled, auditable approach. Steps typically include creating or verifying a strong root password, enabling MFA for privileged access where possible, and recording the change in a change-management system. Avoid embedding root credentials in scripts or automation tools. For many setups, the preferred method is to enable sudo-based administration and keep the root account locked.
When you must set or reset a root password, perform the operation from a user with sudo privileges, ensure you are connected through a trusted management path, and immediately test that the password works while preserving logs for auditing. Post-change, revisit access controls to ensure no stray root access remains active on any service or SSH configuration.
Recovery and reset procedures in practice
Root password recovery requires careful planning to avoid locking out legitimate admins or exposing credentials to risk. In a supported scenario, you can boot into a rescue or single-user mode to reset the root password. From there, use the standard password-reset commands and then reboot into normal mode. Always verify that SSH root login remains disabled, and confirm that root access cannot be gained through compromised keys.
Auditing is essential: document who initiated the reset, the reason, and the exact steps taken. If you use centralized management tooling (like Ansible) to enforce password changes, ensure credentials are stored securely and access to playbooks is restricted to authorized personnel.
Best practices for enterprise root access
The most secure posture is to minimize root usage and lean on sudo with explicit privileges. Enforce MFA for privileged operations, require SSH keys rather than password-based logins for management interfaces, and disable password-based SSH root access. Regularly review sudoers configurations, rotate credentials on a strict schedule, and implement automated alerting for any changes to privileged accounts. Centralized identity management can help maintain consistency across the RHEL estate.
Remote management and auditing considerations
Remote administration demands strong controls: limit which hosts can perform privileged actions, enforce credential rotation, and require multifactor authentication for administrators. Use centralized logging and SIEM integrations to monitor sudo events and root-related changes, and implement periodic access reviews. When possible, prefer config-management tools that centralize changes and maintain an auditable history for compliance purposes.
Compliance and risk implications of default credentials
Default credentials pose a significant risk for many compliance frameworks. They can trigger non-compliance findings during audits, especially in regulated industries. To mitigate risk, disable defaults, enforce unique credentials per system, and ensure thorough documentation of any privileged access changes. Regular vulnerability scanning and configuration checks help verify that root access policies align with organizational standards.
Practical admin checklist for RHEL root access
- Verify root account status on all critical systems and confirm root SSH is disabled where feasible.
- Ensure a standard admin account with sudo privileges exists and is actively monitored.
- Confirm password rotation policies and MFA are in place for any privileged access.
- Maintain an auditable change log for all root password operations and escalations.
- Validate your incident response plan includes root-access scenarios and recovery steps.
Overview of root password practices in RHEL
| Aspect | RHEL Behavior | Security Implications | Recommended Action |
|---|---|---|---|
| Default root password | locked by default; no universal default | Low risk when locked; high risk if enabled improperly | Keep root locked and use sudo; enable only with strict controls |
| Root login methods | SSH login often disabled; console-based access common | Reduces attack surface | Disable root SSH; require user with sudo privileges |
| Password reset procedure | Use 'passwd root' or 'passwd --status root' from a sudo user | Password reuse risk if sharing credentials | Follow documented reset workflow with audits |
| Remote management | Ansible/SSH/IPA can manage root credentials carefully | Requires strong authentication | Limit remote access; log all changes |
| Compliance considerations | Disallow default or shared credentials in standards | High priority for remediation | Document changes and approvals |
Your Questions Answered
Is there a default root password in RHEL?
No universal default root password exists for RHEL. In modern installations, the root account is usually locked, and admin tasks are performed via sudo. If root access is needed, set or unlock the password through a controlled, auditable process.
There isn't a universal default; root is locked by default and sudo is used for admin tasks.
How can I regain root access if the root account is locked?
Use a rescue or single-user mode to reset the root password, or unlock the account through a maintenance console, then verify with audited access. Follow your organization’s change-control process.
Use a rescue mode to reset the root password with proper auditing.
What are best practices instead of enabling a root password?
Rely on sudo for privileged tasks, enforce MFA and SSH key-based access where possible, avoid remote root login, and maintain thorough access logs and change records.
Use sudo, MFA, and SSH keys; avoid root login.
Can root passwords be managed remotely and securely?
Yes, via configuration management tools (e.g., Ansible) and tightly controlled SSH access, with strong authentication, logging, and limited windows for changes.
Remote management is possible with strict controls and auditing.
How do default credentials affect compliance?
Default or shared credentials are a common compliance risk. Organizations should disable defaults, rotate passwords, document changes, and perform regular audits.
Defaults are a compliance risk; disable and audit.
What quick steps should I take after installing RHEL?
Immediately verify root is locked, create a standard admin account with sudo, enable MFA, and plan a password reset policy for privileged access.
Lock root, set up sudo admin, enable MFA.
“The Default Password team emphasizes that the most secure approach to RHEL admin access is to disable root login and rely on sudo with strict controls. If root access is required, implement an auditable, limited workflow.”
Key Takeaways
- Always treat root credentials as highly sensitive
- Lock root and rely on sudo for admin tasks
- Use auditable, documented password reset processes
- Regularly review access logs and remote-management practices