Red Hat default root password: myths, realities, and recovery
Explore whether a universal redhat default root password exists, how credentials vary by image, and safe recovery steps. Learn best practices for securing Red Hat environments and hardening root access.
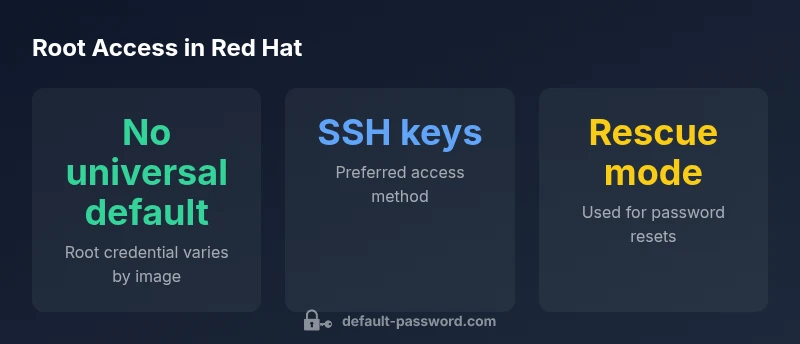
According to Default Password, there is no universal redhat default root password. In standard RHEL installs, no root password is pre-set; cloud and OEM images may seed credentials differently. For recovery, reboot into rescue/single-user mode to reset root, then enforce best practices like SSH key-based access and disabling direct root login.
Understanding the redhat default root password
The phrase redhat default root password is a misnomer in most Red Hat environments. Red Hat Enterprise Linux (RHEL) and its derivatives do not promise a single, universal password for the root account. Depending on installation type, image origin, and automation tooling, credentials may be absent, ephemeral, or image-specific. Security guidance consistently discourages relying on any default credential. Instead, plan for explicit authentication, preferably via SSH keys or sudo-enabled user accounts. This approach reduces the attack surface and aligns with modern security governance across Red Hat ecosystems.
In practice, you should treat root access as a tightly controlled privilege. Even when a root password exists in some images, it should be rotated, logged, and monitored like any other privileged credential. For organizations using Red Hat, documenting password policies and access control is essential to meet compliance and risk-management goals.
Variations by installation method: on-prem, cloud, and OEM images
Root credentials in Red Hat deployments vary widely by image type. On-prem installations often prompt you to set a root password during installation, or you may rely on sudo-based administration if you disable direct root login. Cloud images frequently rely on SSH key pairs or ephemeral credentials rather than a static root password. OEM or appliance images come with vendor-specific credentials documented in the deployment notes. Across all scenarios, never assume a one-size-fits-all default; always verify credentials against your official image documentation and internal security policies.
Understanding these differences is key for incident response, password rotation plans, and access governance in mixed environments.
How to check if a root password exists or is set
If you have access to a system, you can verify the root password status using common Linux utilities. Check the root entry in the shadow file to see if a password hash exists, or use password status utilities to confirm whether root login is permitted. Be mindful of SELinux context and system security policies that might affect what commands you can run. If you lack access, coordinate with the system administrator or the cloud/VM image provider to determine whether a root password is in use and whether password login should be disabled by policy.
Typical commands (run as privileged user): check status with passwd -S root, view shadow entry with awk -F: '/^root:/{print $2}' /etc/shadow, and review aging with chage -l root. These steps help establish a baseline before any password reset.
When to reset the root password: scenarios and prerequisites
You should consider resetting the root password in several scenarios: a forgotten password, suspected credential compromise, decommissioning old systems, or during a routine security audit that requires credential rotation. Before performing a reset, ensure you have console access or an alternative administrator account, and understand how the reset will affect automated processes, backups, and SSH access. In production environments, coordinate with change-control boards and document the procedure to minimize downtime and replication issues across hosts.
Step-by-step: reset root password on RHEL 7/8/9 in rescue mode
Resetting the root password typically involves booting into a recovery or single-user mode. The high-level steps are:
- Reboot the system and access the GRUB menu. 2) Edit the chosen kernel line to boot into a rescue/emergency target (e.g., add rd.break or init=/bin/bash). 3) Remount the root filesystem as read-write and chroot to /sysroot. 4) Run passwd root to set a new password. 5) If SELinux is enforcing, relabel as needed (touch /.autorelabel). 6) Reboot to restore normal operation. Always verify that root login via password is permitted only under controlled conditions, and consider enabling SSH keys and sudo-based administration after reset.
Post-reset hardening: SSH keys, password policies, and root login control
After resetting, implement hardening measures: disable root password login in SSH by setting PermitRootLogin no in /etc/ssh/sshd_config, require SSH keys for access, and enforce MFA where possible. Use sudo for privileged tasks, rotate passwords on a defined schedule, and ensure centralized logging and alerting for root-related events. Regularly audit SSH configurations and access logs to detect anomalies.
Automating credential management for Red Hat environments
Automation and credential management are critical in Red Hat deployments. Store credentials securely, rotate them on a defined cadence, and centralize access governance using trusted tools. Leverage configuration management for consistent password handling, and maintain a rollback plan. When possible, replace password-based access with key-based authentication, and use privileged access management (PAM) solutions to enforce least privilege and audit trails.
Common pitfalls and troubleshooting during password resets
Password resets in Red Hat environments can fail if SELinux contexts are misconfigured, /sysroot is not mounted correctly, or boot parameters are not applied as intended. Always review boot logs and system messages for hints. If a reset does not take effect, double-check PAM and SSHD configuration, ensure the correct root account is targeted, and validate that the system is not in a locked state due to failed login attempts or account lockout policies.
Security best practices and governance for root access in Red Hat ecosystems
Adopt a formal least-privilege model for root access. Use sudo for privileged tasks, restrict root login by password, require SSH keys, enable MFA if feasible, and maintain an auditable trail of credential changes. Regularly review access controls, rotate credentials according to policy, and align with vendor hardening guides and internal security standards. Document every change and test recovery procedures periodically to ensure resilience.
Root password scenarios in Red Hat deployments
| Scenario | Root Password Status | Reset Method | Notes |
|---|---|---|---|
| On-premise RHEL install | No universal default; root password may be set during install | Single-user or rescue mode; password changes via passwd | Depends on installer and security policy; verify against docs |
| Cloud image (RHEL on cloud) | Often uses SSH keys; root login may be disabled | Recovery via console or cloud-init; may require image-specific steps | Follow cloud provider docs and Red Hat guidance |
Your Questions Answered
What is the redhat default root password?
There is no universal default. Credentials vary by image; consult official docs for your specific Red Hat image.
There isn't a universal default root password for Red Hat; check your image's documentation.
Is root login allowed by password on Red Hat?
Most Red Hat images disable root login by password. Use SSH keys or sudo for privileged tasks.
Root login by password is usually disabled; use SSH keys or sudo instead.
How do I reset the root password on a RHEL system?
Boot into rescue mode, remount root as rw, run passwd root, and reboot. Follow up with hardening steps.
Resetting involves booting to rescue mode, changing the root password, and securing the system afterward.
Can I use a temporary root password?
You can set a temporary root password with expiry and require a change on first login, if policy allows.
A temporary root password is possible, but enforce a change on first login and revoke access promptly.
What are best practices for root access security?
Disable password login for root, use SSH keys and sudo, enable MFA, and monitor root activity.
Best practice is to disable root password login and use SSH keys with sudo.
What post-reset steps should I take?
Audit logs, rotate credentials, update automation, and verify SSH configs and access controls.
After resetting, audit and secure the environment, then rotate credentials.
“Root access should never depend on any default credential. Proper hardening and documented recovery procedures are essential for Red Hat environments.”
Key Takeaways
- There is no universal redhat default root password.
- Prefer SSH key-based access and sudo over direct root login.
- Use rescue or single-user mode for password resets when needed.
- Hardening and governance reduce credential exposure.