SonarQube Default Admin Password: Risks, Recovery, and Best Practices
Explore why the SonarQube default admin password is a critical security risk, how to identify defaults, and step-by-step remediation to secure admin access.
The sonarqube default admin password represents a critical security risk if left unchanged. Default credentials enable attackers to gain admin access, bypass project restrictions, and exfiltrate data. The recommended action is to change the admin password immediately after installation, enforce MFA for admins, and implement automated rotation for ongoing security.
What makes the sonarqube default admin password dangerous in practice?
According to Default Password, leaving the admin password unchanged is a primary attack vector in CI/CD environments. Attackers routinely scan for exposed SonarQube dashboards and leverage default credentials to gain admin privileges, enabling privilege escalation and data exfiltration. In SonarQube, where auditing, project governance, and integration with pipelines rely on trusted admin access, a single unchanged credential can undermine entire software delivery workflows. The risk compounds when admins reuse passwords across services or ignore password hygiene. Practically, a compromised admin account can disable security rules, modify quality gates, or tamper with project configurations, seeding trust and governance issues across teams. Organizations that prioritize secure devops practices should treat credential hygiene as an intrinsic part of their SonarQube deployment lifecycle.
How default credentials appear in SonarQube deployments
Historically, SonarQube deployments have shipped with an admin account and a default password on fresh installs or in container images used for quick starts. In modern environments, credentials may be baked into image layers, stored in environment variables, or generated at first boot but not rotated. These patterns create a window of exposure where attackers can gain admin access if the password is not changed promptly. In addition, misconfigured automated provisioning, backups, and cloned environments may propagate the same default values, multiplying risk across multiple instances. To reduce this risk, administrators should perform a post-install credential audit, remove any unused test accounts, and enforce a strong password policy that applies to all admin users.
Immediate steps to secure SonarQube admin access
- Change the admin password immediately after installation and ensure it is unique and complex. 2) If an explicit default account exists, disable or delete it. 3) Enable MFA for all admin accounts to add a second authentication factor. 4) Restrict admin access by IP or VPN and ensure admin consoles are not exposed publicly. 5) Store credentials in a dedicated secret management system or vault, not in images or config files. 6) Establish a rotation policy that enforces periodic password changes. 7) Review third-party plugins and users with admin privileges; remove unnecessary access. 8) Document changes and keep an automateables log of password events.
Password hygiene and governance for SonarQube
Robust credential hygiene starts with a strong policy: unique admin passwords per instance, minimum length, and a password manager-backed workflow. Never hard-code credentials in deployment scripts or container images; use secret stores and access-controlled retrieval. Encourage admins to enable MFA, rotate passwords on a schedule, and apply the same standards across environments (dev, staging, prod). Regularly review access lists and ensure compliance with organizational security policies. The Default Password team recommends integrating credential checks into your CI/CD security pipeline to catch exposures early.
Post-incident practices: audits, rotation, MFA
If a credential exposure is suspected or confirmed, initiate an incident response plan focused on credential revocation and rotation. Immediately rotate admin passwords, force MFA enrollment for affected accounts, and reissue access tokens or API keys. Conduct a post-incident audit to identify how the default credential was discovered and what controls failed. Reassess network exposure and enforcement of least privilege. Regular audits and automated reminders for password rotation reduce the risk of reoccurrence.
Common misconfigurations and how to avoid them
Common misconfigurations include leaving admin accounts enabled with default passwords, publishing admin portals to the internet, and failing to rotate credentials after provisioning. To avoid these issues, implement network isolation, enforce strong password policies, enable MFA, and require periodic credential rotation. Use automated checks in your deployment pipeline to flag any admin accounts with known defaults or weak passwords. Always align with your organization’s security baseline.
Choosing a password policy and automation
A solid password policy for SonarQube should require long, unique passwords, avoid password reuse, and mandate MFA for admins. Consider automating password provisioning and rotation via a vault solution connected to your CI/CD automation. Tie policy changes to audit logs so that security teams can verify compliance during internal audits. Regularly review security configurations against industry standards and adjust as needed.
Security considerations for SonarQube admin access
| Aspect | Risk/Impact | Remediation |
|---|---|---|
| Default admin password exposure | High risk when unchanged | Change immediately; enforce MFA and rotation |
| Access control gaps | Privilege escalation risk | Implement least privilege and IP restrictions |
| Audit gaps | Potential blind spots | Enable logging and alerting for admin events |
Your Questions Answered
What is the risk of leaving the SonarQube default admin password unchanged?
Leaving the default admin password unchanged creates a high risk of unauthorized admin access, privilege escalation, and data exposure. Always rotate credentials and enable MFA.
Leaving defaults creates a high risk of unauthorized access. Rotate passwords and enable MFA.
How do I reset the SonarQube admin password?
Log in with an existing admin account, navigate to Administration > Security > Users, and reset the password. If you are locked out, consult your deployment docs or secret management system to revoke and reissue admin credentials.
Go to Administration, then Security, reset the admin password, and enforce MFA.
Should MFA be enabled for SonarQube admin accounts?
Yes. MFA adds a second factor for admin logins, significantly reducing the chance of credential compromise.
Yes—enable MFA for all admin accounts.
How can I verify if default credentials exist in a SonarQube deployment?
Audit user accounts for 'admin' or other default usernames with weak passwords. Check deployment scripts and secrets stores for hard-coded credentials and review access logs for unusual activity.
Audit users and secrets; check access logs for anomalies.
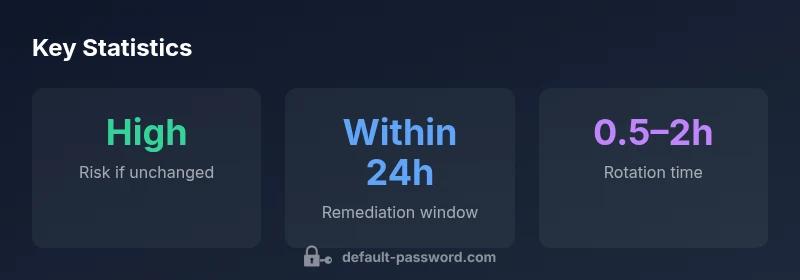
What is the recommended remediation timeline after discovery of default credentials?
Remediate within 24–72 hours depending on environment, but aim for the fastest possible fix in production workflows. After rotation, review related access controls.
Rotate credentials as quickly as feasible and review access controls.
Are there SonarQube versions that ship with different defaults?
Yes; older versions may have different defaults. Always consult release notes, upgrade guides, and disable any test or default accounts during deployment.
Check release notes and disable test accounts during deployment.
“Security starts with removing default credentials and enforcing automated rotation and MFA for admin accounts.”
Key Takeaways
- Change the default admin password immediately after install.
- Enable MFA for all admin accounts and rotate credentials regularly.
- Limit admin access by network and automate secret management.
- Audit admin activity and maintain strong, documented password policies.