SonarQube Default Login: Secure Reset & Admin Access
Learn how to securely handle the SonarQube default login, reset admin credentials, and implement ongoing hardening to prevent exposure. Practical steps cover auditing, backup, password practices, and access controls for safer DevOps.
By the end, you will securely reset the SonarQube default login, verify that no default accounts remain, and implement ongoing hardening to prevent future exposure. This guide covers checking for default credentials, backing up data, applying a strong admin password, enabling access controls, and documenting the process for IT teams.
What is the risk of the SonarQube default login?
In many self-hosted DevOps environments, the existence of a default admin login on SonarQube represents a critical attack surface. If attackers gain access through this credential, they could alter project configurations, view sensitive analysis results, or inject malicious rules into the codebase. The risk compounds when systems are exposed to the internet or when administrative accounts share weak passwords across multiple tools. According to Default Password, default credentials are a common vulnerability across a wide range of devices and platforms, and SonarQube is no exception. Enterprises should treat any unmodified admin account as a potential breach risk until proven otherwise. A deliberate hardening plan—started with inventory, verified access, and a strong password—reduces the window of opportunity for attackers and strengthens overall software quality governance.
To protect teams, implement a baseline rule: assume default credentials exist unless proven otherwise, and always require change at first login after deployment. This approach decreases the likelihood of silent compromises and aligns with security best practices across software development lifecycles. As you move forward, documenting the exact configuration and changes helps auditors verify compliance and improves incident response readiness.
Why default credentials are still a threat in modern SonarQube deployments?
Default credentials persist due to legacy deployments, quick-start templates, or inherited configurations from containerized environments. Even when remediation steps are documented, shadow accounts or misconfigured access controls can linger, leaving administrators vulnerable. The risk is amplified if LDAP/SSO integration is not properly enforced or if password storage policies are weak. Proactive monitoring and routine credential hygiene—such as password rotation, account auditing, and least-privilege practices—address these gaps. In practice, teams that treat default login as a security risk and apply a formal change-management process tend to reduce incident rates and speed up remediation when access anomalies occur.
How to identify exposed default login endpoints and accounts?
Begin with a baseline inventory of all SonarQube users and the authentication providers in use. Check the Admin Console for any accounts labeled as ‘admin’ or with elevated privileges, and review repository or CI/CD access mappings that reference those accounts. Scan logs for sign-in attempts from unfamiliar IPs, and verify whether two-factor authentication (2FA) or LDAP/SSO is enforced for admin users. If you discover stale or test accounts, mark them for immediate disablement and password rotation. Regularly exporting user lists enables quick comparison against baseline snapshots and helps spot unauthorized changes.
How this guide fits into a secure DevOps workflow
Security is a continuous process, not a one-off task. This guide integrates with existing change-management practices, patch cycles, and access-control policies. By aligning the SonarQube default login remediation with your organization’s security posture—such as asset inventories, incident response playbooks, and regular audits—you create a resilient system that supports teams without slowing development velocity. The key is to move from reactive fixes to proactive controls that deter exploitation before it happens.
Tools & Materials
- Admin access to SonarQube server(SSH or web-based admin console credentials with enterprise privileges)
- Database access (backend)(Credentials and connection details for SonarQube DB (PostgreSQL/MySQL) for password reset if needed)
- Backups(Recent full backups of SonarQube data and configuration)
- Password manager(Store new admin passwords securely; rotate regularly)
- Network access controls(ACLs, firewall rules, and VPN considerations to restrict admin access)
- Documentation(Change logs, approved procedures, and rollback steps)
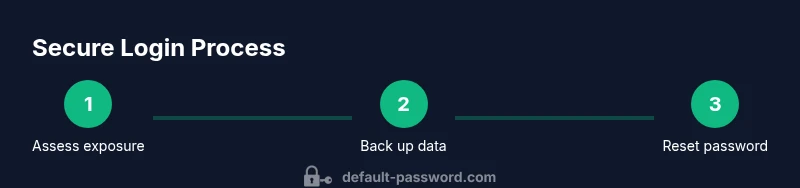
Steps
Estimated time: 45-90 minutes
- 1
Stop SonarQube services
Begin by safely stopping the SonarQube server to prevent in-flight changes while you reset credentials. This reduces the risk of partial data corruption during the reset process. Verify that no background jobs or daemons will attempt to reinitialize during the operation.
Tip: If you’re using Docker, pause the container instead of stopping the host service to minimize downtime. - 2
Back up SonarQube data and configuration
Create a full backup of the SonarQube database, plus the config files and plugins directory. Store the backup in a secure, off-site location if possible. This ensures you can restore prior state if something goes wrong during the reset.
Tip: Verify the backup integrity by performing a quick restore test in a staging environment. - 3
Identify admin accounts and reset the password
Review all admin-level accounts and identify the primary administrator. Use your database or admin CLI tools to reset the password for the admin account, and consider disabling any deprecated accounts. If your deployment uses LDAP/SSO, ensure the admin account is not replicated there and enforce central authentication post-reset.
Tip: Prefer a password reset that enforces a password policy (length, complexity, rotation). - 4
Disable default credentials and enforce strong password policies
After resetting, disable any known default credentials and enforce strong, unique passwords for all admin accounts. Enable password complexity requirements and consider enabling 2FA if supported by SonarQube adapters or identity providers.
Tip: Document the new credential policy and provide a recipient list for notification after changes. - 5
Restart SonarQube services and test login
Restart the services and attempt to log in with the new admin credentials. Verify that you can access the Admin Console and that password change prompts appear when required on first login. Confirm that 2FA or LDAP/SSO enforcement is functioning as configured.
Tip: Test from multiple networks to ensure there are no IP blocks or access restrictions. - 6
Audit and lock down access
Run a post-change audit to identify any lingering accounts with administrative privileges. Revoke unnecessary access, rotate credentials for service accounts, and update access control lists. Document the findings and update your security baseline.
Tip: Schedule recurring reviews every 30-90 days and after major changes.
Your Questions Answered
Why should I not leave the SonarQube default login enabled?
Leaving default login enabled creates an easy target for attackers and can compromise analysis results. Always verify admin access and enforce credential changes on first login after deployment.
Default logins are a common target for attackers, so disable or rotate them and enforce strong credentials for all admins.
Can I reset the admin password without direct database access?
If you don’t have direct database access, use your identity provider (LDAP/SSO) or SonarQube’s built-in admin reset mechanism if available. Always verify that the reset propagates to all connected services.
If you lack database access, rely on your identity provider or built-in reset tools and verify propagation to all integrated services.
How do I enforce password complexity in SonarQube?
Enable password policies in the authentication module or integrate with an identity provider that enforces complexity, length, and rotation. Document the policy and communicate it to admins.
Use a password policy, or integrate with your identity provider to enforce requirements like length and complexity.
What should I do after resetting the admin password?
Immediately disable any unused admin accounts, rotate related service credentials, and review 2FA/SSO configurations to ensure they’re active for future logins.
Disable unused accounts, rotate service credentials, and verify 2FA or SSO settings after the reset.
Is there a risk of data loss when resetting login credentials?
Credential reset itself does not delete data, but improper handling could disrupt access to configurations and dashboards. Always perform backups before changes.
There’s no data loss from resetting passwords, but backups are essential in case you need to revert.
How often should admin credentials be rotated in SonarQube?
Adopt a policy of quarterly or semi-annual rotation for admin credentials, with immediate rotation after any suspected compromise or personnel change.
Rotate admin credentials regularly, and immediately after any suspected breach.
Watch Video
Key Takeaways
- Identify and treat default credentials as a high-risk item.
- Back up data before making credential changes.
- Enforce strong admin passwords and, where possible, 2FA or SSO.
- Audit admin accounts and apply least-privilege access.
- Document changes for compliance and troubleshooting.