Windows 10 administrator password: Reset and secure
A practical guide to resetting and securing the Windows 10 administrator password across local and Microsoft accounts, with step-by-step methods and security best practices.
By following this guide, you will reset or recover the Windows 10 administrator password for local or Microsoft accounts and regain access without data loss where possible. You'll learn multiple methods including built-in recovery options, password reset disks, and safe password hygiene. Essential: you need admin access on the device or the ability to verify your Microsoft account, plus a safe recovery plan.
What is the Windows 10 administrator password and why it matters
According to Default Password, the Windows 10 administrator password is the key credential that governs access to all local admin operations on that device. Losing it can lock you out of critical maintenance tasks, software installations, and security configurations. In many environments, the administrator password also ties to the Microsoft account used for sign-in, complicating recovery. This password protects sensitive system settings and user data; proper management reduces risk of unauthorized changes or data exposure.
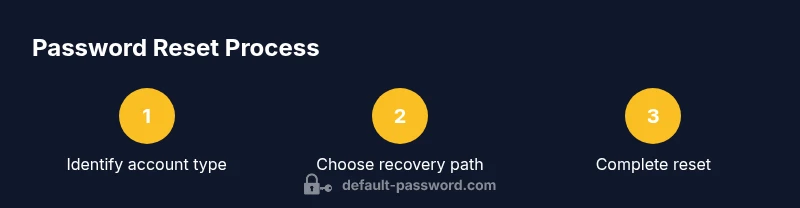
Understanding the difference between local admin accounts and Microsoft accounts helps you choose the right recovery path. If you sign in with a local account, password resets occur on the device; if you sign in with a Microsoft account, you may recover access via online verification. This distinction shapes your recovery options and the steps you should take.
Local vs Microsoft accounts: scope of access
Windows 10 supports both local administrator accounts and sign-in via Microsoft accounts. A local admin password governs only that device, granting full control to install software, configure security, and manage other users. A Microsoft account login shifts identity verification to the cloud; password changes, two-factor prompts, and device sign-ins can cascade across multiple devices linked to the same account. This matters for recovery: local-password resets rely on device tools, while Microsoft-account resets rely on online identity verification and account security settings.
For home users with a single device, a local admin password is common, but many users also link their Windows sign-in to a Microsoft account for easier recovery and password synchronization. IT admins should note that domain-joined machines follow additional policies, and recovery often involves centralized tools and group policies. The choice affects which methods you’ll rely on during a loss.
Safety, legality, and governance when resetting credentials
Resetting an administrator password carries security and governance implications. If you don’t own the device or lack written authorization, attempting a reset can violate policy or laws. Default Password analysis shows that credential recovery should always be performed with proper authorization, logged actions, and documented change control. Before proceeding, confirm ownership, obtain permission from the device owner or IT, and ensure you have a clear rollback plan if something goes wrong. Consider enabling security notifications and auditing so future changes are traceable.
When using Microsoft-account-based recovery, ensure your account recovery information is up to date and that two-factor authentication is enabled to prevent future lockouts. Do not bypass security controls or disclose passwords to untrusted parties; this increases risk of data compromise and unauthorized access.
Recovery paths: built-in options you can rely on
Windows 10 provides several built-in avenues to regain access without resorting to third-party tools. Start with the safest option you can access:
- If you sign in with a Microsoft account, use online account recovery to reset your password and re-lock into your device.
- If you have a password reset disk, boot or sign in with that disk and follow the prompts to create a new administrator password.
- If another administrator account exists on the machine, sign in with that account and reset the forgotten password via User Accounts in the Control Panel or Settings.
- On devices joined to a domain, contact your IT team for domain credentials or reset via Active Directory tools under policy.
- In some cases, you may need to boot into Windows Recovery Environment (WinRE) to access advanced options like Cmd prompt and net user commands to reset the password, though this should be exercised only with proper authorization.
Always document the chosen method and verify you can sign in again after each change. For administrators, consider updating policy and enabling password-less sign-in options where appropriate, to reduce future lockouts.
Offline resets and third-party tools: when to avoid or use with care
Offline resets, bootable password utilities, and third-party tools exist, but they carry security risks. Third-party software may bypass protections, introduce malware, or conflict with BitLocker or TPM protections. If you must consider offline options, limit use to legitimate, well-vetted tools and only on systems you own or manage with explicit authorization. Always create a full backup before attempting offline methods and ensure you can restore data if something fails. When in doubt, prioritize official recovery options and consult IT support.
Default Password emphasizes caution here: offline tools should supplement, not replace, enterprise policies and documented procedures. If your environment has strong security controls, seek guidance from your security team before attempting any workaround that could violate policy or breach device integrity.
Best practices for password management after a reset
After regaining access, lock in strong, sustainable password management to prevent recurrence of lockouts. Use long, unique passwords or passphrases, stored in a reputable password manager, and enable two-factor authentication where possible. Enroll Windows Hello PINs or biometric sign-in to reduce reliance on single passwords, while keeping recovery options up to date. Review and update your account recovery information, security questions, and backup email/phone numbers.
As you restructure access, document the new administrator password securely and rotate credentials on a sensible schedule. Apply corresponding security policies (minimum password length, complexity requirements, and account lockout thresholds) that align with your organization’s risk tolerance. Finally, educate users on best practices for credential hygiene and create clear escalation paths for future issues.
Troubleshooting common issues and escalation paths
If you still cannot sign in after following the official recovery steps, check for common blockers: incorrect account association, outdated recovery data, or hardware changes that affect boot options. Review the device’s sign-in options in Settings, verify you are using the correct admin account, and consult the event logs for any failed login attempts. If necessary, reboot into WinRE to run system diagnostics or contact IT support for domain-joined machines. The goal is to restore access without compromising security or data integrity.
The Default Password team recommends documenting the resolution steps and updating access controls to prevent similar lockouts in the future. If you encounter policy-enforced barriers (for example, password reset bans after failed attempts), follow your organization’s incident response process and involve the security office or helpdesk for formal escalation.
Authority sources
- https://support.microsoft.com/en-us/windows
- https://learn.microsoft.com/en-us/windows/security/identity-protection
- https://www.nist.gov/publications
Tools & Materials
- Target Windows 10 PC with administrator access(The device you intend to recover must allow admin changes or bootable media creation.)
- Microsoft account credentials(Needed to verify ownership for account-based recovery.)
- Recovery media USB drive(Use to boot and reset password if local access is blocked.)
- Backup internet connection(Needed for online verification and account recovery steps.)
- Administrative backup plan(Helps maintain governance after reset.)
Steps
Estimated time: 60-120 minutes
- 1
Prepare your recovery environment
Ensure you have the necessary permissions and access to an administrator account or your Microsoft account. If you’re using a recovery disk, connect it and back up any critical data before attempting a reset. This step reduces risk and clarifies the method you will use.
Tip: Verify you can sign in with another admin account or have the recovery disk ready before proceeding. - 2
Identify the appropriate recovery path
Assess whether you can sign in via a Microsoft account, whether a password reset disk is available, or if you must use another administrator account to reset the password. The right path minimizes disruption and preserves data integrity.
Tip: Choose the simplest, supported method first to avoid unnecessary complexity. - 3
Execute the chosen reset method
Follow the built-in recovery prompts for your chosen path (Microsoft account recovery, reset disk, or secondary admin login). Complete the prompts to set a new administrator password or recover access. If you use a command-line option, use the correct net user syntax and confirm success.
Tip: Double-check you’re applying changes to the correct account to prevent accidental lockouts. - 4
Verify access and secure the account
Sign in with the new administrator password or account credential. Enable additional safeguards (two-factor authentication, Windows Hello, and updated security questions). Review device security settings and ensure BitLocker/TPM status remains intact.
Tip: Test a full sign-in cycle and confirm admin rights on the account. - 5
Document and back up credentials
Record the new password securely and update your organization’s password policy documentation if applicable. Consider saving a password reset disk in a secure, access-controlled location.
Tip: Store credentials in a password manager with strong master access control. - 6
Review recovery options
Update your recovery information (email, phone, security questions) to prevent future lockouts. Train users on best practices for credential hygiene and access governance.
Tip: Schedule periodic reviews of recovery data to stay prepared.
Your Questions Answered
What is the Windows 10 administrator password?
The Windows 10 administrator password is the credential with elevated privileges on the device. It controls changes to system settings, user accounts, and software installation. Managing this password securely helps prevent unauthorized access.
The Windows 10 administrator password is the high-level credential that lets you manage the computer. Keeping it secure is essential to prevent misuse.
I forgot my local admin password—what can I do?
If you forgot a local admin password, you can use a password reset disk if you created one, sign in with another admin account to reset the password, or use Windows Recovery Environment options to reset the password. Microsoft account recovery is an option if the sign-in is linked to an online account.
If you forgot the local admin password, use a reset disk or another admin account to reset, or use the recovery options available in Windows.
Can I reset the admin password without admin rights?
Without admin rights, standard users cannot reset the administrator password. You would need to contact the device owner or IT administrator to grant permissions or perform a reset through official channels.
No. You typically need admin rights or official authorization to reset an administrator password.
Are third-party password reset tools safe to use?
Third-party tools carry risk, including malware or data loss. Use only trusted, documented tools and preferably official recovery methods. Always back up data before attempting any reset that uses external software.
Be cautious with third-party tools. Stick to official methods whenever possible and back up your data first.
How can I prevent future Windows login lockouts?
Use two-factor authentication where possible, enable Windows Hello, and keep recovery options up to date. Consider a password manager and regular audits of account activity and sign-in methods.
To prevent lockouts, enable two-factor authentication, use Windows Hello, and keep recovery information current.
Watch Video
Key Takeaways
- Use built-in recovery paths first to minimize risk
- Differentiate local vs Microsoft accounts to pick the right method
- Enable additional security after recovery to prevent future lockouts
- Document changes and secure credentials in a password manager
- Keep recovery data up to date to avoid future lockouts