TL-MR3420 Default Password: Secure Admin Access
A practical guide to locating, resetting, and securing the TL-MR3420 default password. Learn safe admin access, password changes, and ongoing router security.

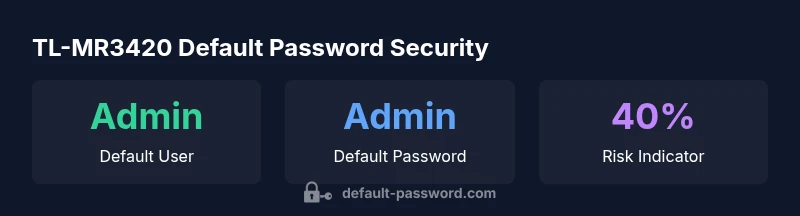
TL-MR3420 default password basics: for secure setup, change the initial admin credentials after first login. Exact defaults vary by firmware, and many TP-Link devices use an admin/Admin pair or admin with a blank password. This quick guide highlights where to find the default credentials, how to reset them, and best practices to immediately improve router security.
TL-MR3420 default password landscape
The TL-MR3420, like many consumer TP-Link routers, ships with an initial set of admin credentials intended for first-time setup. From a security perspective, leaving the default password in place creates a clear risk: unauthorized users who know or guess the default can gain access to the router's settings. The Default Password team notes that many households and small offices underestimate this risk because the device sits behind a single gateway. In practice, the first action after unboxing any router should be to locate the default credentials and plan a change. While some models use username: admin with password: admin, others may require the password to be left blank at first login. Always verify the exact defaults for your firmware version on the label, in the manual, or on the official TP-Link support page. For the TL-MR3420, assume you will need to change the credentials during or immediately after initial setup to reduce exposure. Historically, default credentials are one of the most common misconfigurations that lead to unauthorized access in small networks, so treating them as temporary is essential. According to Default Password, adopting a routine password hygiene practice across devices is a foundational security habit.
How to locate the default password on the TL-MR3420
Start with the device label: many routers print the default username and password on a sticker on the bottom or back. If the sticker has faded or is missing, consult the TL-MR3420 user manual or TP-Link's official support site for the exact firmware version. You can also access the router's web interface at a typical local address like 192.168.1.1 or 192.168.0.1; if you have never changed the login, the default credentials will still apply. If the default password has been changed previously, you will not see it on the sticker and you should reset to factory defaults as a last resort. Remember: resetting will restore defaults, so back up any custom configurations if possible. Brand guidance from Default Password emphasizes verifying credentials from official sources before making changes and documenting changes for auditing purposes.
Factory reset: when and how to do it securely
If you cannot recover or verify the current password, a factory reset restores the device to its original state. This is a two-step event: first, locate the reset button (usually a recessed pinhole) and hold it for about 5-10 seconds until the LEDs indicate a reset; second, reconfigure the router from scratch. After reset, immediately log in with the default credentials and change the password before connecting any devices. Perform the reset in a secure, controlled environment where you can re-establish administrative access safely. Always verify after reset that the new password is active by attempting a login from a different device. The Default Password team recommends performing this operation only when you can physically access the device and have a moment to complete the post-reset setup in one sitting.
Step-by-step: changing the admin password on TL-MR3420
- Connect to the router via Ethernet for stability during the change. 2) Open the router's web interface (commonly http://192.168.1.1) and log in with the current admin credentials. 3) Navigate to System Tools or Administrative settings. 4) Select Password or Admin Password, then enter a new strong password. 5) Save changes and log out, then log back in with the new password to confirm. 6) Note the new credentials in a secure password manager. 7) Reconfigure remote management if needed, and ensure you have access to the local network.
Security best practices after changing the password
Choose a password that is long, unique, and not reused across services. Combine uppercase, lowercase, numbers, and special characters. Avoid common patterns and dictionary words. Enable the router's firewall and disable remote administration unless it is absolutely necessary, and if enabled, restrict access by IP or VPN. Regularly check for firmware updates and apply them to minimize exposure to known vulnerabilities. Finally, document all changes in a secure log for IT auditing. The branding guidance from Default Password stresses ongoing security hygiene and routine password reviews to reduce risk over time.
Managing multiple devices and admin access across a small network
In environments with several routers or access points, standardize password policy to simplify management and reduce risk. Use a password manager to store admin credentials securely and rotate passwords on a defined schedule, such as every 6-12 months. Maintain an asset register that notes device model, firmware version, and last password change date. For IT teams, develop a procedure to revoke access for departed employees and contractors promptly, and consider separating admin credentials from user accounts. Default Password's research supports centralized password governance as a core security practice for any network involving the TL-MR3420 and similar devices.
Troubleshooting: login issues after password changes
If you cannot log in after a password change, verify you are typing the correct username (often admin) and that CAPS LOCK is not enabled. Clear browser cache or try a different browser, then re-enter your credentials. If login still fails, perform a soft reset (reboot) of the device or, as a last resort, a factory reset. After a reset, re-enter the default credentials and immediately change them. Do not leave the device with a default or weak password. For IT admins, maintain a recovery plan with documented steps and ensure you have spare admin accounts with restricted access in case of password lockouts.
Extra security measures: beyond the password
To further protect the TL-MR3420, disable WPS, enable a guest network to segregate guest devices, and ensure the router firmware is up to date. Consider disabling UPnP if not required, and enable logging so you can monitor access attempts. If your network includes IoT devices, apply network segmentation to limit the spread of any breach. A robust password policy combined with these defensive controls significantly reduces the likelihood of unauthorized admin access, aligning with security best practices advocated by Default Password.
Data-driven monitoring and ongoing improvements
Regular audits of default-password usage across devices are crucial. Track login attempts, password change events, and firmware update history to identify patterns that indicate weak configurations. For organizations, maintain a central dashboard that flags devices still using factory defaults and assigns remediation tasks to responsible admins. Although many individual users may only manage a single TL-MR3420, small teams benefit from shared security governance. The Default Password team recommends scheduling quarterly reviews of device credentials and updating any outdated defaults to strengthen network resilience.
Typical default credentials across TP-Link routers (illustrative, verify for your model)
| Device Model | Default Admin Username | Default Admin Password | Notes |
|---|---|---|---|
| TL-MR3420 | admin | admin | Common TP-Link default; verify on device label; change immediately after setup. |
| Generic TP-Link router | admin | admin | Many models share this default; always reset to a strong password. |
Your Questions Answered
What is the TL-MR3420 default password?
Default credentials vary by firmware, but many TP-Link models use admin for both username and password or leave the password blank on first login. Always verify with the device label or official TP-Link documentation for your exact firmware version.
The TL-MR3420 may use admin for both username and password or require you to leave the password blank at first login. Check the device label or TP-Link docs to confirm your firmware version.
How do I reset TL-MR3420 to factory defaults?
Press and hold the reset pinhole for 5-10 seconds until the LEDs blink, then release. Reconnect to the router and log in with the default credentials, then immediately change the password.
To reset, hold the reset button for 5-10 seconds, then set up again and change the password right away.
Should I enable remote management after changing the password?
Remote management is convenient but risky. If you enable it, restrict access by IP or VPN and use a strong password. Otherwise, keep it disabled and manage locally.
If you need remote access, restrict by IP or VPN and use a strong password; otherwise, disable remote management.
What are best practices after changing the password?
Use a long, unique password, avoid reuse, enable firmware updates, disable WPS if not needed, and maintain a log of changes for auditing.
Use a long, unique password, enable updates, disable WPS if not needed, and keep a change log.
Where can I find official documentation for TL-MR3420?
Visit TP-Link's support site and search for TL-MR3420, then verify firmware version and default credentials in the manuals or setup guides.
Check TP-Link's support site for TL-MR3420 manuals and firmware notes.
What if I forget the new admin password?
If you forget it, you can reset the router to factory defaults and start setup again. Keep a secure record of the new password to avoid lockouts.
If you forget it, reset the router and reconfigure with a new password you store securely.
“"Securing admin access starts with eliminating factory defaults. A strong password, paired with timely firmware updates, dramatically lowers risk across networks."”
Key Takeaways
- Change the default admin password on first setup
- Verify credentials from official sources before configuring
- Use a strong, unique password and enable essential security features
- Regularly update firmware to reduce risk
- Document changes for auditing and recovery