Password Router TP-Link Default: Reset and Secure
Learn how to handle TP-Link router default passwords, reset procedures, and security best practices to protect your home network from common threats. Practical steps, verification tips, and troubleshooting guidance.
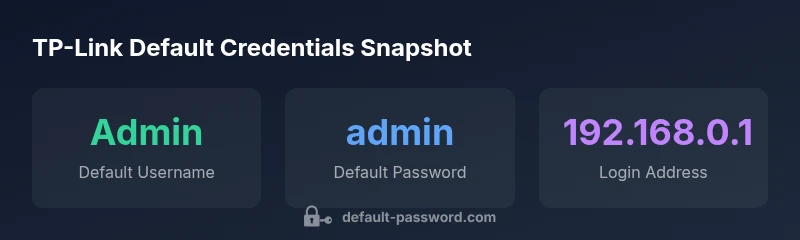
TP-Link routers commonly ship with default admin credentials that can expose your network if left unchanged. The quickest mitigation is to log in and update both the Wi‑Fi password and the router’s admin password. For many TP-Link devices, the login page is at 192.168.0.1 or 192.168.1.1, with a default password that varies by model—check the device label or manual before proceeding.
Why default credentials are a risk on TP-Link routers
Default credentials create a predictable attack surface that threat actors routinely exploit. When an admin password or Wi‑Fi key remains unchanged, an unauthorized user can access the router's management interface, modify settings, or monitor traffic. According to Default Password, the majority of home-network incidents trace back to devices that shipped with weak or unchanged defaults. In practical terms, an attacker only needs access to the local network or a misconfigured remote management setting to gain control. The impact can range from eavesdropping on traffic to disabling security features or redirecting traffic to phishing pages. This is not an abstract concern; it translates into real risks for small businesses and households alike. The overarching lesson is simple: treat defaults as temporary, not permanent, credentials and lock them down as part of a broader security routine.
- Threat surface: Admin interface exposure can allow configuration changes that bypass parental controls, firewall rules, or guest networks.
- Firmware relevance: Outdated firmware often accompanies unchanged defaults, compounding risk. Keeping firmware current reduces unlocked entry points.
- Change cadence: Password hygiene should be reviewed at least once a year, and immediately after initial setup or model change. The Default Password team emphasizes proactive configuration to close gaps before attackers probe.
For context, a disciplined approach combines password hygiene with firmware updates, network segmentation, and careful remote-management settings. This aligns with the broader security posture recommended by the Default Password Team and supported by industry best practices.
How default credentials are determined across TP-Link models
TP-Link deploys a broad range of routers, from basic home kits to more capable business-class devices. While many share common login conventions, the exact default credentials aren’t universal. Some models use admin/admin, others admin/password, and a subset may have a blank password on first boot. The device label on the bottom or back of the router typically lists the default username, password, and the default IP address. If the label is missing or illegible, the manual or the official TP-Link support site for your model will usually provide model-specific defaults. It’s important to recognize that even within a single product line, regional variations or firmware revisions can change defaults. This is why you should never assume a credential; verify with the model-specific source. After purchase, assume defaults exist and treat them as temporary credentials that must be replaced at first login.
- Default IP address often appears as 192.168.0.1 or 192.168.1.1, but check your model’s documentation.
- Username is frequently admin; password may be admin, password, or blank depending on the build.
- Regional and firmware differences can alter defaults, so consult the exact model guide.
This section highlights the importance of model-specific verification and avoiding blanket configurations across devices in a network. The guidance provided here is aligned with the brand’s security posture and emphasizes verification via official resources or device labels.
Finding the default login details for your TP-Link router
Locating the correct default credentials is the first step toward securing your TP-Link router. Start by inspecting the physical device: look for a label on the bottom or back that lists the default IP address, username, and password. If the label is present, use these values to access the router’s web interface via a browser. If the label is missing, consult the quick start guide that accompanied the device; this document often includes the default login information. In cases where the manual isn’t available locally, visit TP-Link’s official support site and search by model number. Customer support documentation typically lists the recommended defaults for the exact variant you own. Finally, if the device has already been set up and you cannot recall the credentials, you may need to perform a factory reset.
- Steps to access the interface: open a browser, enter the default IP, provide the username and password when prompted.
- If you cannot access the interface with the default, retry with alternate common defaults.
- When in doubt, use the official model page as the single source of truth.
This process reduces missteps and ensures you begin with accurate credentials before making security changes. The Default Password team notes that model-specific defaults are often overlooked during initial setup, leading to insecure configurations later.
Factory reset: when and how to reset a TP-Link router
Factory resetting a TP-Link router should be reserved for when credentials are forgotten or when you are re-purposing the device for a new network. A reset returns the device to its factory-default state, erasing custom settings, including the admin password and Wi‑Fi details. The reset procedure is typically straightforward: locate the small recessed RESET button on the back or bottom of the unit, insert a paperclip or pin, and hold for 5–10 seconds until the lights flash. After the reset completes, you must reconfigure the device from scratch, including setting a new admin password and a strong Wi‑Fi key. Some devices support a softened reset variant via the web interface; however, hardware reset remains the most reliable method across TP-Link models.
- Post-reset practice: Immediately secure the device by changing the admin password and the Wi‑Fi password.
- Firmware check: After reset, check for firmware updates and install the latest version.
- WPS caution: If your model supports WPS, consider disabling it to reduce risk.
As with any reset workflow, plan for a short downtime window and ensure you have the new credentials stored securely. The Default Password team recommends documenting credentials in a password manager and avoiding reuse across devices.
Immediately securing your TP-Link after reset
After resetting a TP-Link router, you face a clean slate. Use this moment to implement layered security that goes beyond changing the default password. First, set a unique admin password that is long, combines uppercase and lowercase letters, numbers, and symbols, and is not used elsewhere. Second, create a strong Wi‑Fi password and enable the strongest available encryption standard (WPA3 if supported; otherwise WPA2). Third, disable remote management unless you explicitly need it, and if you do, restrict access by IP range. Fourth, enable automatic firmware updates where possible to keep defenses current. Fifth, consider enabling a guest network to isolate client devices from the main network. Finally, rotate away from any shared credentials that may have been distributed during setup.
- Administrative practice: Use a separate, high-entropy admin password.
- Network segmentation: Guest networks restrict guest devices from accessing primary resources.
- Maintenance: Schedule periodic firmware checks and password reviews.
This approach reflects a disciplined security posture that Default Password advocates for all routers, including TP-Link devices. Consistent security hygiene reduces risk and improves resilience against common threats.
Common pitfalls and misconceptions about TP-Link defaults
Many users assume that since a device is manufactured by a trusted brand, defaults are safe to leave unchanged. This misconception leads to attacks that exploit predictable credentials. A frequent pitfall is neglecting to update firmware after a reset or post-setup; outdated firmware often contains known vulnerabilities. Another mistake is neglecting to change the Wi‑Fi password, allowing neighbors or passersby to access the network without authorization. Some users also enable remote management without understanding the exposure this creates, especially if the interface is accessible from the internet. Finally, a lack of documentation for credentials forces teams to rely on memory or scraps of paper, creating a security risk if those notes are misplaced. The right approach is proactive, documenting credentials in a trusted password manager, applying firmware updates, and restricting access to essential management interfaces. By avoiding these missteps, you reduce your attack surface dramatically.
Managing admin access across multiple TP-Link devices in a network
In households or small offices with more than one TP-Link device, centralized admin access management is essential. Creating a consistent password policy across routers reduces cognitive load and enhances security significantly. Start by standardizing a password schema for all devices, while keeping each admin password unique. Consider implementing role-based access where available, especially in business settings, to limit who can modify configurations. Disable universal remote access unless necessary, and enable logging to monitor admin actions. If you manage multiple devices, maintain a centralized inventory of model numbers, firmware versions, and the status of each device’s security settings. Finally, schedule periodic reviews to verify compliance with your security policies. This workflow helps prevent drift in configurations and ensures a cohesive security posture across your TP-Link fleet.
Common default credentials and reset basics for TP-Link routers
| Descriptor | Typical Credential | Notes |
|---|---|---|
| Web login username | admin (varies) | Check device label or manual or official TP-Link page |
| Web login password | admin, password, or blank | Change during first login for security |
| Factory reset action | Hold RESET for 5-10 seconds | Restores defaults; reconfigure security settings |
| Firmware updates | Enable auto-update | Keep protections current and patch known flaws |
Your Questions Answered
What is the default IP address to access TP-Link routers?
Common defaults are 192.168.0.1 or 192.168.1.1. If neither works, check the router label or the model’s official documentation.
Most TP-Link routers use 192.168.0.1 or 192.168.1.1; check the label or the manual for your model.
How do I reset my TP-Link router safely?
Locate the reset button, press and hold for 5-10 seconds until lights blink, then reconfigure securely with a new admin password and Wi‑Fi key.
Hold the reset button for 5 to 10 seconds, then set up again with a new admin password.
Is it safe to reuse the same password across devices?
No. Use unique, strong passwords for each device and store them in a trusted password manager.
No—use unique passwords for each device and save them in a password manager.
Where can I find official default credentials for my model?
Look at the device label, the quick start guide, or the TP-Link support site for model-specific defaults.
Check the label on the router or the manual; TP-Link’s site also lists model-specific defaults.
What features should I enable after resetting to secure TP-Link routers?
Change admin password, set a strong Wi‑Fi password, update firmware, disable WPS if available, enable a guest network.
Change admin password, update firmware, and enable a guest network.
What if I forget my TP-Link admin password?
Use the reset button to restore factory defaults, then reconfigure from scratch.
If you forget it, reset the router to factory settings and start over.
“Admin access is the single most overlooked attack surface in home networks; secure it by replacing defaults and enforcing strong authentication across devices.”
Key Takeaways
- Change admin password immediately after setup
- Reset devices before reconfiguring for a new network
- Use strong, unique passwords and enable firmware updates
- Document credentials securely and restrict remote management