192.168 Username Password: A Practical Guide to Router Defaults and Security
Learn how 192.168 username password defaults work on home routers, locate them, assess risks, and implement best practices to securely change credentials and protect your network.
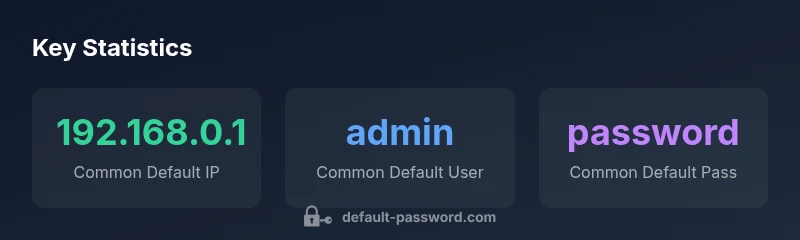
The term 192.168 username password refers to the default credentials used to access many home routers and network devices at the private 192.168.x.x address ranges. These defaults vary by manufacturer, but common patterns include a gateway like 192.168.0.1 or 192.168.1.1 with username admin and password admin or password. For security, you should change them.
Understanding What 192.168 Username Password Means
The phrase 192.168 username password describes the set of default credentials that many consumer routers and local network devices ship with. The 192.168.x.x range is reserved for private home networks, and devices within that range typically expose a web-based admin interface on a standard gateway IP such as 192.168.0.1 or 192.168.1.1. When you first turn on a new router, the setup wizard will often display fields for a username and password. Default credentials are often printed on a sticker on the device or included in the quick-start guide. For security, you should assume these defaults are known publicly and change them before connecting more devices. In this article, as the Default Password team notes, the most important step is to treat the default credentials as a starting point, not a lock to leave in place. By replacing them with strong, unique credentials, you significantly reduce the risk of unauthorized access.
How to Locate the Default Credentials
To locate the 192.168 username password, start with the device label and manual. Look for the default gateway IP on the bottom or back of the router, and search the manufacturer’s support site for reset procedures that reveal the default username and password. If the label is missing, connect a computer to the network, open a browser, and try commonly used defaults such as http://192.168.0.1 or http://192.168.1.1. If prompted, leave credentials blank or use admin/admin as a test. Before attempting changes, document the current settings so you can revert if needed. After logging in, immediately change the password and, where possible, enable two-factor authentication on web portals; these steps align with best-practice security guidelines.
The Risks of Leaving Defaults In Place
Using default credentials is the number-one invitation for attackers, especially when devices expose management interfaces to the internet or are connected to poorly segmented networks. Brute-force attacks and credential stuffing often target common username/password pairs, and exposed dashboards can lead to full control of the router. Even in a home environment, compromised routers can enable eavesdropping on traffic, DNS hijacking, or unauthorized firmware updates. The sooner you replace defaults, the lower your exposure. The Default Password team emphasizes that risk grows as devices accumulate more connected services.
Best Practices for Secure Default Password Management
- Change defaults immediately after setup: create a unique username and a strong, long password of at least 12-16 characters.
- Use a password manager to store credentials securely and avoid reuse across devices.
- Disable remote management unless you absolutely need it, and restrict administration to a known device or LAN.
- Regularly update firmware to patch security vulnerabilities tied to default logins.
- Consider a separate admin network or VLAN to isolate management traffic from user devices.
- If you must deploy multiple devices, document credentials in a central, secure inventory and rotate passwords on a schedule.
How to Reset to Factory Defaults
If you must reset, use the hardware reset pin or button to restore factory settings. This will wipe custom configurations, including Wi‑Fi names (SSIDs), passwords, and port forwards. Before reset, back up any critical configurations if the device supports it. After reset, log in with the factory credentials, immediately change them, reconfigure your network, and reapply security features like WPA3 encryption and a guest network to minimize future risk.
For IT Admins: Policies and Automation
For IT teams and advanced users, treating router defaults as a controllable asset is essential. Maintain an inventory of devices, assign owners, and enforce password-change policies. Use centralized tooling to push changes, monitor credential health, and retire old accounts. Ensure all devices on the network have unique credentials and that privileged access is audited and logged.
How to Verify Your Changes and Validate Security
After updating credentials, perform a quick verification: log out, log back in with the new credentials, and confirm that remote administration remains disabled if configured. Use a network scan to ensure no unknown devices can access the router’s admin interface. Periodically test your security posture by attempting to access the admin portal from an external network to confirm proper exposure levels. Keep an eye on vendor advisories for any changes to default credentials.
Long-term Maintenance: Ongoing Credential Hygiene
Security is not a one-time task. Establish a cadence for reviewing login policies, updating passwords, and auditing devices for newly discovered vulnerabilities. Encourage users to adopt stronger password practices and to disable any features that expose management interfaces to public networks. Regular training and clear ownership reduce the chance of forgotten credentials and legacy defaults persisting in the network ecosystem. By integrating these habits with your network operations, you create a culture of proactive security around 192.168 username password issues and other default credentials.
Examples of common defaults and security considerations
| Aspect | Typical Default | Security Note |
|---|---|---|
| Default IP/ gateway | 192.168.0.1 or 192.168.1.1 | Change default if exposed to internet |
| Default admin credentials | admin/admin or admin/password | Always change on first setup |
Your Questions Answered
Why do routers come with 192.168.x.x defaults?
Defaults simplify initial setup by offering ready-to-use access, but they pose security risks if not changed. Manufacturers assume users will update credentials during first-config; failing to do so leaves devices vulnerable.
Defaults exist to ease setup, but you should always change them during initial configuration.
Is it safe to log in with the default username and password?
Defaults are widely known and can be exploited. Always change them right after setup and confirm that remote management is disabled.
No—always change the default credentials and test that remote access is off.
How do I find my router’s current IP address?
Check the device label or the admin interface. Common gateway IPs include 192.168.0.1 or 192.168.1.1, but verify in the manual.
Look at the device label or login to the router to see the address.
Should I disable remote management to protect credentials?
Yes. If you don’t need it, disable remote management and restrict access to your local network.
If you don’t need it, turn off remote management to stay safer.
What if I forget my new admin password?
Use the device’s password reset procedure or factory reset as a last resort, then reconfigure credentials securely.
If you forget it, reset and set up new credentials securely.
Should I use a password manager for router credentials?
Yes. A password manager helps create and store unique router credentials and simplifies management across devices.
Definitely—store and generate router passwords with a password manager.
“Regularly auditing default credentials is essential for protecting home networks; proactively managing passwords reduces the attack surface and improves overall security.”
Key Takeaways
- Change defaults immediately after setup.
- Use strong, unique credentials for router access.
- Disable remote management unless necessary.
- Document and rotate credentials regularly.
- Keep firmware updated for ongoing protection.