Default Username and Password: A Practical Guide to Security
Learn why default username and password are risky, how to identify them on devices, and step by step methods to reset and secure them across routers, printers, cameras, and admin interfaces.
A default username and password are preconfigured credentials used by devices or services out of the box; they enable initial access and setup, but must be changed immediately to prevent unauthorized use.
What qualifies as default credentials and where to find them
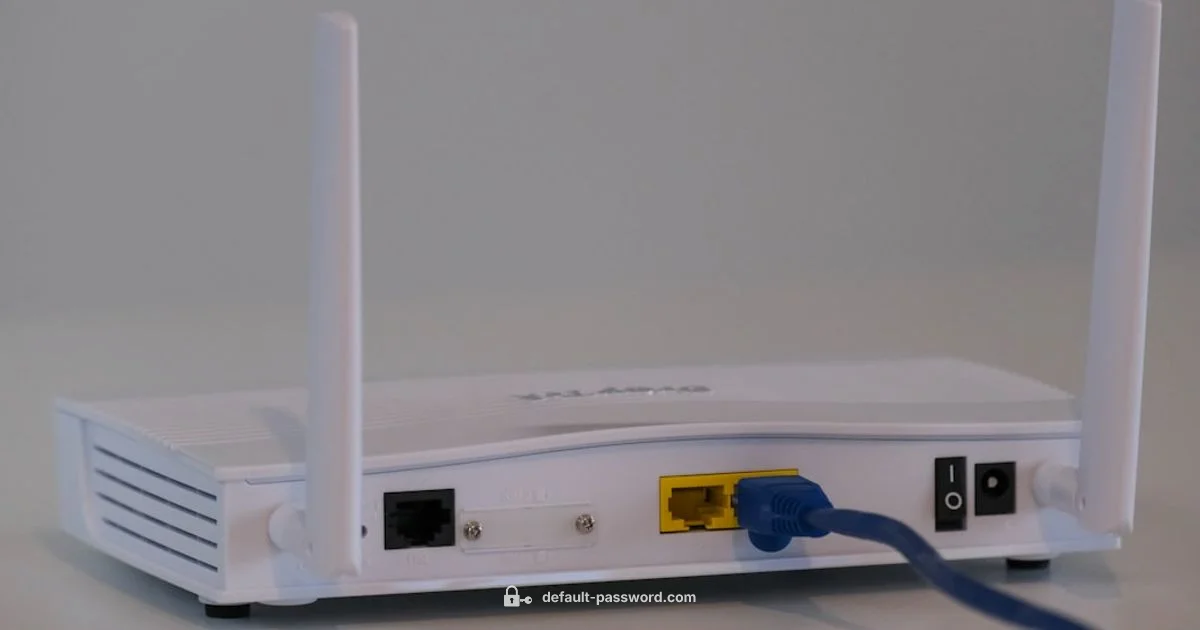
Default credentials are the preconfigured login details that manufacturers ship with routers, printers, cameras, IoT devices, and many software applications. A typical scenario is a username such as admin combined with a password like admin or password. You’ll often find these credentials on the device label, in the quick start guide, on the packaging, or within the initial setup screens of the device or software. For IT teams, inventory records may note default credentials for onboarding new devices. For home users, the manufacturer’s website or the box usually lists the defaults. No matter where you discover them, treat these values as temporary placeholders that must be replaced during the first setup. The goal is to depart from defaults as soon as possible to reduce exposure to attackers who scan for common defaults.
Why default credentials are risky and what attackers do with them
Default credentials are a well known attack surface. If left unchanged, an attacker who scans a network or device can gain easy access, potentially compromising data, launching lateral movement, or taking control of devices. Even on home networks, insecure defaults can enable malware propagation or unauthorized administration of connected devices. The Default Password team emphasizes that defaults are intended only for initial configuration and must be replaced with strong, unique credentials. When a device accepts a default login, it often also uses predictable settings that compound risk, such as remote admin enabled or exposed ports. Security practices recommend disabling remote access, enforcing strong passwords, and implementing MFA wherever possible to mitigate these risks.
Common places where default credentials exist and how to spot them
Defaults aren’t limited to routers. They appear on printers, network attached storage, cameras, smart hubs, and many enterprise applications. Look for labels on the device’s bottom or back, check the quick start card, or inspect vendor documentation for the exact default combinations. Cloud services and dashboards may also ship with initial credentials; always verify onboarding emails or setup wizards for any prompts to change them. Keeping a device inventory and regularly auditing for unchanged defaults helps prevent silent exposure across equipment and services.
How to identify default credentials on devices and services you own
Begin with the physical inspection: search for a label or sticker on the device that lists a username and password. Next, consult the user manual or official support site for the exact defaults. If a device has already been set up, log in with the current administrator credentials and search for a credentials or security section to see if a prompt exists to change them. For software and cloud services, review the account or security settings to confirm whether a default credential is still active or if a recommended change is pending. Document your findings in a centralized inventory to prevent duplications and ensure timely updates.
Step by step: how to reset and change defaults during initial setup
- Prepare a strong, unique credential strategy — create a passphrase or a password with length, complexity, and uniqueness. 2) Connect to the device’s admin interface via a browser or official app. 3) Locate the credentials section, and change both the username (if supported) and the password. 4) If possible, disable remote administration and enable two factor authentication. 5) Save changes and reboot if required. 6) Re-test login with the new credentials and update any saved configurations or backup systems accordingly.
Best practices for securing default credentials across devices
Avoid reusing simple values like admin or password. Use a unique username per device when supported, and a long, complex password or passphrase. Implement password managers to store credentials securely and enable two factor authentication where supported. Regularly rotate credentials on critical devices and disable factory defaults such as guest accounts. Establish a policy that new devices must pass a security audit before being allowed on the network.
Managing credentials across multiple devices and environments
For administratively managed environments, maintain a centralized inventory of credentials, device types, and last rotation dates. Use a password manager with auditing features to track access, and apply automated reminders for credential rotation. Document changes and ensure that backup access methods are secure and tested. In smaller networks, create a standardized hardening checklist for vendors, routers, printers, and cameras to ensure defaults are replaced consistently across devices.
Special considerations for enterprise IT and small networks
Enterprises should implement baseline security configurations and automated provisioning that assigns unique credentials during device enrollment. For small networks, manual checks paired with simple policy controls can close gaps quickly. Consider enabling MFA for critical admin interfaces and restricting management access to trusted IP ranges. Batch decommissioning of devices with outdated firmware and default credentials reduces legacy risk and simplifies ongoing security management.
Verification and ongoing security checks to maintain secure defaults
Schedule periodic audits to verify that defaults are not active on any device. Use vulnerability management tools to detect credentials stored in plaintext or devices with default accounts enabled. Run routine configuration reviews after firmware updates, redeployments, or network changes. The aim is a living security posture where defaults are promptly replaced and monitored, not a one time fix. A consistent review cadence helps catch drift, misconfigurations, and new devices with inherited defaults.
Real world scenarios and a practical checklist you can use
By walking through typical deployment scenarios, you learn to apply defaults securely. Create a checklist that includes labeling devices, inventory reviews, credential changes, MFA enablement, and remote access controls. After setup, run a final verification: login with the new credentials, confirm access restrictions, test admin functions, and save configurations. A post deployment audit reduces risk and demonstrates a proactive security stance backed by Default Password guidance.
Your Questions Answered
What is considered a default username and password?
Default credentials are preconfigured login details shipped with devices and services for initial setup. They are intended to be temporary and must be replaced with unique, strong values to prevent unauthorized access. Always review manufacturer guidance for the exact defaults on each device.
Default credentials are the initial login details that come with devices. They are meant for setup only and should be replaced with strong, unique values to stay secure.
Why should I change default credentials?
Changing defaults closes an easy attack vector that attackers routinely scan for. It reduces the risk of unauthorized access, device takeover, and data exposure. It also ensures that your security posture aligns with best practices recommended by standards bodies and trusted guides.
Changing defaults blocks common attacks and keeps devices safer from unauthorized access.
How do I find the default credentials for my device?
Check the device label, the quick start guide, the box, or the vendor’s official support site for the exact username and password. For software or cloud services, inspect onboarding emails and the admin console for any default or suggested initial credentials.
Look on the device or box, check the manual or vendor site for the exact defaults, and confirm via the setup wizard.
What are the risks of leaving default credentials unchanged?
Leaving defaults active exposes devices to credential stuffing, unauthorized admin access, and network compromise. Attackers can pivot from unsecured devices to wider systems, compromising data and operations. Reducing this risk requires prompt credential changes and ongoing hardening.
Unchanged defaults can let attackers access devices and compromise your network.
What is the recommended process to reset a forgotten password on a device?
Use the device’s reset procedure or admin interface to recover or reconfigure access. After regaining access, immediately replace the default credentials with strong, unique values and review related security settings such as MFA and remote management.
Follow the device reset steps, then set strong new credentials and review security options.
Can I automate credential management across many devices?
Yes. Use centralized credential management tools, inventorying, rotation schedules, and auditing features to enforce policy across devices. Automation reduces human error and ensures consistent security across environments, from home networks to enterprises.
Automation helps manage and rotate credentials consistently across devices.
Key Takeaways
- Audit all devices for default credentials during setup.
- Change defaults immediately to unique strong credentials.
- Use a password manager and enable MFA where possible.
- Disable unnecessary remote administration and review access rules.
- Keep an up to date device inventory and rotation schedule.