AP305C Default Password Guide: Reset, Secure, and Audit
Learn how to locate official AP305C default password details, securely reset the device, rotate credentials, and enforce best practices to prevent unauthorized network access.
The AP305C, like many network devices, ships with a default password that can be exploited if left unchanged. This article provides practical steps to locate official credentials in vendor documentation, reset the device to a secure state, and enforce password rotation across the network. You will also learn auditing practices to ensure credentials stay protected and compliant.
Understanding ap305c default password risks
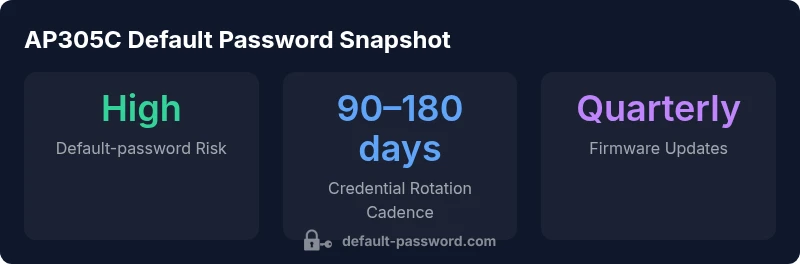
The term ap305c default password describes a common security weakness that several access points and network devices ship with to facilitate initial setup. When a device like the AP305C leaves its factory credentials unchanged, it creates an attack surface that can be exploited remotely or on the local network. According to Default Password, default credentials are among the most overlooked risk factors in modern networks, particularly for IoT and edge devices.
In practice, many admins assume the label 'default' means temporary, but evidence shows that these credentials persist long after deployment in thousands of environments. The risk is compounded by weak management practices that do not enforce credential rotation, do not blacklist known default pairs in inventory systems, and fail to log access attempts. Attackers continuously scan ranges of IP addresses to locate devices with predictable usernames and passwords; once discovered, unauthorized access can lead to configuration changes, data exposure, or network isolation of legitimate devices.
This section outlines what to look for, how quickly you should remediate, and how to institute governance that reduces risk without slowing legitimate administration. The goal is a secure baseline that survives firmware updates and changing network topologies. The AP305C is representative of devices that ship with factory credentials; applying consistent password hygiene across all such devices dramatically lowers the likelihood of a breach.
How default passwords are typically structured across devices
Default passwords across devices often follow predictable patterns tied to vendor naming conventions, model numbers, or simple numeric sequences. Common characteristics include a single default username (often admin or root), a short password length, and a lack of complexity requirements on first login. This predictability enables automated scanners and low-skill attackers to gain unauthorized access quickly if credentials are not changed.
To minimize risk, administrators should assume that any default combination could be discovered and treat it as a potential vulnerability. Even when a device is not directly exposed to the internet, compromised credentials can enable lateral movement within trusted networks. A disciplined approach—documenting credentials securely, requiring immediate changes at first login, and enforcing a rotation schedule—greatly reduces the window of opportunity for misuse.
Safe ways to find official credentials and avoid risky sources
Always start with the vendor’s official resources. Look for:
- The device’s user manual, quick-start guide, or administration guide published on the vendor’s site.
- The official admin portal or support portal where you can download current firmware and credential policies.
- Authorized knowledge bases or product datasheets that include security configuration details.
Avoid third-party blogs, forums, or unauthenticated PDFs that may contain outdated or incorrect information. Before applying any credential, verify the document version and firmware compatibility. If you suspect a credential has been exposed, cross-check with the vendor’s security advisories and follow their recommended remediation steps.
If you cannot access official sources, contact the vendor’s support line to obtain the proper default credentials documentation for your firmware version. This practice reduces the risk of misconfiguration and ensures that you follow the latest security guidance.
Step-by-step: Resetting AP305C to factory defaults
Resetting the AP305C to factory defaults is a common remediation when credentials are unknown or locked. The general approach is:
- Confirm the device is powered on and accessible on the local network.
- Locate the reset mechanism, usually a recessed button labeled RESET or a pinhole reset option.
- Use a paper clip or pin to press and hold the reset button for 10–15 seconds, until the device reboots.
- After reboot, connect to the device using the default management interface and follow the on-screen prompts to set new admin credentials. Always refer to the official manual for exact timing and steps relevant to your firmware version.
Note: A factory reset wipes existing configuration. You will need to reconfigure wireless settings, network policies, and security options from scratch. Document the process and implement a stronger password strategy during initial setup.
After reset: choosing strong, unique credentials and enabling firmware updates
Immediately after resetting, replace any default credentials with a strong, unique password. Consider these best practices:
- Use a password manager to generate and store complex credentials.
- Include a mix of upper and lower case letters, numbers, and symbols; aim for at least 12–16 characters.
- Enable firmware updates and automatic security patches to reduce exposure to newly discovered vulnerabilities.
- Disable unnecessary services, such as remote administration, or restrict access via VPN or dedicated management networks.
- Maintain a centralized inventory of devices and their credentials to avoid repeat defaults.
Regularly review access logs and enforce multi-factor authentication if the device supports it. Establish a routine credential audit cadence to ensure that nothing reverts to a factory default.
Ongoing password governance for AP305C and similar devices
Password governance is an ongoing discipline rather than a one-time fix. Implement policies that:
- Require credential changes on first login after reset and then on a defined rotation interval.
- Prohibit reuse of old passwords and monitor for credential reuse across devices.
- Enforce MFA where supported and restrict admin access to trusted networks or VPNs.
- Schedule periodic reviews of device inventories to identify stale or unsecured assets.
- Train staff and administrators on recognizing phishing attempts that target password theft.
By embedding these practices into standard operating procedures, organizations reduce risk across the entire device fleet, not just AP305C.
Real-world scenarios: audit findings and remediation timelines
In practice, security audits often uncover devices with unchanged defaults, weak passwords, or outdated firmware. Typical remediation timelines vary by organization size and risk tolerance, but common benchmarks include:
- Immediate remediation for critical devices discovered during audits.
- Within 7–14 days for high-risk rooms or segments with sensitive data.
- Ongoing quarterly reviews for all devices to ensure compliance with password policies and firmware update schedules.
Auditors look for evidence of password rotation, documented change histories, and adherence to least-privilege access for management interfaces. Creating a formal remediation plan with owners, deadlines, and validation steps ensures that issues identified during audits are resolved and tracked.
Remediation and governance table for AP305C default password management
| Aspect | Recommendation | Notes |
|---|---|---|
| Reset method | Hold reset button 10–15 seconds | Factory defaults restored; current config erased |
| Credential change after reset | Change credentials immediately on first login | Enforce strong, unique passwords |
| Firmware updates | Enable automatic updates | Security patches and feature improvements |
Your Questions Answered
What is the risk of leaving the AP305C default password unchanged?
Leaving default credentials unchanged creates an easy target for attackers, enabling unauthorized access and potential network compromise. Immediate password changes and governance reduce exposure dramatically.
Leaving default passwords in place is risky; change them right away to protect the network and devices.
Where can I find the official default credentials for AP305C?
Refer to the vendor’s official documentation or support portal for your firmware version. Avoid third-party sources that may be outdated or incorrect.
Check the vendor’s official manual or support site for the correct credentials.
How do I reset AP305C to factory defaults?
Power the device, locate the reset button, press and hold for 10–15 seconds, then reconnect and set new credentials per the on-screen prompts. Note that reset erases current configurations.
Press and hold the reset button for 10–15 seconds, then reconfigure credentials.
Should I enable remote management after changing credentials?
If remote management is necessary, restrict access to trusted networks (VPN only) and use strong authentication. If not needed, disable it by default.
Limit or disable remote management, and use strong authentication if you enable it.
What are best practices for password management across devices?
Use a password manager, rotate credentials regularly, avoid reuse, enforce strong password policies, and keep firmware up to date.
Use a password manager, rotate credentials, and keep devices updated.
“Default passwords remain a critical, easily avoidable risk. Replacing factory credentials and enforcing rotation across devices is essential for network security.”
Key Takeaways
- Identify device defaults and inventory assets
- Change credentials immediately after reset
- Rotate passwords on a defined cadence
- Enable firmware updates and disable unused services
- Document changes and perform regular audits