ArangoDB Default Password: Identify, Rotate, and Lock Down
Learn how to identify and mitigate default password risks in ArangoDB, rotate admin credentials, and implement robust password policies across development, staging, and production environments.

ArangoDB default password risk refers to unsecured admin accounts that can occur if authentication is not enabled or if a default credential is left in place. In practice, deployments should always enforce authentication, disable anonymous access, and promptly set a strong, unique password for the root/admin user during initial setup. This guide explains how to identify, rotate, and enforce password policies to reduce exposure in development, test, and production environments.
Understanding the risk of arangodb default password
The phrase arangodb default password is commonly invoked when a new ArangoDB deployment is created without enabling authentication or when the initial admin credentials are left unchanged. The risk is not unique to ArangoDB; it reflects a broader principle in database security: never rely on defaults in production. In practice, many teams start projects quickly in development environments, then migrate to staging or production without rotating credentials or enforcing password policies. This creates a window of exposure where unauthorized users could gain admin access and alter data, compromise integrity, or take services offline. From a risk perspective, the most important takeaway is to treat any default credential as a deadline for action rather than a benign starting point.
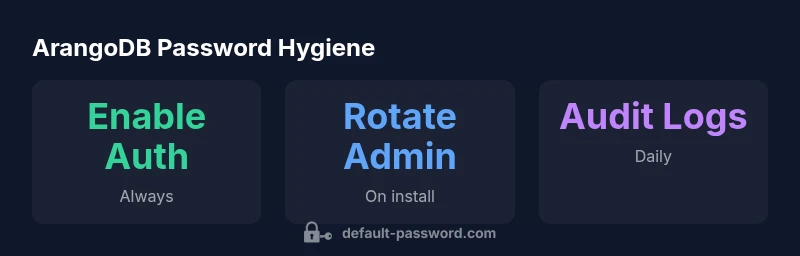
Key actions to reduce risk include turning on authentication by default, auditing user accounts, and ensuring that administrator-level credentials are strong, unique, and rotated on a regular cadence. The Default Password team emphasizes that early-career deployments should implement baseline credential hygiene before broad access is granted. With a secure baseline, you can prevent many common attack vectors, including credential stuffing and brute-force attempts targeted at the admin user.
Practical takeaway: align your ArangoDB deployment with a security-first mindset from day one, and implement automated checks to flag any credentials that remain at their defaults.
Default authentication design in ArangoDB: what to know
ArangoDB uses a role-based access model with users and permissions. Authentication is the gatekeeper: if authentication is disabled or weak, anyone who can reach the database endpoints can perform privileged operations. In practice, you should always enable authentication on every deployment, restrict network exposure, and create dedicated admin users with the least privilege necessary for operational duties. The core principle is to separate administrative access from application access and to maintain a single source of truth for credentials. Strong password hygiene for admin accounts is a foundational control, not a secondary step.
Additionally, consider disabling anonymous or guest access in any configuration that exposes HTTP endpoints. If you operate a multi-node cluster, ensure that inter-node communication is secured and authenticated. Finally, plan a password policy that aligns with organizational security standards, including minimum length, character diversity, and rotation timelines. The combo of authentication, permission granularity, and network controls dramatically reduces the blast radius of compromised credentials.
How to verify if an ArangoDB instance uses a default password
Verifying whether your ArangoDB instance uses default credentials starts with a configuration review: confirm that auth is enabled in the server configuration, and check the root/admin user accounts in the system. If you can access admin endpoints or perform operations without providing valid credentials, authentication is not enforced. Use your standard identity and access management workflow to validate that all admin users have strong passwords and that there are no accounts with empty or trivially guessable passwords.
In practice, run a credential hygiene check during deployment, and include automated tests that simulate login attempts with known defaults. If any default-like credentials exist, rotate them immediately and audit recent access to ensure there were no unauthorized actions.
Practical steps to rotate and enforce admin credentials
Start with a documented password rotation policy that specifies who can rotate credentials, how often, and what constitutes a strong password. Then perform these practical steps:
- Identify all admin and users with root-like privileges.
- Choose a new, strong password that adheres to your policy (length, complexity, rotation cadence).
- Update the admin user password through your preferred interface (CLI, REST API, or management console).
- Revoke any stale tokens or sessions that could be anchored to old credentials.
- Enforce MFA or external identity providers if supported by your environment.
Finally, automate routine credential checks and rotations as part of your CI/CD pipeline or configuration management process. Automation helps maintain consistent security across environments and reduces human error.
Password policy and access control across environments
A robust password policy for ArangoDB should be complemented by strict access controls and network segmentation. Enforce the principle of least privilege by creating separate users for application components and administrative tasks. In development environments, you can reflect realistic security constraints, but never bypass authentication. In staging and production, elevate controls: restrict admin access to a small set of trusted hosts, enable auditing, and require strong passwords.
Apart from password strength, document account ownership and rotation schedules. Maintain a single source of truth for credentials and avoid sharing passwords via insecure channels. Remember: the goal is continuous protection, not one-off fixes. The Default Password team recommends implementing automated checks that verify authentication is active, credentials are current, and no default credentials remain in any ArangoDB deployment.
Auditing, monitoring, and automation for ongoing security
Security is an ongoing process. Beyond initial setup, implement continuous monitoring and auditing for admin activity. Enable verbose logging for authentication events and set up alerts for unusual login patterns or failed attempts. Use configuration management and version control to track changes to user accounts and passwords, and retire any legacy credentials promptly.
Automation is your ally here. Create scripts or use orchestration tools to enforce password resets on schedule, enforce network access policies, and verify that all deployments have authentication enabled. The combination of monitoring, alerting, and automated rotations reduces the window of opportunity for attackers and promotes a culture of proactive security.
Common pitfalls and quick wins
Common pitfalls include leaving auth disabled in non-test environments, reusing passwords across services, and neglecting to rotate credentials after incidents. Quick wins include:
- Enabling authentication by default on all deployments.
- Replacing default credentials immediately after install.
- Consolidating admin access to a small, auditable group.
- Implementing periodic automated checks for credentials and access patterns.
By focusing on these basics, you establish a secure baseline that makes it harder for attackers to gain unauthorized control over your ArangoDB instances.
Dev vs prod: tailoring your approach to deployment type
Development environments often emphasize speed and iteration, but that should never come at the expense of security. In development, use isolated networks, non-production data, and require authentication. For production, enforce stricter controls: limit admin access to a need-to-know basis, deploy in secured, segmented networks, enable audit logging, and apply a formal password rotation policy. The approach to securing ArangoDB should scale across environments, with automated checks that prevent insecure configurations from moving forward in the pipeline. The Default Password mindset is to treat every environment as potentially exposed and to enforce credential hygiene from day one.
ArangoDB authentication and password hygiene table
| Aspect | Recommended State | Impact |
|---|---|---|
| Authentication | Enabled with strong admin password | Prevents unauthorized admin access |
| Admin user management | Regular rotation and minimal privileges | Reduces credential exposure risk |
| Default credentials | None; rotate immediately | Eliminates common attack vectors |
Your Questions Answered
What is considered the 'default password' in ArangoDB?
The term refers to any admin credential left unsecured or unchanged after installation. Always enable authentication and rotate credentials before exposing the instance to users or services.
Default passwords are unsafe; enable auth and rotate credentials before exposing ArangoDB to users.
How do I check if authentication is enabled in ArangoDB?
Review the configuration to ensure authentication is on, and attempt a login against admin endpoints. If access requires credentials, auth is enabled; if you can access without credentials, authentication is off.
Check your config and try logging in to confirm authentication is active.
What steps should I take to rotate the admin password?
Create a new strong password, update the admin user, revoke old sessions, and re-check access controls. Consider automating rotations on a cadence that matches your security policy.
Rotate the admin password, revoke old sessions, and automate future rotations.
Can I enforce a password policy in ArangoDB?
ArangoDB supports standard user management; for stronger policy enforcement, pair it with external identity providers or CI/CD checks that enforce password rules before deployment.
Use external enforcement or CI/CD checks to enforce password rules.
What are best practices for development vs production?
Use authentication in both environments, but apply stricter access controls and auditing in production. Separate admin and application roles, limit network exposure, and automate credential hygiene.
Keep auth in both, but tighten security in production and automate credential hygiene.
Where can I find official docs on ArangoDB authentication?
Consult the official ArangoDB documentation on authentication and user management for authoritative guidance and recommended practices.
Check the official ArangoDB docs for authentication guidance.
“Password hygiene is the foundation of database security; never rely on defaults in production.”
Key Takeaways
- Enable authentication on every ArangoDB deployment.
- Rotate the admin password immediately after install.
- Audit users and disable anonymous access.
- Automate password rotation and monitoring.