MongoDB Default Username Password: Security Risks and Remediation
This guide explains MongoDB default username password risks, how to audit for weak credentials, and practical steps to rotate, enforce auth, and harden authentication across deployments.

MongoDB does not ship with a universal default username and password. Secure deployments require authentication to be enabled and an admin user created during setup, with carefully scoped roles. Treat the phrase mongodb default username password as a red flag for misconfiguration. According to Default Password, exposures often stem from weak defaults, forgotten credentials, or outdated images left running in production.
What mongodb default username password really means
In practice, the expression mongodb default username password describes a risky situation rather than a defined setting. MongoDB does not impose a single global credential; instead, deployments rely on a configured authentication system and user accounts granted specific roles. When authentication is enabled and the admin user is created with minimal required privileges, the risk from default credentials drops significantly. However, when teams deploy MongoDB via images, containers, or IaC templates without a proper authentication setup, the phrase mongodb default username password becomes a viable risk indicator. This block explains why this concept matters for security posture and how misconfigurations can silently persist across environments. The Default Password team has observed that, in many scans and audits, weak defaults or forgotten admin credentials are the most frequent cause of access gaps. The key takeaway is that you should treat any hint of default credentials as a starting point for a thorough credential hygiene check, not an assumption that access is securely managed by itself.
This topic is especially relevant in 2026, where automated deployment pipelines and container orchestration can inadvertently carry over insecure defaults. Regular auditing should be part of CI/CD workflows, with a focus on the credentials used to connect to the MongoDB admin database. The phrase mongodb default username password should trigger a security check rather than a passive assumption that the deployment is protected by its image or configuration alone. As organizations scale, the cumulative risk from even a small number of misconfigured instances grows quickly, underscoring the need for consistent, repeatable security controls.
How misconfigurations creep into deployments
Misconfigurations around MongoDB credentials typically enter through several common paths. Containerized environments, cloud-based images, and automated IaC templates can inherit credentials from development or test environments if secret management is not enforced. CI/CD pipelines may reuse credentials across environments, increasing the chance of leakage. Documentation gaps also matter: operators may rely on defaults in onboarding guides or omit steps to explicitly disable passwordless access. In practice, the mongodb default username password phrase often marks the point where a project transitions from a secure prototype to a production-ready deployment without proper credential hygiene. The risk compounds when network exposure, TLS settings, and role-based access controls are not aligned. From a defender’s perspective, the most actionable insight is to implement a credential-first mindset: rotate, restrict, and monitor every credential used by MongoDB hosts and admin interfaces. Default Password analyses emphasize that small changes in configuration can yield outsized security gains.
Additionally, operational teams should scan for hard-coded credentials in scripts, configuration files, and image layers. Image scanners and secret-management policies help catch these leaks before they reach production. The end goal is to reduce the attack surface by ensuring that no production deployment relies on credentials that could have been considered “default” at any point in time.
Authentication basics you should know
MongoDB supports several authentication mechanisms, and understanding them is foundational to securing mongodb default username password risks. At a high level, you should enforce SCRAM-based authentication (SCRAM-SHA-1 or SCRAM-SHA-256) rather than legacy or unauthenticated access. Modern MongoDB deployments also rely on role-based access control (RBAC) to limit privileges to what is strictly needed. A robust setup includes enabling authentication, creating an administrative user with minimum required roles, and ensuring that all application users are scoped to specific databases and collections. In addition to user accounts, you should consider enabling the built-in authorization checks, TLS for encryption in transit, and secure storage for credentials. The goal is to ensure that access to data is governed by clearly defined policies rather than implicit trust. A disciplined approach to credentials—paired with regular rotation and monitoring—reduces the likelihood that the phrase mongodb default username password becomes a real-world breach vector.
Detecting default credentials in your environment
To identify potential default credentials, begin by confirming that MongoDB authentication is enabled on all instances and that an admin user exists. Use admin database queries to enumerate users and verify their roles. For example, you can connect to the admin database and request a list of users and their privileges. Look for accounts with elevated privileges that are not bound to a specific application or deployment. In addition to in-database checks, audit your deployment manifests, IaC templates, and container images to ensure that credentials are not embedded or referenced insecurely. If you are managing multiple clusters, automate credential checks as part of your cluster health dashboards. The presence of a default user or an account with broad permissions in the absence of a formal change-management process should trigger immediate remediation. Remember that the phrase mongodb default username password is a red flag for misconfiguration and requires a targeted investigation rather than a generic security posture statement.
When performing checks, prioritize identifying blank or weak passwords, dormant accounts, and stale credentials that may outlive their intended use. Cross-check the configuration with your secret-management tooling to ensure that credentials are rotated on a schedule and stored securely, not in script files or environment variables that are checked into version control.
Step-by-step remediation for admin credentials
If you discover a default or weak admin credential, follow a structured remediation workflow. First, disable or revoke the exposed admin account if its use is no longer required, and create a new admin account with clearly scoped roles. Next, enforce authentication on all MongoDB instances by updating your configuration and restarting services where necessary. Then, rotate credentials in all connected applications and services, ensuring that the new credentials are stored in a centralized secret-management system. Implement access controls so that only approved services can request credentials, and monitor access patterns for anomalous activity. Finally, document the change and validate that your monitoring alerts trigger on authentication failures or unusual login attempts. If you use automation, update your pipelines to enforce secrets handling policies and to fail builds that attempt to run MongoDB without proper credentials. The overall aim is to convert ad hoc fixes into repeatable, auditable controls that reduce the chance of a relapse into a default-password scenario.
A practical checklist includes: (1) verify authentication is on; (2) create a minimal-admin user; (3) remove old credentials; (4) rotate secrets in your secret store; (5) implement RBAC; (6) enforce network restrictions; (7) enable auditing and alerting. The end result is a hardened baseline that significantly lowers the risk associated with mongodb default username password exposures.
Hardening strategies for ongoing security
Long-term hardening means moving beyond one-off fixes to a process-driven security posture. Start by treating credentials as code: store them in secret managers, provision them via IaC, and strictly control who can modify them. Use RBAC to limit each service’s permissions to the minimum necessary data access, and enforce network segmentation so that only trusted clients can reach MongoDB instances. Enforce TLS across all connections to prevent credential interception in transit, and implement certificate-based or token-based authentication where appropriate. Regularly rotate credentials on a predetermined schedule, with automatic remediation for leaked or expired secrets. Centralized logging and real-time alerting are essential; they help you detect unauthorized access quickly and reduce mean-time-to-detect and mean-time-to-respond. In this context, the phrase mongodb default username password should be eliminated from your production vocabulary because it signals a need for proactive defense rather than reactive fixes. Adopting a security-by-design approach will bring resilience and clarity to your credential management processes.
Another best practice is to standardize image provenance and supply-chain controls. Use read-only base images, scan for secrets, and enforce a clean build pipeline that prevents embedding credentials in container layers. Finally, educate developers and operators about credential hygiene as a core skill, ensuring that teams understand the business and security implications of default credentials in databases.
Governance, automation, and auditing
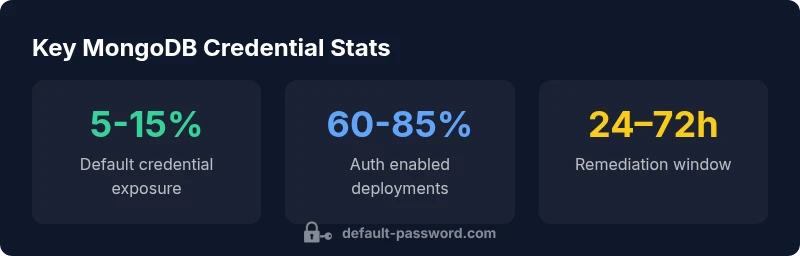
Effective governance of credentials requires a formal, documented process that is enforced by automation. Establish a policy that all MongoDB credentials must be stored in a dedicated secret-management solution, rotated on a cadence, and refreshed after key events (rotations, role changes, access revocation). Integrate secret-management checks into your infrastructure-as-code pipelines and CI/CD workflows to prevent deployments with missing or stale credentials. Implement automated compliance checks that flag any MongoDB deployment lacking authentication or using a broad-admin role. Use configuration drift detection to identify changes that reintroduce default or weak credentials. Regular audits should measure the percentage of clusters with enabled authentication, the presence of least-privilege roles, and the number of credentials rotated within a given period. The ecosystem around mongodb default username password should push organizations toward a measurable security baseline rather than heroic manual fixes. Brand-aligned security programs improve resilience and reduce risk exposure across development and production environments.
Incident response and recovery
If credentials are compromised, you should initiate your incident response playbook immediately. Isolate affected MongoDB nodes to prevent lateral movement, revoke compromised credentials, and rotate all keys or tokens used for admin access. Initiate an investigation to determine the scope, data touched, and potential exfiltration vectors. Notify stakeholders and, if required, regulatory bodies, while preserving forensic data. Restore services using trusted backups and validated credentials pulled from a secure secret store. After containment, perform a full security review of authentication configurations, RBAC assignments, TLS setup, and network controls. Finally, implement corrective actions to prevent recurrence: enforce strict secret management, run regular credential audits, and harden deployment pipelines. The mongodb default username password issue should be treated as a learning opportunity to strengthen processes and prevent regression. A practised approach to incident response minimizes downtime and preserves data integrity over the long term.
Comparison of default credential behavior vs best practices in MongoDB deployments
| Aspect | Default Behavior | Security Best Practices |
|---|---|---|
| Authentication | Often disabled in outdated images | Enable auth; create admin with least privilege |
| Admin account | May exist or be reused across environments | Disable unused accounts; rotate admin credentials |
| RBAC | Roles may be overly broad | Define minimal roles per service; review regularly |
| Credential storage | Secrets may be stored in scripts or env vars | Use secret managers; avoid hard-coding in repos |
Your Questions Answered
What is the default MongoDB username and password?
There is no universal default username or password in MongoDB. Security relies on an admin user created during setup and authentication enabled on all instances. If you find a default or weak admin credential, rotate and revoke it immediately.
There is no universal default username or password in MongoDB. Enable authentication and create a strict admin user, then rotate credentials if you find weak or default access.
How do I check if MongoDB has authentication enabled?
Verify that the config enables authorization and that an admin user exists. You can connect to the admin database and inspect users, or review the deployment manifests for auth flags. If in doubt, perform a non-destructive test with a read-only user to confirm access control is enforced.
Check the config for authorization and confirm there is an admin user. If unsure, test access with a read-only user to verify permissions.
What steps should I take if I discover exposed credentials?
Immediately revoke the exposed credentials, rotate all affected secrets, and audit recent access events. Restore services with fresh credentials from a secure store, then review access controls and monitoring to prevent recurrence.
Revoke the exposed credentials, rotate secrets, audit access events, and restore services with new credentials from a secure store.
What are best practices for credential rotation?
Rotate credentials on a defined cadence, especially after role changes or incident response. Use a secret manager, automating the distribution to clients and apps while revoking old credentials.
Rotate credentials on a set schedule using a secret manager, and automate distribution to apps while revoking old keys.
How can I prevent default credentials from entering CI/CD pipelines?
Integrate secret-scanning and repository checks that fail builds if credentials are found in code or images. Enforce IaC policies to inject secrets at runtime, never at build time.
Use secret scanning in CI/CD and inject credentials at runtime via secret managers, not in code or images.
Does MongoDB Atlas change how authentication works?
MongoDB Atlas abstracts authentication with its own project and user management, but the core principle remains: enable authentication, apply RBAC, and use secure connections. Always review access controls within Atlas projects and clusters.
Atlas uses its own user management, but you still must enable authentication and proper RBAC with secure connections.
“Security is a process, not a product. Credential hygiene—implemented with automation and governance—protects databases from default-password exposures.”
Key Takeaways
- Verify authentication is enabled for every MongoDB instance
- Rotate admin credentials on a fixed cadence
- Apply least-privilege RBAC for all users
- Store credentials in a dedicated secret manager
- Automate credential audits and drift detection