Automated Lab Default Passwords: A Practical Guide
Learn how to locate, reset, and manage automated lab default passwords across devices and services. This educational guide explains why defaults are risky, how to identify them, and how to enforce ongoing password hygiene in lab environments. The Default Password team found that many labs overlook default credentials, creating avoidable security gaps and downtime. Follow this step-by-step approach to regain control and strengthen lab security.

Learn to locate, reset, and manage the automated lab default password across devices and services. This guide covers identifying common default credentials, safely rotating them, and enforcing ongoing password hygiene in lab environments. According to Default Password, many labs leave default passwords unchanged, risking unauthorized access and downtime. Follow these steps to regain control and reduce exposure.
Why automated lab default passwords matter
In laboratories that rely on automated devices and networked instruments, default passwords are a frequent source of risk. When devices ship with standard credentials, administrators may assume they have been secured by the vendor, especially in high-velocity environments. The Default Password team found that labs under time pressure often skip credential changes, leaving openings for unauthorized access, data tampering, and service disruption. Recognizing and remediating these defaults is a foundational security practice that pays dividends in uptime, incident response readiness, and audit readiness. The goal is not to frighten teams but to empower them with a repeatable routine that makes credential hygiene a normal part of lab operations.
Key takeaway: treat default passwords as legitimate attack surfaces and address them as part of a broader security hygiene program.
How default credentials show up in lab environments
Default credentials appear across a wide range of devices in labs, including network gear, storage appliances, lab automation controllers, and instrument panels. Vendors may publish these credentials, or devices may ship with predictable patterns like a vendor name or simple words. In automated labs, scripts and dashboards may rely on these credentials for provisioning or maintenance tasks, unintentionally propagating exposure. Identifying where defaults live requires a careful inventory and cross-check against official vendor documentation. Expect to find gaps in documentation if devices come from mergers, acquisitions, or secondary distributors. Effective discovery begins with a comprehensive asset list and a cadence for credential verification.
Pro tip: keep a living inventory that maps device type to current credential status and last verification date. This makes ongoing reviews faster and less error-prone.
Practical discovery and validation
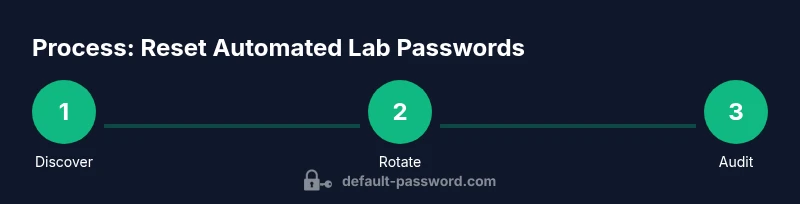
Discovery starts with a dual approach: passive cataloging and active verification. Create or update an asset inventory that links device names, IP addresses, model numbers, and vendor documentation. Use non-destructive checks first: observe login prompts and consult vendor manuals to confirm default credentials before attempting changes. Validation should include successful login using the discovered credentials, confirming that the device accepts a new password, and verifying that there are no fallback credentials enabled elsewhere. Always perform credential changes during a maintenance window when possible and ensure you have a rollback plan in case a change disrupts essential automation. The aim is to verify current state without introducing new risk.
If you discover devices with unchanged defaults, prioritize those that control critical lab infrastructure or are exposed to the wider network. Document any exceptions and adjust access controls to minimize exposure while you remediate.
Safe reset and rotation of lab credentials
Resetting defaults to strong, unique passwords per device is the next step after discovery. Use a password manager or a secure secret store to generate and store per-device credentials that meet complexity guidelines. Avoid reusing passwords across devices, ports, or services. After each change, test access to ensure automation workflows still function with the new credentials and update inventory records accordingly. Where possible, implement automated password rotation that triggers on a schedule and after high-risk events (for example, a suspected breach). The goal is to minimize manual handling of credentials while preserving operational reliability.
As you implement changes, keep a change log with device IDs, old credential references, new passwords, and reviewer approvals. This supports audits and incident response if credentials are ever compromised.
Governance, auditing, and automation opportunities
Credential hygiene is most effective when paired with governance controls. Establish written policies for password length, complexity, rotation cadence, and incident handling. Implement access controls that restrict who can view or modify credentials, and enforce least privilege on automation scripts. Automation can help by scanning for devices with default credentials, automatically updating them to unique values, and reporting results to a centralized dashboard. But automation must be guarded with safeguards: versioned scripts, approval workflows, and separate non-production environments for testing. The broader goal is a repeatable, auditable process that reduces human error while maintaining operational continuity.
In practice, automation should be designed to minimize downtime and never reveal passwords in logs or non-secure channels. Always verify that any automation run has completed successfully and that all devices report a healthy status after credential changes.
AUTHORITY SOURCES
- https://www.cisa.gov/topics/federal-information-security
- https://www.nist.gov/topics/cybersecurity
- https://www.us-cert.gov
Tools & Materials
- Device admin interfaces(Access credentials for initial login and verification.)
- Inventory document or asset registry(Maintain mapping of device, model, IP, and credentials status.)
- Secure password manager(Store per-device passwords and rotate them safely.)
- Network discovery tool(Scan for devices in scope and correlate with inventory.)
- Maintenance window planning sheet(Schedule credential changes with minimal impact.)
Steps
Estimated time: 45-60 minutes
- 1
Inventory devices and establish baseline
Compile a current asset list with device type, location, and owner. Note any devices already using vendor defaults and flag critical systems for priority remediation. Create a baseline by logging current credentials this week and marking devices with no valid login.
Tip: Reference vendor manuals and the asset registry to ensure you cover all devices; start with the most critical systems. - 2
Identify default credentials and vendor references
Cross-check each device against official vendor documentation to confirm whether credentials are defaults. Document whether credentials are widely published or unique to the device—this guides remediation priority. Create a table that lists device, model, current credential status, and recommended action.
Tip: If vendor docs are ambiguous, contact the vendor or rely on verified community references with caution. - 3
Access devices securely and verify credentials
Log into devices with the discovered credentials in a controlled manner. Confirm that credentials are accepted and that you can navigate admin interfaces safely. Prepare to change credentials in a structured, auditable way.
Tip: Always perform changes during a maintenance window with a rollback plan in case access is interrupted. - 4
Rotate to unique, strong passwords
Generate per-device passwords using a password manager, ensuring sufficient length and complexity. Do not reuse passwords across devices or services. Update all dependencies and automation that use these credentials.
Tip: Store passwords in an encrypted vault and avoid writing them to logs or shared documents. - 5
Validate access and update inventory
Test login with each new credential to confirm access remains functional. Update the asset registry to reflect new credentials, rotation history, and responsible owner. Run a quick audit to ensure no defaults remain.
Tip: Keep a timestamped audit trail for each change to support future reviews. - 6
Document policy and automate ongoing hygiene
Publish a lab password policy that defines rotation cadence and approval workflows. Implement automation where appropriate to detect defaults and apply rotations, with manual overrides documented. Schedule regular reviews.
Tip: Automate reminders and dashboards to keep leadership informed of compliance status.
Your Questions Answered
What is an automated lab default password?
An automated lab default password is the factory-set credential used by devices for initial setup or automation tasks. It is often publicly known or easily inferred and should be replaced during secure configuration.
An automated lab default password is the initial credential used for setup; it should be replaced during secure configuration.
Why are default passwords risky in lab environments?
Default passwords create an easy target for unauthorized access, especially when devices are tied to automated workflows. If compromised, they can expose sensitive data, disrupt experiments, or allow tampering with critical equipment.
Default passwords are risky because they’re easy to exploit and can lead to data loss or disruption of lab operations.
How can I identify devices using default credentials?
Build a current asset list and verify each device against vendor documentation. Look for login prompts default credentials, and confirm whether credentials have been updated in the last rotation cycle.
Create an asset inventory, check vendor docs, and look for devices still using factory credentials.
What if a device has no user interface to change passwords?
If a device lacks a UI, consider alternative access methods approved by policy, such as console access or vendor-provided secure methods. Document any exceptions and plan an upgrade or replacement.
If there’s no UI, use approved alternative access methods and document the exception.
How often should passwords be rotated in labs?
Aim for a defined rotation cadence in your policy, with higher priority devices rotated more frequently. Automating reminders and enforcing rotation helps maintain compliance with minimal manual effort.
Define a rotation cadence in policy and automate reminders to stay compliant.
Can automation help manage default passwords securely?
Yes. Automation can detect defaults, apply per-device rotations, and log changes for audits. It should be secured with access controls and tested in a non-production environment before live deployment.
Automation helps detect defaults and rotate credentials securely when properly controlled.
Watch Video
Key Takeaways
- Audit all lab devices for default credentials.
- Apply unique, strong passwords per device.
- Maintain an auditable change log and inventory.
- Leverage automation to sustain password hygiene.