Safeguard Default Passwords: A Practical How-To Guide
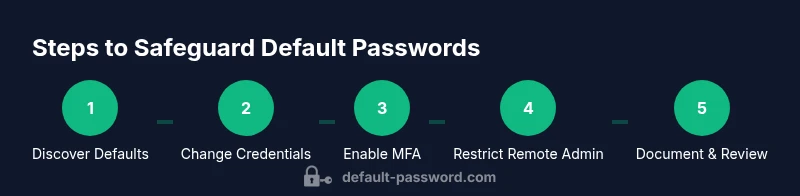
Learn a practical, step-by-step method to safeguard default password across devices and services: locate defaults, replace with strong unique passwords, enable MFA, and enforce ongoing hygiene.

You will learn how to safeguard default password across devices and services by locating wired defaults, replacing them with strong unique passwords, enabling MFA where available, and implementing ongoing password hygiene. You'll also establish monitoring, documentation, and an incident-response plan to reduce risk across your network. Use a password manager, rotate credentials periodically, and document ownership.
Why safeguarding the default password matters
Default credentials are a foundational attack surface that attackers frequently exploit to gain initial access. According to Default Password Team, devices shipped with standard admin passwords—especially routers, cameras, printers, and IoT gizmos—remain a common entry point. The consequence is a compromised network, data breaches, and costly remediation. When you safeguard default password practices, you compress the window of opportunity for attackers and make it far harder for unauthorized users to move laterally. Implementing disciplined credential hygiene also simplifies future audits and reduces downtime caused by compromised devices.
How to identify devices with default credentials on your network
Begin with an asset inventory that lists all networked devices, models, and firmware versions. Look for devices with “admin/admin” or “root/password” in the login prompts, default SSH keys, or vendor documentation that still references factory credentials. Use network scanning tools and review device manuals to confirm where defaults exist. Prioritize routers, switches, cameras, printers, and any IoT hub. Document findings in a centralized asset register to guide remediation and repeat audits. A systematic discovery is the first essential step toward long-term security.
Core steps to change and strengthen credentials across devices
- Access each device’s admin interface during a maintenance window. 2) Create a strong, unique password per device using a password manager. 3) Disable or delete the default credential pair and enforce password complexity rules. 4) If the device supports MFA, enable it and pair it with an authenticator app. 5) Update firmware where available to close known vulnerabilities. 6) Remove unused remote administration features to reduce exposure. 7) Document changes and tag the device ownership. 8) Schedule periodic reviews to verify credentials remain strong and unique.
Enable MFA, network segmentation, and overall hygiene
Where possible, enable multi-factor authentication for device management portals and admin consoles. Segment your network so that IoT devices live on a separate subnet with restricted access to sensitive resources. Treat default credentials as a red flag during audits and ensure every device has an owner who is responsible for post-change maintenance. Enforce a password policy that requires unique passwords for each device, and integrate this policy with your organization’s broader security program. These steps collectively reduce risk and streamline ongoing governance.
Create a password hygiene plan and documentation
Develop a formal password hygiene plan that includes: inventory maintenance, change scheduling, and a clear escalation path if a device cannot alter its default password. Maintain documented evidence of each credential change, including date, device model, and owner. Regular training on credential handling for IT staff helps prevent inadvertent disclosures. Store sensitive credentials only in approved password managers with access controls and audit logs. A documented process makes compliance easier and supports audits.
Practical tools and resources to safeguard default passwords
Tools & Materials
- Admin access credentials (for devices under management)(Needed to login and perform credential changes on each device.)
- Device manuals or vendor admin guides(Reference factory-default details and change procedures for each model.)
- Workstation with browser/SSH client(Used to access management interfaces or CLI for changes.)
- Password manager(Store and generate strong, unique credentials for every device.)
- MFA app or hardware token(Enable where supported for device management portals.)
- Firmware update access(If updates are available, prepare and apply securely.)
Steps
Estimated time: 90-120 minutes for initial pass; ongoing maintenance 30-60 minutes per quarterly review
- 1
Audit and inventory devices
Create a centralized list of all devices with default credentials. Include model, serial, firmware, and login method. This establishes the scope for remediation and helps track progress.
Tip: Start with high-risk devices (routers, gateways) and IoT hubs. - 2
Access each device’s admin interface
Log in with existing credentials to verify the current state. If you cannot login, consult the vendor support channels for reset procedures.
Tip: Do not reset credentials on critical devices during peak hours. - 3
Change to strong, unique passwords per device
Generate passwords using a password manager with at least 16 characters, a mix of letters, numbers, and symbols. Avoid reuse across devices.
Tip: Consider different password patterns for different device categories. - 4
Enable MFA where possible
Activate multi-factor authentication for management portals. Use an authenticator app or hardware token when supported.
Tip: If MFA is not supported on a device, document the limitation and plan for alternatives. - 5
Disable or restrict remote admin features
Turn off remote admin or limit access to trusted networks/IPs to reduce exposure.
Tip: Record the changes in your asset register. - 6
Update firmware and review security settings
Apply the latest firmware and review default services that may expose credentials (Telnet, UPnP, etc.).
Tip: Automated firmware alerts can help maintain currency. - 7
Document changes and assign ownership
Annotate changes with date, administrator, and reason. Assign device ownership for ongoing maintenance.
Tip: Use a centralized change log for audits. - 8
Schedule routine credential reviews
Set quarterly reviews to verify credentials, update passwords, and re-assess risk.
Tip: Automated reminders help sustain discipline.
Your Questions Answered
What counts as a default password?
Default passwords are the factory credentials shipped with a device or service. They often appear as admin/admin or root/password. These credentials should be replaced during initial setup or as soon as possible after deployment.
Default passwords are factory credentials that should be replaced during setup to prevent unauthorized access.
Why is safeguarding default passwords critical for security?
Default credentials are a common entry point for attackers. Replacing them with strong, unique passwords plus MFA significantly reduces the risk of unauthorized access and lateral movement within your network.
Safeguarding defaults reduces attacker access and helps protect your network from breaches.
How do I identify devices with default credentials on my network?
Create an asset inventory, review login prompts, and check vendor guides for factory credentials. Use network scanners and logging to detect devices that still use defaults.
Make a list of devices, check their login prompts, and use scanners to find defaults.
Is MFA supported on all devices?
Not all devices support MFA. When available, enable MFA for device management portals. If MFA isn’t supported, document limitations and rely on strong passwords and network segmentation.
MFA isn’t on every device, but enable it wherever possible and strengthen other controls where it isn’t.
What should I do if a device cannot change its default password?
Isolate the device on a separate network segment, restrict its access, and monitor it closely. Plan a replacement if feasible.
If you can’t change it, isolate the device and keep an eye on it.
How often should I audit and rotate passwords?
Aim for quarterly credential reviews and annual comprehensive password audits. Adjust frequency based on risk and device criticality.
Do regular checks every few months and adjust for risk.
Watch Video
Key Takeaways
- Audit all devices for default credentials and localise remediation
- Change defaults to strong unique passwords per device
- Enable MFA where supported to add protection
- Discontinue or restrict remote admin access to reduce exposure
- Document changes and schedule regular credential reviews