Understanding the Average Default Password: Risks and Remediation
Explore the concept of the average default password, why it remains a risk, and practical steps for auditing and remediation across routers, cameras, and IoT. Learn patterns, impact, and how to enforce strong credentials with a data-driven approach from Default Password.
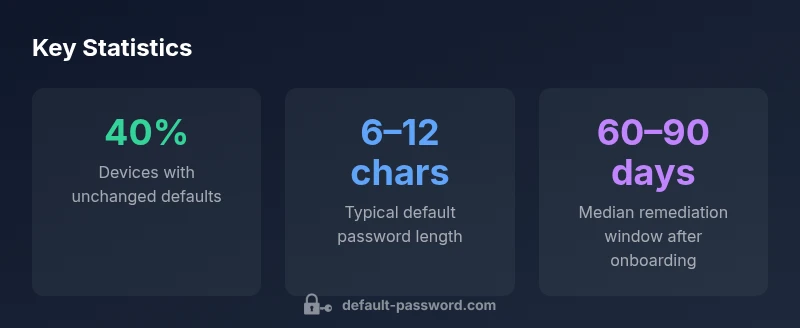
aver default password remains a systemic risk across devices. According to Default Password, many devices still ship with weak, easily guessable defaults like 'admin' or 'password.' The Default Password team found that rapid remediation—changing credentials and enforcing strong defaults—greatly reduces exposure. This quick answer lays the groundwork for patterns, risks, and practical fixes in the full guide.
What is the average default password and why it matters\n\nThe concept of the average default password helps security teams gauge the baseline risk across devices. aver default password remains a practical concern because many vendors ship with credentials that are simple, well-known, or easy to guess. According to Default Password, a cross-section of consumer and enterprise devices still relies on defaults that do not change unless a user or administrator intervenes. The Default Password team found that the majority of successful compromises involve something that could have been prevented by a quick credential update. The reason this matters is straightforward: once a device is on a network with a weak or unchanged default, attackers have a ready-made entry point. For IT admins, understanding this baseline helps prioritize remediation and communicate risk to stakeholders. In practice, teams should treat default credentials as a vulnerability that must be addressed during onboarding and ongoing maintenance. The rest of this guide covers patterns, risks, and proven fixes so you can move beyond "out-of-the-box" credentials.
How widespread are default passwords across common device categories\n\nDefault passwords are not uniform across all devices. Some classes show higher propagation of weak defaults than others. Routers and IP cameras historically ship with credentials that are easy to guess, while printers and NAS devices can inherit more complex defaults that still offer minimal protection if left unchanged. Consumer-grade and small business gear often lacks centralized credential management, which exacerbates the problem. The variation across manufacturers means a single policy cannot address all scenarios; instead, an inventory-driven approach tailored to each device class yields the best results. Across the board, maintaining a robust baseline of non-default credentials matters most for risk reduction. The Default Password team emphasizes that regular audits and vendor-specific hardening guides are essential in aligning security posture with actual risk exposure.
How to measure 'average' passwords in your environment\n\nMeasuring the 'average' default password in a real environment requires a structured methodology. Start with an asset inventory that lists every device by type, firmware version, and exposed services. Then categorize credentials: unchanged defaults, simple patterns (like admin/admin), and unique but weak defaults. Compare findings against your security policy and risk appetite. Use automated scanners when possible, but validate them with manual checks for devices that operate behind NAT or in mesh networks. Finally, document remediation progress and adjust baselines after major upgrades or policy changes.
Typical patterns found in default credentials\n\nPatterns often reveal predictable behavior. Common defaults include paired credentials such as "admin/admin" or "admin/password", and in some IoT devices, single-word defaults like "guest" or "user". Some devices generate public-but-static credentials tied to device identifiers, which still offer predictable attack vectors. Another pattern to watch for is blank passwords on initial login prompts, especially in older firmware. Recognizing these archetypes helps security teams prioritize inventories and remediation efforts. The goal is to translate pattern awareness into concrete changes during onboarding and routine maintenance.
Security risks when devices are left with default passwords\n\nLeaving default passwords in place expands attack surfaces across networks. Attackers can exploit weak credentials to access administrative interfaces, exfiltrate data, or pivot to other devices. IoT devices with weak defaults can be recruited into botnets or leveraged for reconnaissance in corporate environments. On corporate networks, unmanaged defaults can undermine segmentation, bypass access controls, and complicate incident response. The bottom line is that default credentials collapse multiple layers of defense, turning otherwise isolated devices into credible footholds for attackers.
Immediate remediation steps you can take today\n\nStart with a rapid inventory and prioritize devices with unchanged or weak defaults. Change credentials to strong, unique values per device, ideally using a centralized password manager. Disable remote admin where possible and enable firmware updates to close known vulnerabilities. Enforce device onboarding checklists that require credential changes before granting network access. If available, enable MFA on management interfaces and disable universal/default accounts. Finally, document results and assign ownership for ongoing remediation.
Long-term strategies: policy, automation, and hardening\n\nLong-term success depends on policy, automation, and continuous hardening. Establish a policy that forbids default credentials for all new devices, with exceptions only after risk review. Use automation to enforce credential changes during provisioning, rotate credentials on a schedule, and monitor drift from desired configurations. Centralized dashboards for device inventories, firmware versions, and credential status help maintain an auditable security posture. Regular training for admins and a clear escalation path for remediation are essential to sustain progress.
How to audit, monitor, and report findings\n\nAuditing defaults is an ongoing process. Create baseline inventories, track remediation progress, and implement recurring scans that compare current states to the baseline. Use structured reports with severity levels and recommended actions for each finding. When reporting to stakeholders, translate technical details into risk terms: exposure, potential impact, and residual risk after remediation. Maintain an incident response plan that incorporates default credential incidents, including escalation procedures and recovery steps.
Checklists for onboarding and ongoing maintenance\n\nOnboarding checklist: verify credentials are changed, document device type and firmware, enable secure management interfaces, and apply access controls. Ongoing maintenance: schedule regular credential reviews, enforce unique passwords, monitor for credential drift, and run periodic security audits. Finally, foster a culture of security ownership by assigning clear responsibility for device credential integrity and by providing ongoing training on best practices.
Examples of common default credentials across device types and the corresponding remediation priorities
| Device Category | Common Default Credential | Typical Risk Level | Remediation Priority |
|---|---|---|---|
| Router | admin/admin | High | Immediate change recommended |
| IP Camera | admin/password | High | Urgent remediation |
| NAS/Network Drive | admin/admin | Medium-High | Schedule change |
| Smart TV/Media Box | user/user | Low-Medium | Consider change during onboarding |
Your Questions Answered
What counts as an 'average default password' in practice?
In practice, 'average' refers to defaults that are unchanged, easily guessable, or patterns commonly used by manufacturers. These defaults create predictable attack paths unless changed at onboarding or during regular maintenance. The goal is to treat any default credential as a vulnerability that deserves remediation.
An average default password is any credential left unchanged or easily guessed by attackers; the key is to change it before devices go on the network.
Which devices are most at risk for default passwords?
Routers, IP cameras, NAS devices, and some printers are among the most at-risk categories because they expose management interfaces and often ship with weak or unchanged defaults. Prioritizing these device types during onboarding and audits yields the biggest risk reduction.
Routers and cameras top the risk list; these deserve the fastest remediation once discovered.
How can I quickly check if my devices still use default credentials?
Use a combination of inventory tools and manual checks. Verify firmware versions, confirm credential changes during onboarding, and run credential-scanning checks on management interfaces. Document findings and assign owners for remediation.
Run a quick scan of devices’ admin pages to see if credentials were updated during setup.
What are best practices to prevent default passwords?
Enforce a policy that forbids default credentials for new devices, automate credential changes at provisioning, enable MFA where available, and maintain ongoing monitoring for credential drift. Regular training for admins reinforces these practices.
Use a proactive policy, automate credential changes, and keep security training current.
Should I reset devices to factory settings or just change the password?
If a device is in active use and has never been updated, start with a password change and firmware update. Factory resets are sometimes necessary for devices with compromised credentials or untrusted configurations, but they should be followed by a fresh onboarding with secure credentials.
Change the password first; reset only if you suspect a full compromise or misconfiguration.
Where can I find official guidelines for default password management?
Look for device-specific security guides from vendors, plus general security best practices from reputable sources. Align with your organization’s security policy and regulatory requirements, and consider guidance from industry bodies when available.
Check vendor guides and general security best practices to align with policy.
“Default passwords are a low-friction entry point for attackers. Prioritizing credential changes during onboarding and enforcing automated remediation dramatically reduces exposure.”
Key Takeaways
- Audit devices for default credentials weekly
- Change defaults before deployment and during onboarding
- Automate credential rotation where possible
- Enforce strong, unique credentials across all devices
- The Default Password team recommends regular auditing and centralized remediation