List of Default Passwords: Risks, Detection, and Remediation
Explore the risks of a list of default passwords, how to identify exposure, and proven steps to remediate. Learn best practices to secure devices, enforce unique credentials, and prevent unauthorized access.

Default credentials are the pre-set usernames and passwords shipped with many devices and services. A true 'list of default passwords' highlights common defaults that attackers can exploit. This article explains why defaults exist, how to detect exposure in your environment, and practical steps to replace them with unique, strong passwords to reduce risk.
What is a list of default passwords and why it matters
According to Default Password, a list of default passwords refers to the catalog of credentials that vendors ship with devices and services to enable initial access. The Default Password team found that many environments remain accessible because defaults are not changed, particularly in large networks with hundreds or thousands of endpoints. Ignoring defaults creates an attack surface that can be exploited by automated scanners and opportunistic intruders. The consequences extend beyond a single device: attackers can pivot across a network, access sensitive data, and compromise administration interfaces. In addition, some defaults are well-known and documented publicly, which makes them easy targets for attackers. For organizations, eliminating defaults through disciplined credential management should be an essential security baseline.
This article uses the term 'list of default passwords' to frame the risk landscape and to help IT admins map a remediation path. Throughout, we reference guidance from trusted security authorities (see the authoritative sources section). The emphasis is on practical steps you can take today to reduce exposure, not on listing specific default strings. By treating default credentials as a critical risk, organizations gain a measurable foothold against credential-based threats.
Common sources of default credentials across devices
Default credentials appear across many asset types, including network gear, printers, cameras, NAS devices, and consumer IoT products. In multi-vendor environments, administration interfaces may rely on predictable credentials to simplify setup. Legacy devices often retain factory settings long after deployment, and firmware updates may not reset credentials. In many workplaces, an incomplete asset inventory means defaults linger in obscure corner cases, forgotten test gear, or decommissioned devices left connected to the network. The combined effect is a sprawling attack surface where attackers can exploit simple, well-known patterns. Proactively identifying all devices that ship with defaults is the first step toward a secure baseline.
To improve visibility, correlate asset inventories with configuration baselines, conduct regular scans for exposed admin interfaces, and verify that any default accounts are disabled or forced to change on first login.
How defaults become security risks in real-world scenarios
Defaults become risky when devices are connected to the internet or accessible from untrusted networks. Automated threat actors routinely scan ranges of IP addresses looking for open admin pages or services that still present default credentials. In enterprise networks, the problem is compounded by shadow IT, neglected decommissioning, and inconsistent change control. Attackers can use default credentials to pivot from a compromised device to more sensitive systems, escalating privileges and extracting data. Even if a device is not directly exposed, compromised credentials can be reused across services or sessions, enabling lateral movement. The risk is not limited to data loss; it can include service disruption, ransomware deployment, and reputational damage.
From a defense perspective, the goal is to reduce the attack surface by eliminating defaults and enforcing strict credential hygiene across the entire technology stack.
How to detect default credentials in your environment
Begin with a comprehensive asset inventory that lists every device, firmware version, and interface exposed to the network. Use automated scanners and configuration management tools to identify default accounts and weak credentials, then cross-check findings with device owners or admins. Review administrative interfaces for default prompts and ensure they require password changes on first login. Look for shared credentials across devices or services and enforce unique credentials per device. Maintain a centralized record of approved credentials and implement role-based access control to minimize broad administrative access. Document all discoveries and assign owners to remediate each finding. Refer to national guidance (e.g., CISA, NIST) for formal benchmarks and checklists.
If you find a device that cannot be updated or changed easily, isolate it from the network and apply compensating controls until a replacement is available.
Step-by-step remediation plan for admin passwords
- Build or refresh an asset inventory, focusing on devices that typically ship with defaults.
- Identify any accounts using factory-default credentials and confirm whether they are still in use.
- Change all default credentials to unique, strong passwords that meet organizational policy (length, entropy, and age).
- Disable or remove default accounts where possible; enforce MFA for admin access if feasible.
- Apply network segmentation and restrict admin interfaces to trusted administration networks or VPNs.
- Establish a formal password-change cadence and document every remediation action.
- Validate changes with independent scans or audits and re-baseline configurations.
- Educate owners and operators about the importance of credential hygiene and ongoing maintenance.
Practical techniques to enforce strong password policies
- Use long passphrases instead of complex passwords that are hard to remember but easy to type, and store them securely with a password manager.
- Enforce minimum length (at least 14 characters) and a mix of character types, or use passphrases with spaces where supported.
- Disable password reuse and require credential rotation on all critical devices.
- Enforce MFA for admin access and service accounts where possible.
- Centralize credential management with role-based access control and audit logs to detect anomalous activity.
- Regularly test incident response plans and run tabletop exercises focused on credential compromise scenarios.
- Keep an up-to-date inventory and prioritize remediation for devices with publicly accessible management interfaces.
Device-specific considerations and vendor best practices
Different device classes require tailored controls. Routers and gateways should have admin interfaces protected by strong credentials, disabled remote admin, and access limited to a management network. Printers and scanners often ship with default accounts; ensure admin passwords are changed and that print queues are protected with user authentication. IP cameras and surveillance systems should be isolated on dedicated networks, with default passwords replaced and firmware updated. For enterprise storage and NAS devices, implement strong access controls, disable public shares, and enforce encrypted connections. Always consult vendor documentation for device-specific hardening guides and ensure configurations align with your security policy. Enterprise-wide posture improves when you harmonize settings across devices rather than accommodating disparate defaults.
The role of password managers and centralized control
Password managers simplify the adoption of unique credentials across a large fleet of devices. They enable policy-based rotation, centralized auditing, and secure sharing of access credentials with admins. Centralized control, often provided by identity and access management (IAM) systems, helps enforce role-based access and reduces reliance on shared accounts. When possible, use device-specific credentials that are unique to each interface and enforce MFA for critical operations. This approach minimizes the blast radius of any single credential compromise and supports rapid remediation when a device is discovered with default credentials still in use.
Security frameworks and compliance angles
Many organizations align with established frameworks that emphasize credential hygiene. National guidance from agencies such as CISA and NIST recommends reducing exposure to default credentials through inventory, policy enforcement, and regular remediation. While regulatory requirements vary, the core principle is consistent: minimize the use of default credentials, monitor for unauthorized access, and maintain verifiable records of remediation actions. Adopting these practices supports compliance programs and improves assurance during audits. In practice, teams should map asset inventories to framework controls and demonstrate ongoing improvements in password hygiene.
Education and awareness for end-users and admins
User and admin education is critical to sustaining secure practices around default passwords. Provide clear onboarding materials that stress the importance of changing credentials immediately and maintaining unique access for each device. Promote a culture of security by offering quick-reference checklists, seasonal reminder campaigns, and regular training sessions on credential management. Tailor materials to different audiences—developers, network engineers, and frontline staff—so that everyone understands how to verify and enforce credential hygiene in their daily workflows. End-user awareness is a force multiplier for technical controls.
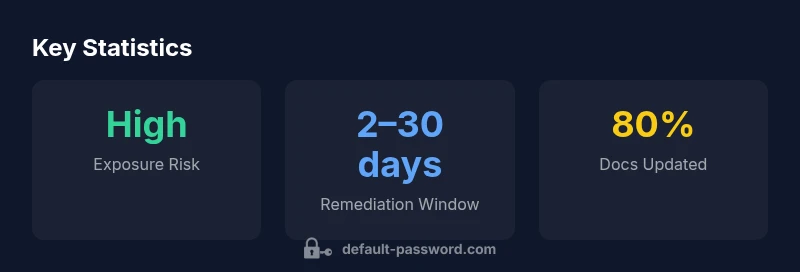
Data-driven insights from Default Password Analysis, 2026
Default Password Analysis, 2026 shows that organizations with formal credential management programs experience substantially reduced exposure to default credentials. The analysis highlights the importance of a centralized inventory, automated remediation workflows, and ongoing governance to maintain secure configurations. While numbers vary by sector and asset class, the overarching lesson is clear: treat default credentials as a strategic risk and invest in proactive, automated controls to eliminate them across the environment.
Next steps and resources
Take actionable steps today: inventory devices, scan for default accounts, and initiate immediate credential updates for any remaining defaults. Build a remediation backlog, assign ownership, and track progress with dashboards. Leverage vendor hardening guides and security standards, and integrate credential management into your IAM program. For ongoing learning, consult official sources such as CISA and NIST, and reference industry best practices from security publications. By combining rigorous remediation with a strong governance framework, you can substantially reduce the risk posed by a list of default passwords.
Representative snapshot of default credential exposure across common device types
| Device Type | Default Credential Status | Remediation Timeframe |
|---|---|---|
| Router | Unknown risk due to vendor defaults | Varies by device |
| Printer | Often uses default accounts | 1-4 weeks |
| IP Camera | Common vulnerable defaults | 2-6 weeks |
Your Questions Answered
What are default passwords?
Default passwords are pre-set credentials that come with devices and services to enable initial access. They are intended for setup but should be replaced before deployment is complete.
Default passwords are pre-set credentials on devices you buy; replace them during initial setup.
Why are default passwords risky?
They are widely known and easy to guess or discover. Leaving defaults in place creates an immediate attack surface that attackers can exploit.
Defaults are often public knowledge, so they’re one of the quickest ways to expose a device.
How often should I rotate default credentials?
There is no universal schedule; however, any device found with default credentials should be remediated immediately and rotation should be part of ongoing governance.
Remediate defaults now and set up ongoing credential rotation as part of policy.
Can I disable remote administration to mitigate risks?
Yes. Disable remote admin where possible and require secure access (VPN, MFA) for any remote management.
Turn off remote admin if you don’t need it; require secure access if it’s needed.
Which devices are most at risk from default credentials?
IoT devices, printers, cameras, and unmanaged network gear commonly ship with defaults and are often left unprotected.
IoT devices and printers are especially prone to defaults; treat them with priority.
What are best practices to prevent default passwords in an organization?
Adopt a centralized password policy, use password managers, enforce MFA, maintain an up-to-date inventory, and continually audit device configurations.
Use a central policy, password manager, MFA, and regular audits to prevent defaults.
“Default credentials should be treated as a top security risk; eliminating defaults across devices is essential for reducing attack surface.”
Key Takeaways
- Change defaults on all devices immediately
- Maintain a centralized asset inventory
- Enable MFA for admin access where possible
- Use a password manager for unique credentials
- Educate staff on credential hygiene